Tag: Security Technologies
How Face Recognition Apps Are Defining The Future Of Competitive Industries?
There has been a lot of talk about Face Recognition Apps recently. It has received accolades for its use in enhancing security as well as flak over privacy concerns. Speculations aside, there is no denying that face recognition software has revolutionized the way we perceive technology. It is no longer a faraway concept as it finds a place in our pockets through mobile technology.
In this blog, we will look at the technology behind face recognition software, what makes it tick and how it has found application across industries.
What Is A Face Recognition App?
Face recognition is a biometric technology that creates a face print of an individual by mapping out his or her facial features mathematically. This face print is stored and used to compare a digital image of a person verifying their identity.
This mapping is done by identifying 80 nodal points on a human face. These nodal points are used to measure different variables of the face. The width of the forehead, the length of the nose, the shape of the eyes – these measurements are captured on a digital image of the person’s face and stored as a face print. Deep learning algorithms are then used to identify a person in comparison with the face print.
This technology has been used in various ways from automatic photo tagging by apps like Facebook for authentication and identification by Apple’s iPhone X. The way in which Apple has used this technology is interesting. Face ID technology, which allows users to unlock their phones using the stored face print, is designed with 3-D modeling. The software compares over 30,000 variables to fine-tune recognition capabilities. This face print or Face ID can be used as authentication for purchases done with Apple Pay and other Apple stores. Amazon Rekognition, Google Cloud Vision API and other image analysis APIs can be now used to add facial recognition capabilities to other applications.
The inclusion of technologies like augmented reality, mixed reality and more have made face recognition software a powerful force. At Fingent, we developed a mixed reality application using Microsoft Hololens. This application helps in the identification of a person and also links the face print to the biodata of the person. It will also be able to capture images and compute similarities between the captured image and all the other images in a secure database.
Read More: The future of communication and security using augmented reality.
The Role of Face Recognition Apps in Safety and Protection
According to a Javelin Strategy and Research study, identity fraud hit a record high with 15.4 million U.S. Victims in 2016 and an increase of 16 percent from previous years. In a connected world where such vulnerabilities exist, face recognition software is proving to be an invaluable asset. The software is helping law enforcement and corporate to put a name to the faces of criminals who have been playing havoc with stolen identities. Some applications of face recognition software in ensuring safety are:
- Identity validation at ATMs and prevention of identity theft with photo IDs.
- Face recognition surveillance systems in schools to protect students from expelled students or parents who have been flagged as dangerous.
- Equipping law enforcement personnel with identification of criminals and contextual data to warn them of dangerous persons before they approach offenders.
- Automated facial recognition (known as AFR) helps in forensic investigations by identifying individuals on surveillance cameras and videos, as well as in recognition of dead/unconscious individuals at crime scenes.
- Protecting retailers from shoplifters by warning security personnel of known criminals with a record. It also helps them avoid potential violence in the store by warning them when dangerous criminals or disgruntled former employees enter.
How Various Industries Can Benefit from Face Recognition Apps
Apart from ensuring safety and prevention of identity theft, face recognition software has many commercial applications as well. Many organizations across industries are recognizing the vast potential of face recognition apps and exploring different ways to capitalize on its features. Let us look at the Healthcare and Retail industries as an example.
Healthcare
Healthcare is constantly making giant strides with technology and facial recognition is contributing in unexpected ways. Researchers from the National Human Genome Research Institute (NHGRI) in the United States have come up with a face recognition system, which can diagnose a rare genetic disease called DiGeorge syndrome. People with this syndrome exhibit particular facial anomalies, which give them characteristic expressions that can be detected by facial recognition software. Despite the many challenges associated with effective detection, the team has developed software with an accuracy of 96.6%.
Another example of face detection software being used in healthcare is the facial recognition app developed by Listerine. This app enables a blind person to detect when somebody is smiling at them, by setting off vibrations when the face recognition app detects a smile. This helps the blind respond better in social situations, thus contributing to their quality of life.
