How Business is Adapting to the Next level of Mobility in The Hyper-Connected World
Employees and other key stakeholders of a business now expect seamless, ‘always-on’ mobile connectivity from the device of their choice. Work processes are now built around mobility, and a throwback to the “stone age” of communications is unthinkable. Enterprises not providing enterprise solutions based on hyper-connectivity not only miss out on seizing the business moment, but also face the risk of top talent leaving to better “digital” pastures.
Most enterprises play to the gallery. The latest smartphones come with several advanced features enabling asset tagging, image building and management, RFID/UID tagging, laser engraving, custom labeling and packaging, knitting or reverse kit solutions, and several other possibilities not easily doable before.
Wearables leverage features such as the accelerometer, barometer, gyro, ambient light, barometer, altimeter and other key features to automate key tasks, issue timely alerts, and more, without any action from the user. Such devices, and mobility solutions leveraging such devices, already play a critical role in inventory planning, field collaboration, strategic analysis, and several other functions of the enterprise. Businesses leveraging such latest technology to offer cutting edge enterprise solutions can expect to ride the digital wave to success.
However, much more is required, to sustain the success. As it is with technology, mobility is in a state of continuous flux. New technologies such as Augmented Reality and Internet of Things promising to take connectivity to whole new levels. Businesses have no option but to keep track of the latest developments, and they also need to take a few other coherent steps to ensure they deliver the goods in today’s hyper-connected world.
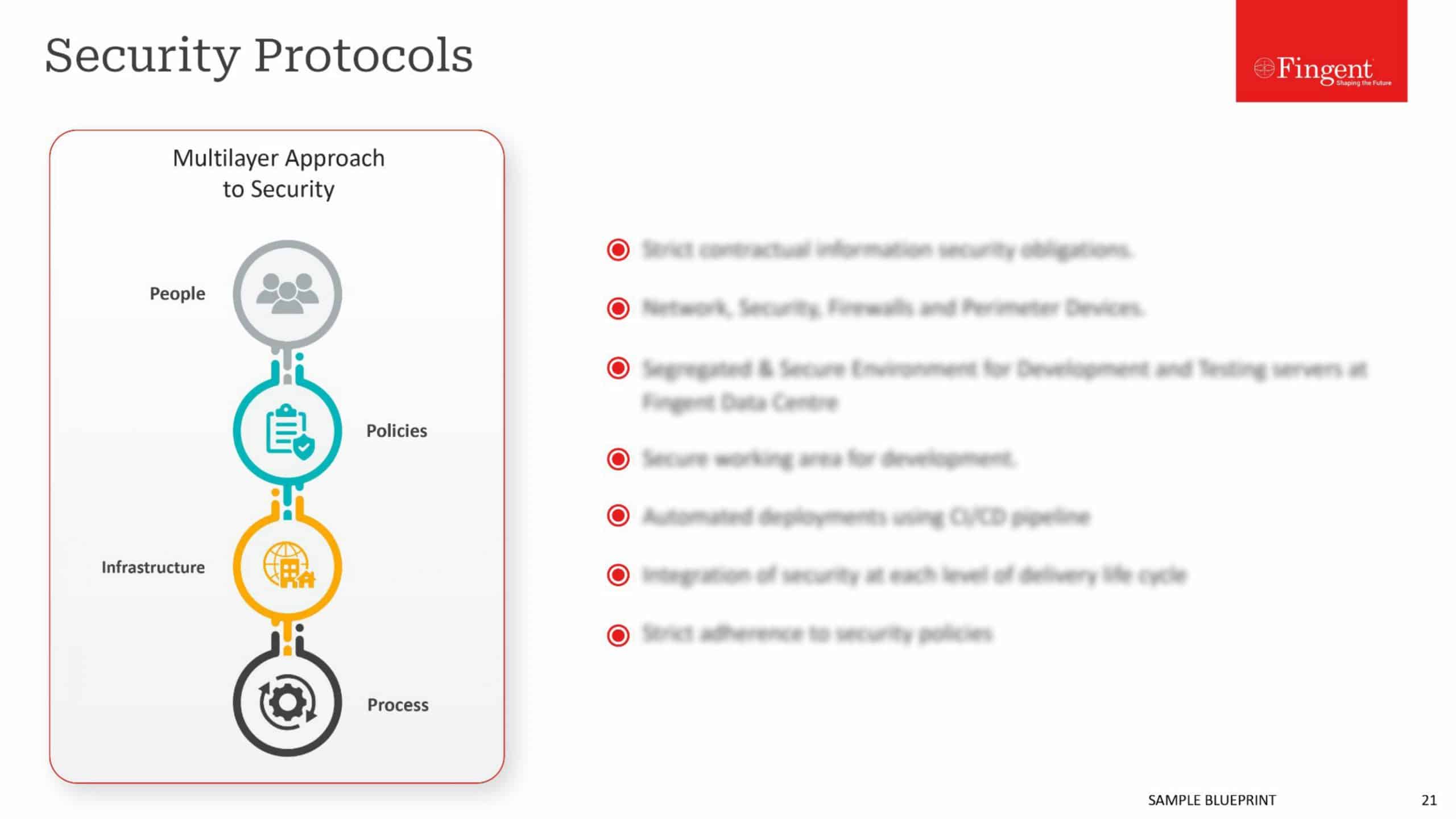
Pay Attention to All Round Security
Safe and reliable connectivity is the basic objective of any mobility strategy. Enterprises ignore network security at their own peril, but many enterprises also make the mistake of limiting security to protecting the device or strengthening the firewall. Managing access is just as important and many enterprises underestimate the potential vulnerabilities on offer in this front.

