2003
Year of Establishment

100s
of Customers Worldwide

4.9/5
Customer Rating
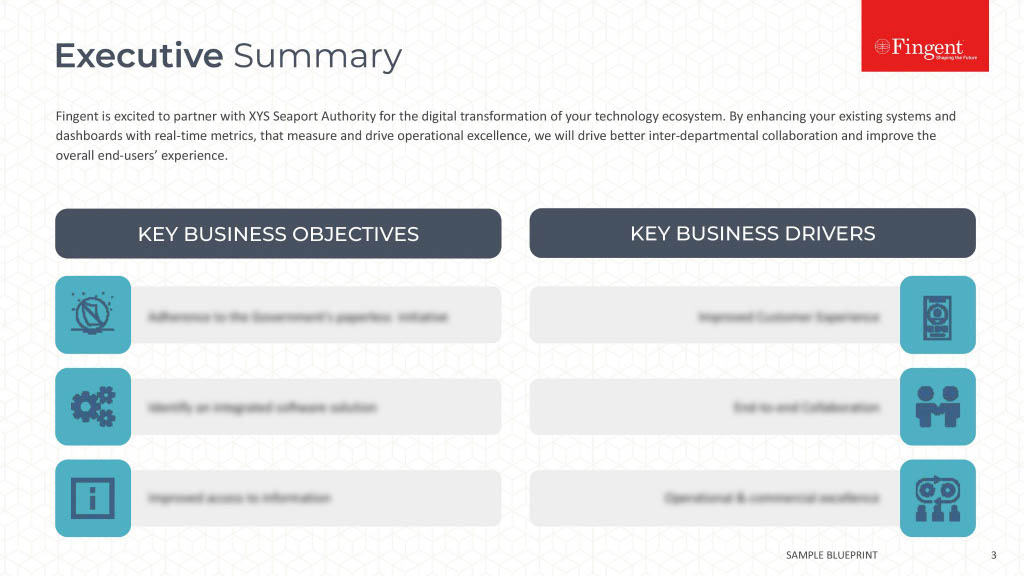
How Fingent Helps
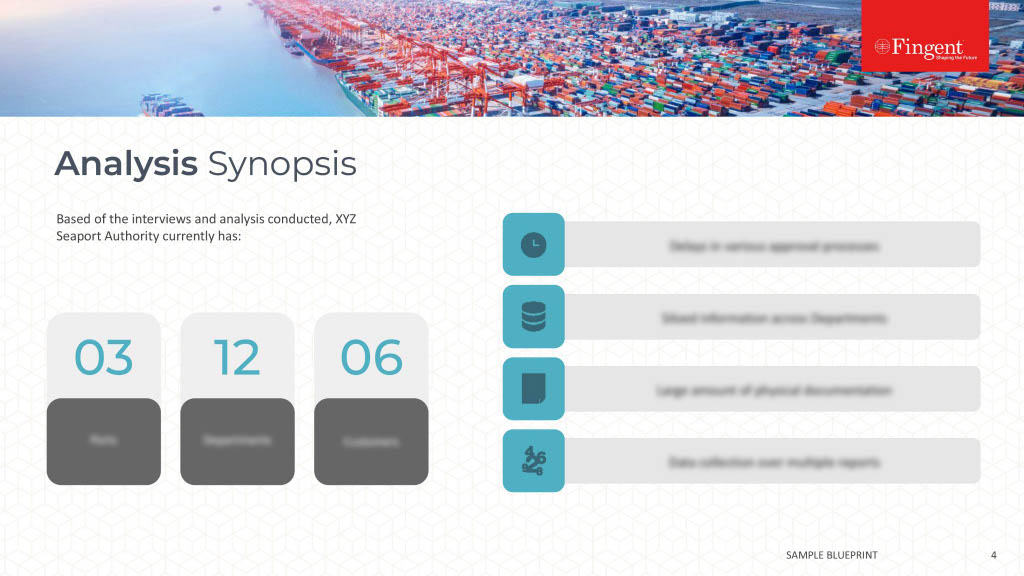
Cyberattacks on critical infrastructure have become increasingly complex and disruptive. Data breaches and even complete system shutdowns have been achieved of these formidable cyber foes, resulting in loss of revenue and damaged reputations.