Speaking about the further possibilities that technology can bring to healthcare, Christoffer Nellaker, of the Medical Research Foundation’s Functional Genomics Unit at Oxford says: “A doctor should in the future, anywhere in the world, be able to take a smartphone picture of a patient and run the computer analysis to quickly find out which genetic disorder the person might have”. This is already coming true with the help of face recognition.
Related Reading: Check out how modern healthcare is revolutionizing with automation.
Retail
Retailers have been using augmented reality to improve the customer experience for a while now. The retail giant Sephora has gone one step further and added a live 3D facial recognition feature to its Virtual Artist application. This enables a more accurate facial tracking and rendering, allowing users to virtually try on Sephora’s various products while they are moving in real time. Parham Aarabi, CEO of ModiFace, which is the developer of this function for Sephora says: “We believe the ability to see yourself with products can impact sales online … and thus the integration on Sephora will, based on our expectation, result in increased conversions and user engagement.” The goal with this move is to enable customers to try on their products in a fun and more interactive way. The accuracy enabled by this technology will go a long way in enhancing the customer’s experience and boosting sales.
By using face recognition software in making educated guesses about a potential customer’s gender, age, etc., big retail giants are optimizing their ad campaigns to specific target audiences. Such advertisements are more effective as they help deliver a targeted message that has a powerful effect on consumers. An example is the “Because I’m a Girl” campaign rolled out by children’s charity Plan the UK. The charity created bus billboards, which would scan the viewer’s face and display an ad depending on the viewer’s gender. This was done to highlight the plight of women who are denied rights based on their sex. Brands like Virgin Mobile, Nike and others have also used face recognition software to create a more immersive ad experience for their customers.
Related Reading: Find top ways to leverage smart IT solutions for your retail business.
Implementing Face Recognition Technology
Face recognition software is closer to home than we think, and it is apt to look at ways in which your company can capitalize on its capabilities. Talk to us and let’s discuss how.
