Tag: software development security
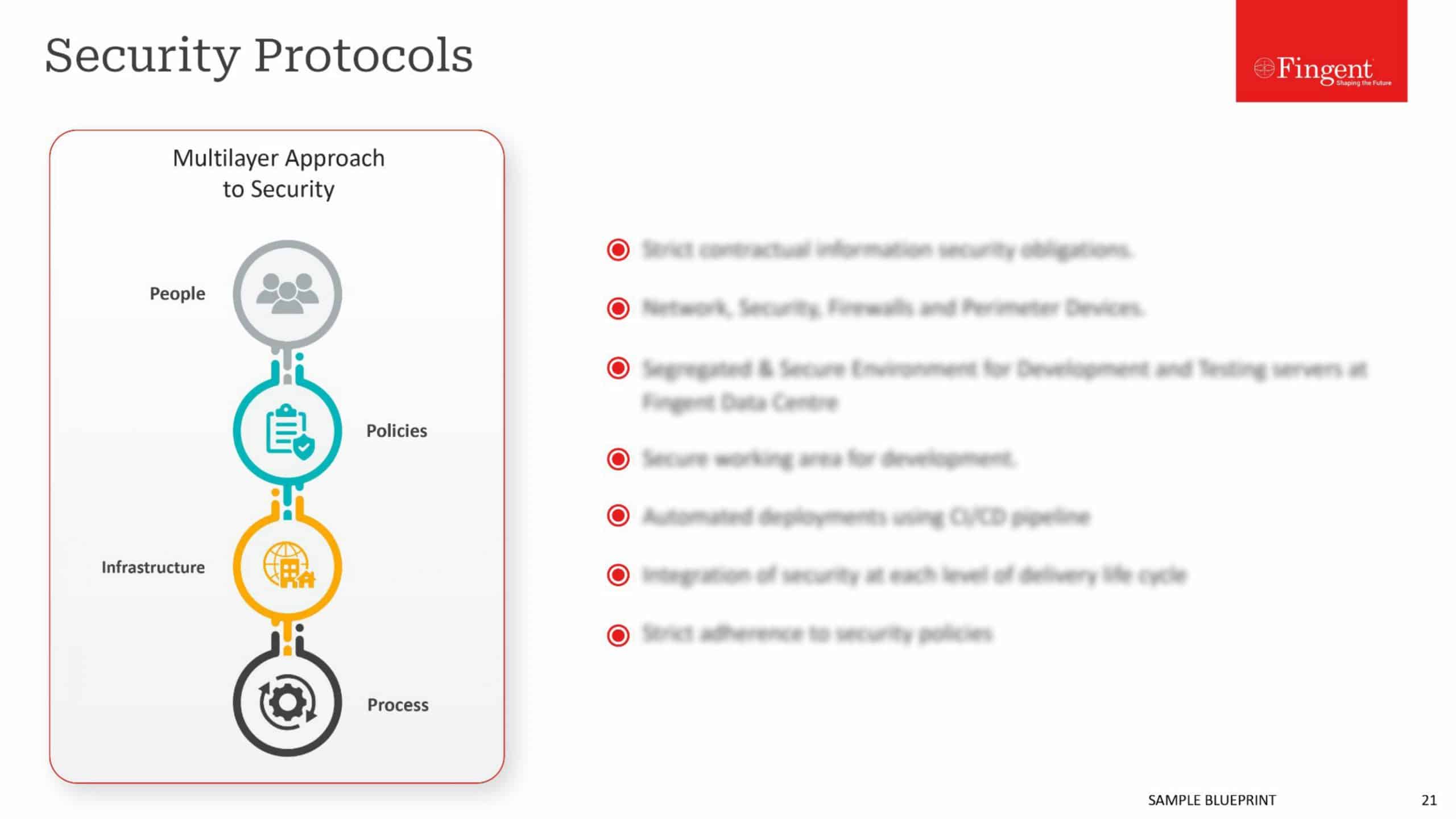
The more advanced the technology, greater the security risks. Instances of cyber breaches, ranging from hackers stealing consumer’s bank account to hacking nuclear power plants, are all too commonplace. It comes as no surprise many CIOs rank cyber security as their number one challenge.
