2003
Year of Establishment

100s
of Customers Worldwide

4.9/5
Customer Rating
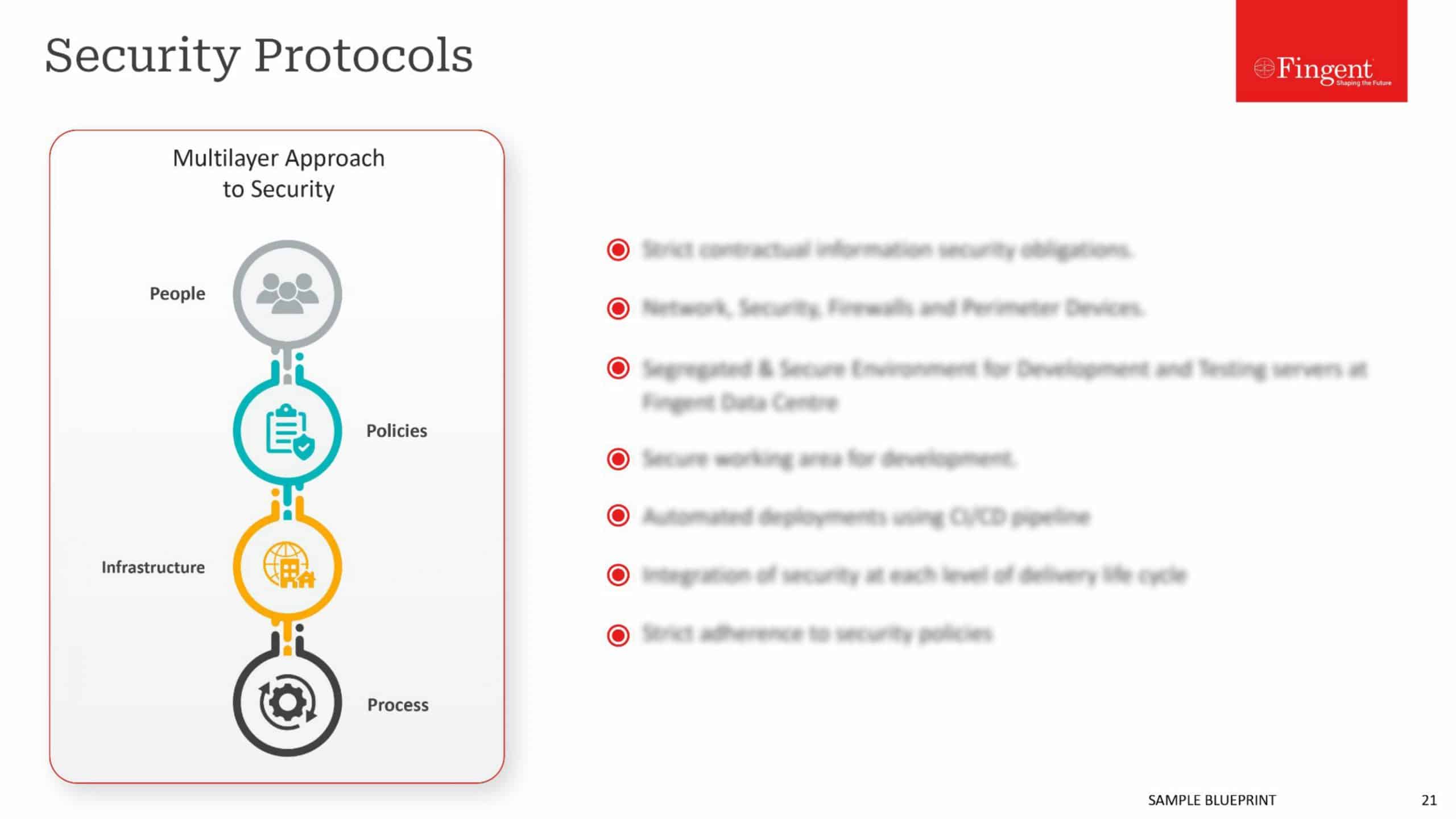
How Fingent Protects Your Business
Network security has grown into an important concept today with multiple devices communicating with each other over wired, wireless, or cellular networks. Every organization must protect its network to successfully deliver the services that their employees and customers demand. By combining multiple layers of defenses at the edge and in the network, we help protect your proprietary information from cyber attacks.
Corporations over the years have realized that Network Outsourcing to best of breed IT service providers like Fingent can yield them significant cost savings and business benefits. Our offerings are conceptualized, implemented and delivered keeping in mind the entire suite of network security services.

Our Network Security Services

Network Consulting, Implementation, and Integration

Network Operations Center

LAN, WAN, and WLAN management

Managed Unified Communications Services

Network Consulting, Implementation, and Integration
Using hybrid cloud and IT as a Service deployment, we help you assess, design and plan a dynamic network aligned to your IT and application needs. Our network consulting, implementation and integration services help unify your network infrastructure and make way for new technologies like SDN, NFV and more. We help strengthen your network security capabilities with IPS, IDS, URL Filtering, AMP, and AVC features.