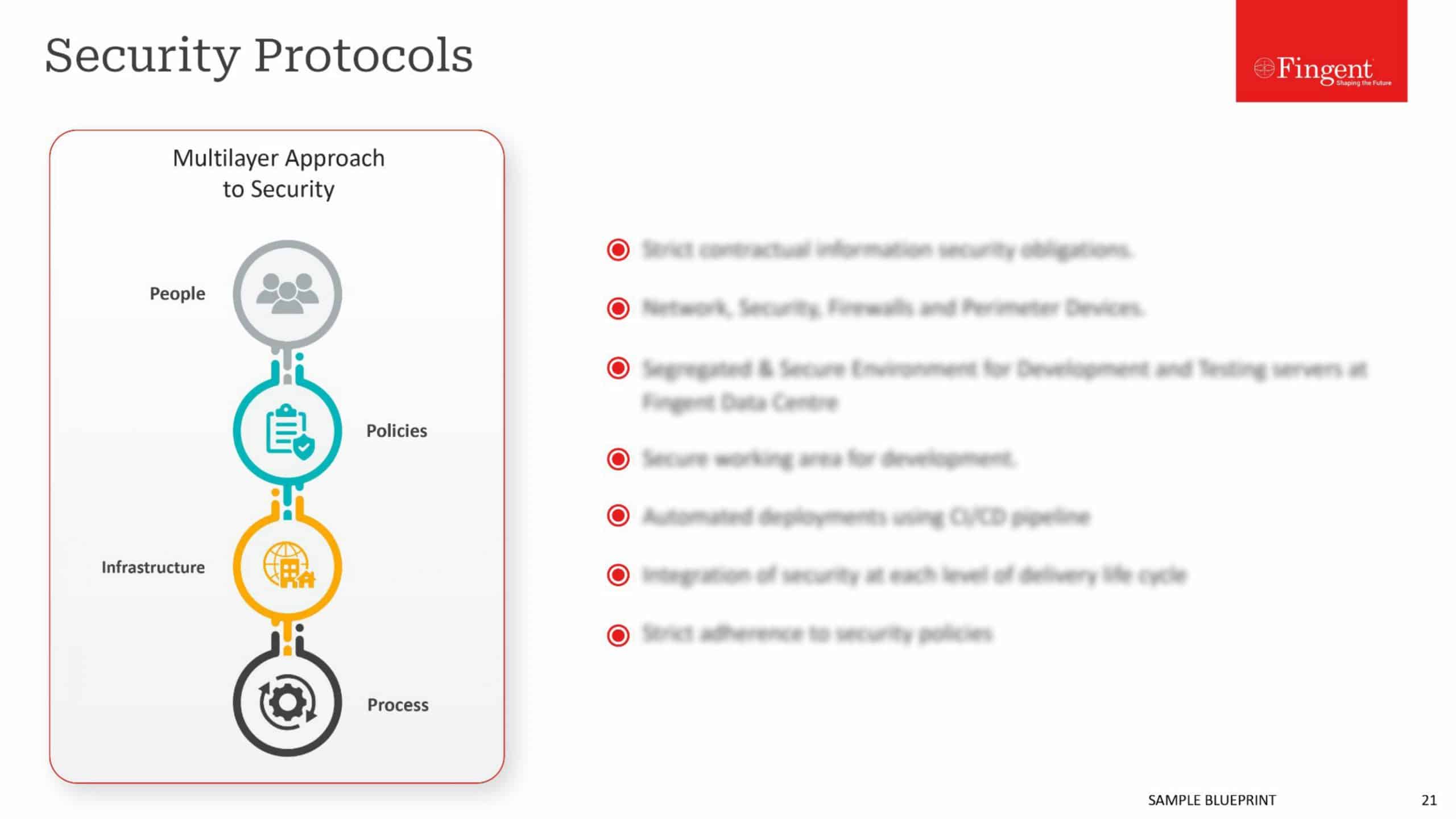
Security remains a key concern in the cyber-space, with cyber-attackers striking at will, limited only by the extent of their determination. Many incumbent security apparatuses have big holes, but the security industry is ever-evolving, constantly adapting to remain one-up on cyber-criminals and offer robust security for new paradigms such as mobile and cloud at the same time.
Here are some of the emerging security technologies to consider for your organization
Newer Malware Detection Models
With many traditional models being an utter flop in preventing cyber-breaches, organizations are looking at newer models to detect malware.
The ingenuity of cyber criminals has rendered the traditional signature-based model of detecting malicious files obsolete. Many organizations now consider other methods, such as machine learning-based mathematical models, or testing suspicious files in a virtual sandbox. Cost-effective SaaS-based security scanning services has also caught on in a big way, considering most attackers target the configuration weakness and code vulnerabilities.
Many security providers offer solutions that fix attribution on attackers and profile them. San Francisco-based Mykonos Software fingerprint cyber criminals based on their intent and skills and inject the attack platform with a token to block future attacks.
Crowd-sourcing is making a mark in security as well. Palo Alto Networks, a Santa Clara, California-based company has pioneered this front with its Wildfire platform that uses a cloud-based malware analysis environment, to share threat information with all subscribers.
Improved Services
Even as some conventional security services has flopped, others such as trust services and encryption retain their relevance. However, these services too are under considerable stress, owing to developments in technology.
IoT boom overwhelms Trust Services with the need to support billions of devices, many with limited processing capability. Some leading-edge approaches adopted by organizations to cope up with the challenge include the use of distributed trust and block chain-like architectures.
Likewise, while full encryption of the data before saving it in the cloud addresses the security needs, it impedes usability. Homomorphic encryption, which allows categorizing and mining encrypted files, is gaining traction now, as a solution.