Trying to keep cyber attackers at bay by fortifying perimeter security, or adding extra layers is trying to fight the sea waves. It has been proved again and again that it is only a matter of time before cyber criminals get one-up on whatever new approach security experts throw at them. Many of the hackers represent the best brains in the industry, and many of them are actually in for some cause and display missionary zeal to breach networks. Such forces are unstoppable, as even Fortune 500 firms have found out the hard way over the last decade.
In such a state of affairs, the only effective approach is incorporating security with the system, by ensuring the code is impeccable. Cyber attackers exploit some latent vulnerability in the code, to launch an attack. If they are no vulnerability, the code cannot be breached. A tight-knit code, with no vulnerabilities, shuts the door firmly on attackers and eliminates the major source of the breach.
The State of Vulnerabilities
Ensuring tight-knit security within the system by testing the code for vulnerabilities and flaws is an indispensable best practice, regardless of the nature of the software, or the size of the enterprise.
The reality on the ground is markedly different, though. A September 2016 survey by Veracode reveals 83% of cyber experts releasing code before testing or even before resolving known bugs and other security issues. A March 2015 IBM report reveals one in every three enterprises do not even bother to subject their mobile apps to testing for security vulnerabilities, before rolling it out in the market.
The obvious reason is competitive pressures in a fast-paced business environment, where even a few days delay in launching an app can have an adverse impact on its adoption and success. Most enterprises who compromise testing evaluate the time taken for testing would defeat the very purpose of rolling out the app in the first place.
Another reason for short-cuts on testing is the severe skill shortage. Lack of talented hands with the ability to conduct the process with aplomb force many enterprises into compromises.
Such short-cuts and omissions are a mistake but are the practical reality. Success does not come by wishing away the reality, but accepting it, and doing something to counter it. Here are some tips in this direction.
Integrate Security into the Design
Security did not have a place in the traditional software development model and was actually included as an afterthought when breaches started to cause serious damage. Changing this model is the key towards ensuring effective security.
As the adage goes, “you can’t protect what you don’t understand.” The basic requirement is understanding the system, as in how existing components and systems communicate with one another, a map of the workflow, a review of past incidents and most likely attack vectors, and more. Such information helps the development team understand the key elements and assets to protect, and devise ways to thwart potential attacks on the system.
For instance, a new e-commerce site will invariably feature an UI for end-user interaction, a set of services where the business logic will reside and a data store. When the user submits a form through the UI, the data moves from a user-controlled environment to a trusted server. Smart developers identify a trust boundary at this point and take effective precautions such as modeling threats or codifying validations.
Develop a baseline security standard based on standards like ASVS, and use threat modeling tools to identify additional vulnerabilities unique to the system.
Cross-Check the Code
Co-opting security into the software development model requires testing for code integrity early and often, as opposed to penetration testing at the end of the process to catch bugs.
The practice is catching on. A December 2016 Veradode survey reveals 40% of developers incorporating securing testing during programming stage itself and 21% at the design stage. Identifying and eliminating bugs, glitches, and vulnerabilities at the development stage itself make it that much easier, simpler, and less costly to eliminate the same, and do not leave any window for attackers to exploit the vulnerability before it is identified. Developers could use a combination of static application security testing tools and dynamic application security testing technologies, or even visual testing at the development stage.
Post Production Initiatives
Despite the best of precautions, there is always a chance of some vulnerabilities slipping through the net. Some vulnerabilities may not manifest itself until the software gets active, and interacts with its ecosystem.
Static and dynamic analysis tools help identify vulnerabilities missed during development and testing. Automated checks for libraries that require updating is also fairly simple to include.
Deploying a group of ethical hackers, such as IBM X-Force Red, is another approach to discover and fix bugs in a proactive manner before the bad guys discover the bugs first.
The importance of software developers as the first and most effective line of defense against cyber-attacks can never be understated. For this reason, a credible partner who has considerable experience in delivering highly robust and secure apps, and who have the talent and expertise to combine innovation and best practice in the most optimal way, can give a big fillip to your enterprise security. With our uncompromising approach to quality and backed by a highly competent and talented team, you can rest assure the solutions we deliver are as secure as it comes. Partner with us to ensure your code is robust and secure in all aspects, and security vulnerabilities do not wreck your business.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new