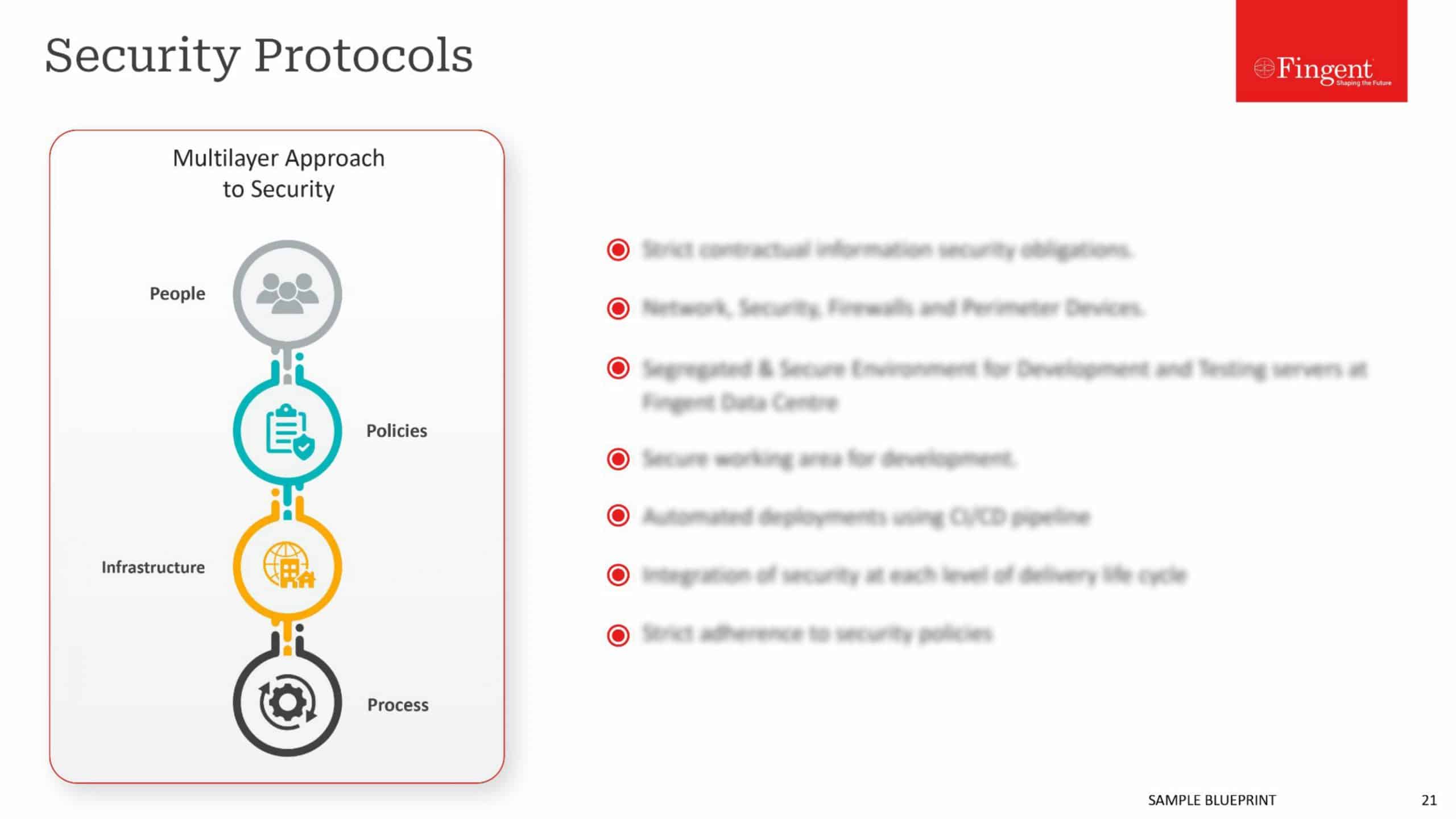
Our strategic approach towards infrastructure security limits the vulnerabilities of these systems and builds up cyber resilience to protect your business against contamination and sabotage. We help you build a robust and impenetrable security structure across all your multi-cloud environments.