Erecting Forts
In today’s BYOD era, trying to control the employee’s phone is akin to ordering the tides to go back. Security experts have long realized the more efficient way is to enforce security at the application level, and deploy application containers or wrappers for the purpose.
Likewise, more and more organizations look at hardware isolation to contain attacks. Secure virtual containers are becoming familiar to insulate web browsers, PDF readers, and other executable files. Bromium, a Cupertino, a California-based company has launched a micro-visor that isolates system processes.
Another fortification measure that has caught on is “micro-segmentation,” or more intense granular segmentation of east/west traffic in the networks. Typically, attackers can move around the network at will, once they gain entry. Visualization tools that make explicit flow patterns, and allow admins to set segmentation policies, thwart such free movement and contain the damage to a small area. Point-to-point IPsec tunnels and cryptographic isolation between workloads are some tools that help contain the breach to the particular area, post-visualization.
Deceiving the Deceiver
With perimeter fencing having all but lost the battle to cyber-attackers, more and more organizations now resort to deception.
Deception technology tries to beat malware at its own game, by resorting to various deceptive tricks against it. The most common method is deploying honeypots to create fake vulnerabilities, and lure the attackers into distributed endpoint decoy systems. When the attackers touch an emulator that serves as a honeypot, the security system triggers the alarm.
Gartner predicts about 10% of enterprises to use deception tools and tactics, by 2018.
Dissuading the Attacker
If organizations can identify the motive of the cyber attacker, they can work to remove the motivation, and hence deter the attacker. Most targeted attacks aim to steal intellectual property and other information that has commercial value. Many organizations now indulge in comprehensive risk assessments, to identify tempting targets resident in their systems. They can either beef up security around such critical assets or even take such assets offline.
Denying the Attackers
Organizations now deploy various innovative measures to deny attackers. One measure which has gained considerable traction is remote browsers. Most attacks target end-users with malware-infected URLs, email, and messages. A remote “browser server,” isolates the browsing function from the rest of the endpoint and corporate network, thereby keeping malware off of the end user’s system, and reducing the risk manifold.
Indulging in Deep Profiling
Accenture’s 2013 Technology Vision document is a perfect example of deep authentication, authorizing users based on their location, time of day, and several other factors that make it virtually impossible for even legitimate or familiar users to gain unauthorized access.
Today’s organizations go even beyond, many of them deploying artificial intelligence empowered systems that understand legit users’ daily activity profile, place login attempts in context, and take risk-based decisions in real-time. For instance, an employee who has no business to travel suddenly making a login attempt from Timbuctoo raise a serious red flag, and cause a lock-down.
User and entity behavioral analytics (UEBA) generates deep insights on not just user behavior, but also on endpoints, networks, and applications. Organizations need to factor in such analytics to an intelligence-driven security operations center (SOC) and adopt event-based monitoring in a big way.
Beefing Up the Authentication
Most organizations now employ multi-factor authentication. The password nevertheless remains the primary authentication mechanism. It has been a cat-and-mouse game between security experts and cyber criminals, with the increased complexity of the passwords invariably matched by advancements in password-cracking technologies. Security experts are toying with substituting passwords with biometric authentication methods. Only the difficulty in wrapping hardware and software around biometrics has prevented this move from becoming mainstream.
However, hardware tokens as part of the authentication process are now mainstream. Intel’s new, sixth-generation Core vPro processor offers “Authenticate” solution that validates a user through permutations of various hardware-enhanced factors. Hardware authentication is not just useful to secure traditional endpoints such as laptops and mobiles, but it even more critical in the IoT world, where a network needs to ensure the thing trying to gain access should have access to it.
Deploying the latest technology alone, however, does not guarantee security. Even the best security method falters in isolation. What is needed is a comprehensive analysis and deployment of the appropriate security measures as part of an integrated whole. Get in touch with us for a comprehensive security assessment and implementation of the right security suite, in the right way.