Today’s users access mobility solutions through wi-fi, Bluetooth, SMS, email, or other options available in the device. The coming Internet of Things will expand such options. With such wide options come wide threats. Each of these connectivity options is a potential threat vector, which an enterprising attacker could leverage to breach the network. Enterprises need to establish policies that cover various aspects and implications of connectivity, as in the security implications when accessing the corporate network from public wi-fi available at Starbucks and other places, data retention when connectivity is disrupted or intermittent, implications of sensitive data being siphoned off by hackers who take advantage of Bluetooth technology, and more. Effective security now requires not just macro level provisioning but also paying attention to details.
Take Stock of BYOD Challenges
Bring-your-own-device (BYOD), a norm in many enterprises, is a double-edged sword. It is a win-win in the sense it spares the enterprise from the investment in procuring handsets, and it offers employees the convenience of carrying around just one device. However, it also poses grave security implications, when employees use their device for personal purposes.
BYOD is sure to subvert the enterprise network unless strong security policies are in place to ensure the employee’s personal activities do not encroach on the corporate assets in the phone. Containerization separates personal data from corporate data and is the preferred option in most mobile device management approaches. The “enterprise wipe” removes data from the corporate container, handy when the employee leaves the enterprise or turns rogue. MDM solutions enable effective enforcement of all corporate policies on company and BYOD devices.
There is also the issue of platform fragmentation, with enterprises having to roll out apps for Android, iOS, and Windows, and cater to different device configurations. Even without BYOD, enterprises need to take the decision on which platforms to support upfront.
Deploy the Required Infrastructure
Effective policies require backup in the form of adequate infrastructure. Evaluate the quality of the existing infrastructure by conducting wireless surveys, gap analysis, and other methods, to ascertain the gap between the present and the desired state, and work to provisioning for the ideal state. Some areas where infrastructure usually requires ramp-up for mobility include ingress/egress infrastructure, the number of points on the network, bandwidth capabilities, network segmentation, switching, and routing capabilities. Make sure the provisioned infrastructure is scalable.
Apart from the technical backbone to run mobility solutions seamlessly, there is a need for robust development infrastructure as well. Developing mobility solutions is now a cross-functional team effort, with members from different backgrounds heavily involved in all stages of the development process. It requires a culture of collaboration, backed up by adequate infrastructure such as project wise Git repository, coordinated workflow, development tools such as native SDKs, hybrid Apache Cordova, HTML5, Sencha, Xamarin, Appcelerator, or any other tool, as appropriate. The best practice is to use open and cloud-based technologies, with an emphasis on reusability, collaboration, and scalability, as this perfectly complements sustainable innovation, so essential to keep pace with things.
Enterprises also require flexible and easy-to-deploy solutions to secure apps and deliver data in a secure manner. The best solutions virtualize and pool compute, storage, and network resources, and ensure rapid assignment and deployment, as needed. Enterprise solutions build on hyper-convergence is the way to go in an increasingly connected world.
It requires both skill and experience to deploy an effective mobility strategy that enables the enterprise to leverage the latest mobility must offer. The internal IT team may be handicapped in this regard, and would anyway have their hands full with keeping the system running. Often, roping in a strategic partner works wonders to implement an effective mobility policy. Opt for partners who work with the enterprise, understand the requirement, and offer customized solutions rather than try to push generic solutions they already have.
Stay up to date on what's new

Recommended Posts

25 Aug 2020
Why It’s Time to Embrace Cloud and Mobility Trends To Recession-Proof Your Business?
Cloud and Mobility: The two pillars to recession-proof your business Introduction How Does the Recovery Shape of The Coronavirus Recession Look? What is a recession-proof business? What can business……

19 May 2017 Retail
Mobile Connectivity Issues: The Hidden Danger Subverting Enterprise Mobility
The need for remote connectivity is growing day by day, as the ranks of the mobile workforce swell. While enterprises are busy rolling out mobile apps to facilitate the mobile……
08 May 2017
Native Apps vs Web Apps: Choosing the Best For Your Brand
Mobility is growing at an exponential pace and mobility apps are the flavor of the season. However, it is still important to get the development right, to reap the benefits……

04 May 2017
Enterprise Mobility: Practical Strategies to get rid of Paperwork
Paperwork is the bane of most enterprises seeking productivity and efficiency improvements, to reduce their operational costs and become more competitive. While a certain amount of paperwork remains inevitable owing……
Featured Blogs
Stay up to date on
what's new