Our Infrastructure Security Services

Aggressive Defense Strategy

Instant Response to Threats

Exposing Risk Through Visibility

Building Resilience Against attacks

Aggressive Defense Strategy
We constantly apply our infrastructure security capabilities to find and address vulnerabilities before they impact your business and your customers. We support quick mobilization of your workforce and the digitalization of your business by optimizing security tools and deploying next-generation defenses.

Instant Response to Threats
Our technology can monitor your servers, enabling you to spot abnormal behavior as soon as it appears. It thus eliminates the need for a scheduled scan and can quickly identify the threat and contain it before it moves laterally across your infrastructure.

Exposing Risk Through Visibility
Identifying abnormal behavior and obtaining visibility into the number of smart devices connected to the infrastructure can reduce the risk of a cyberattack. We give you consolidated visibility across multiple networks to help your security teams respond swiftly.

Building Resilience Against attacks
We provide you with a range of security services that guard your business software and hardware systems. By maintaining firewalls and monitoring network traffic, we help you maintain the continuity and compliance of your business.
Why Industry Leaders Trust Our Security Solutions
Consistent high-quality results with robust agile teams and dedicated QA practices
Highly cost-effective and best-of-breed solutions with no last minute surprises
Transparent project management with maximum adherence to deadlines
Our Unique Approach & Process
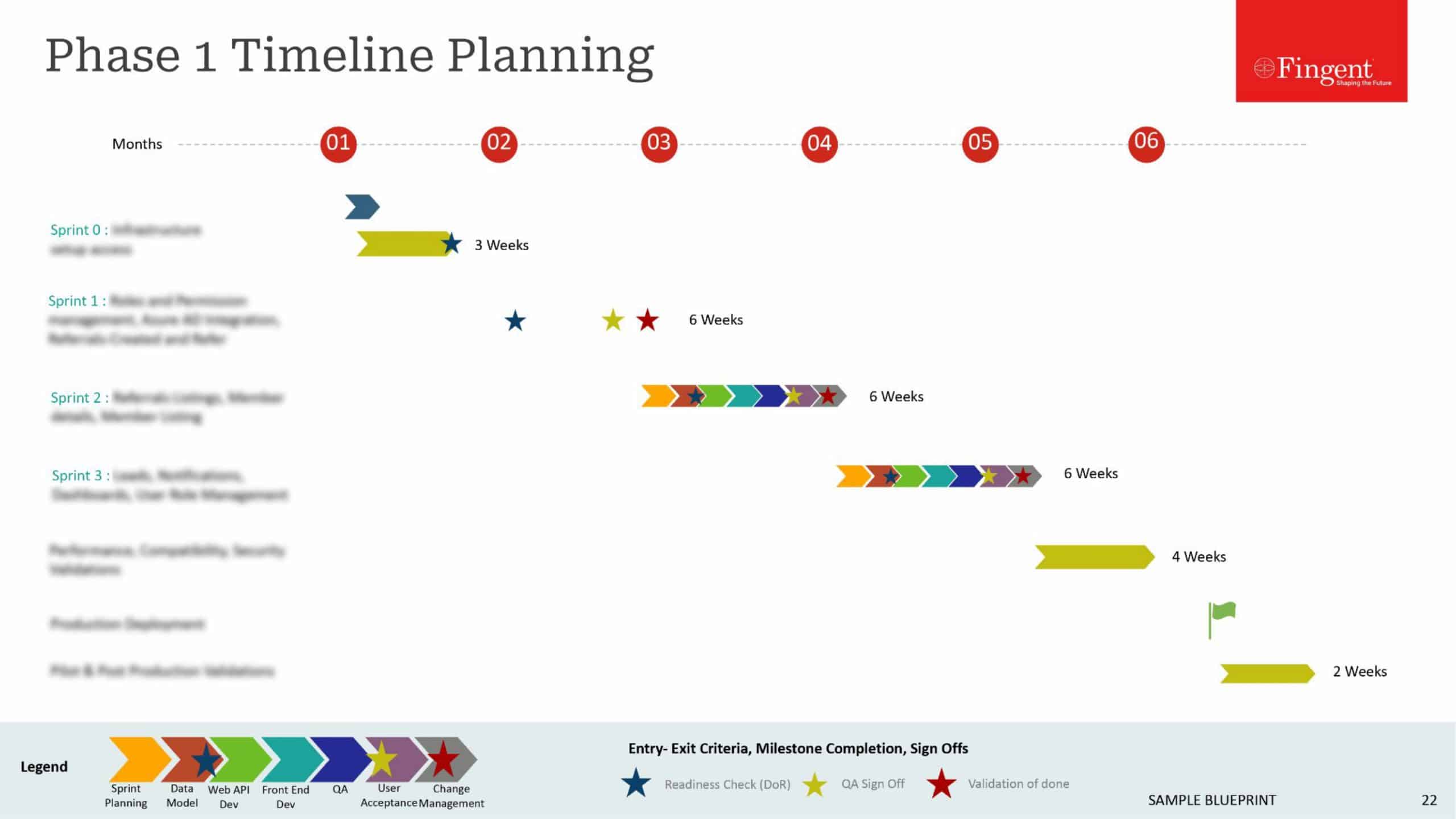
By initiating your project with Fingent, you get a dedicated and skilled team backing you up round-the-clock. All our processes are customer-oriented, designed to reduce the cost of business operations, address IT resourcing challenges, and offer you a competitive edge. We start with a deep analysis of your requirements and continue our relationship with post-launch support and updates.
1
Research and Discovery
2
Validating and Shaping Idea
3
Design and Prototyping
4
Development
5
Testing and Quality Assurance
6
Maintenance and Support
Contact Us
Hundreds of leading businesses have derived strategic advantages from our transformative solutions.
The entire engagement was completely transparent and very systematic. It’s been an exceptional working experience.
Their team is completely committed to our success as a client, and they do that with their dynamic team.
They’ve also been great at meeting the needs of our timeframe versus theirs.