Network Operations Center
Our IT support technicians supervise, monitor and maintain client networks through a network operations center that provides firewall and intrusion prevention systems, network discovery and assessments, patch management and whitelisting, performance reporting, backup and storage, email management, application software installations, troubleshooting and updating, policy enforcement, and other critical network security services.

LAN, WAN, and WLAN management
Fingent partners with leading networking equipment suppliers to deliver tailored services to our users. We can help you with WAN, LAN, and WLAN solutions so that you have a secure, fast and cost-effective working environment regardless of your requirements. We also monitor and manage customer-owned IT infrastructure on a global scale and leverage predictive network analytics to identify potential network issues before they impact crucial operations.

Managed Unified Communications Services
The communication environment of enterprises is highly fragmented with multiple service networks and differing solutions for voice, video, contact center, and collaboration. Fingent’s unified communications management spans voice/IP telephony, voicemail, IVR, messaging, multimedia conferencing, contact center, support for connectivity, and business analytics. Partner with us to deploy advanced collaboration technologies to drive enterprise productivity.
Why Leading Companies Trust Our Security Solutions
Consistent high-quality results with a robust agile team and a dedicated QA practice
Highly cost-effective and best-of-breed solution with no last minute surprises
Transparent project management with maximum adherence to deadlines
Our Unique Approach & Process
By initiating your project with Fingent, you get a dedicated and skilled team backing you up round-the-clock. All our processes are customer-oriented, designed to reduce the cost of business operations, address IT resourcing challenges, and offer you a competitive edge. We start with a deep analysis of your requirements and continue our relationship with post-launch support and updates.
1
Research and Discovery
2
Validating and Shaping Idea
3
Design and Prototyping
4
Development
5
Testing and Quality Assurance
6
Maintenance and Support
Contact Us
Hundreds of leading businesses have derived strategic advantages from our transformative solutions.
The entire engagement was completely transparent and very systematic. It’s been an exceptional working experience.
Their team is completely committed to our success as a client, and they do that with their dynamic team.
They’ve also been great at meeting the needs of our timeframe versus theirs.
They go above and beyond what the typical developer interaction would be.
They were highly responsive to our needs.
We found their project management solid.
Reviews from engineers testify that their code was consistently solid and comprehensively documented.
I have been very pleased with Fingent Corporation’s user experience and design capabilities.
Fingent’s project team demonstrated passion and commitment throughout the dev cycle and it was very evident in their work.
They’re an honest company to deal with … they were always fair and reasonable.
FAQs
The common types of network security are:
- Antivirus and Antimalware Software
- Application Security
- Behavioral Analytics
- Data Loss Prevention (DLP)
- Email Security
- Firewalls
- Mobile Device Security
- Network Segmentation
- Security Information and Event Management (SIEM)
- Virtual Private Network (VPN)
- Web Security
- Wireless Security
- Endpoint Security
- Network Access Control (NAC)
Network security helps you protect your proprietary information from cyber attacks. It allows you to take preventative measures to secure your organization’s networking infrastructure from unauthorized access, misuse, malfunction, modification, destruction or improper disclosure. By implementing network security measures, your users, computers, devices, and programs can perform their authorized critical functions within a secured environment.
Security analytics is a cybersecurity approach that aims to take proactive security measures based on the analysis of data. Incredible amounts of data keep passing through your network continuously. In such scenarios, your security appliances like firewalls or Intrusion Detection Systems get only limited time to inspect the traffic flowing through your network. This is where network security analytics can help you.
Network security analytics broadly comprises the tools, technologies, and methodologies that make use of data science techniques such as statistical analysis and pattern detection for network security risk management.
Intrusion Prevention System (IPS) is a kind of network security that continuously monitors your network to detect and prevent identified threats. An IPS system captures information on any malicious incidents and reports the events to system administrators who can take preventive actions to defend any cyber attacks. IPS is placed in between the direct communication path between the source and destination so that it can actively analyze and take automated actions on the traffic flowing through the network.
VPN or Virtual Private Network extends a private network across a public network. It allows you to create a virtual private network from a public internet connection by masking your internet protocol so that your online activities are virtually untraceable. VPN protects your online activities such as shopping, emails, bills, and payment transactions using encryption and anonymity, and makes your web surfing anonymous.
Network segmentation is intended to improve network performance and security. It works by dividing or segmenting a computer network into smaller parts so that an organization can control how traffic flows across each part of your network. You can restrict or define the traffic flow based on the traffic type, source, destination, and other criteria. Segmentation reduces network congestion, restricts the damage caused by cyberattacks, protects vulnerable devices, and minimizes the costs associated with regulatory compliance.