They go above and beyond what the typical developer interaction would be.
They were highly responsive to our needs.
We found their project management solid.
Reviews from engineers testify that their code was consistently solid and comprehensively documented.
I have been very pleased with Fingent Corporation’s user experience and design capabilities.
Fingent’s project team demonstrated passion and commitment throughout the dev cycle and it was very evident in their work.
They’re an honest company to deal with … they were always fair and reasonable.
FAQs
Your infrastructure is an integral part of your business and its functioning. It comprises your IT systems including both hardware and software systems. With security breaches and other threats on the increase, your infrastructure is at constant risk. These threats are real and can cause major outages.
These are security systems set in place to limit the vulnerability of critical infrastructure. This requires integrating security into mainstream organizational management and processes. Threat prevention, Data Governance, Data Encryption, Firewall Solutions, Intrusion Prevention and other aspects come into play in the execution of Infrastructure Security.
Data theft or manipulation by bypassing in-built access permissions, unauthorized access to terminals or systems, sabotage by ex-employees, information warfare for private gain, and so on.
Many businesses might rely on their IT teams to provide infrastructure security. But practically, IT teams seldom have the special skills required or the time and manpower to proactively deal with security threats. Using an external security partner to plan and maintain your security solutions gives you a hassle-free and effective strategy to secure your systems.
Broadcom Inc. reports that in 2015, over 43 percent of cyberattacks were done on small businesses. Hence, the benefits of investing in an external infrastructure partner are numerous. All businesses should approach their security policies like they do any investment: long-term with quantifiable goals.
The first and foremost is that it protects your most valuable business assets, such as your customer data. It builds client and customer trust which in effect has a direct bearing on your company’s reputation. It reduces security threats of an internal and external nature and bolsters regulatory compliance at every level. Most importantly, it gives business owners the peace of mind that they are doing all they can to be secure and successful. Choosing to invest in infrastructure security translates into investing in your company’s future.