How Secure is Your Business in a Multi-Cloud Environment
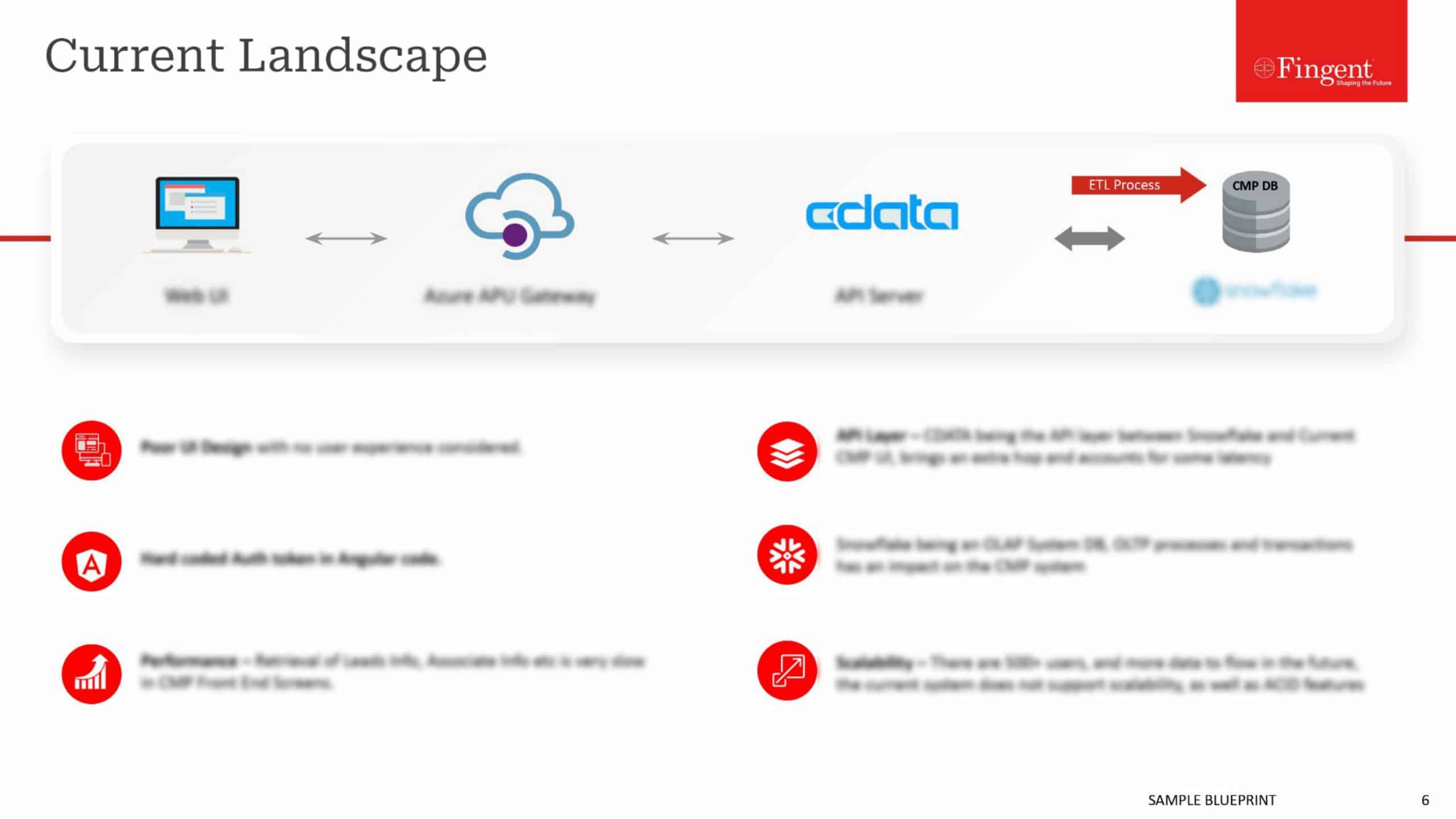
Cloud computing refers to the method of computing in which an interconnected network of remote servers is utilized for the execution of the operations such as storage, management, and processing of information. The business units in the current era are making use of multiple cloud computing services and techniques in an integrated architecture. There are various deployment and delivery models of the cloud which are amalgamated as one unit for the execution of business processes and activities. However, with the expansion of such practices, there are some security issues that have been observed.
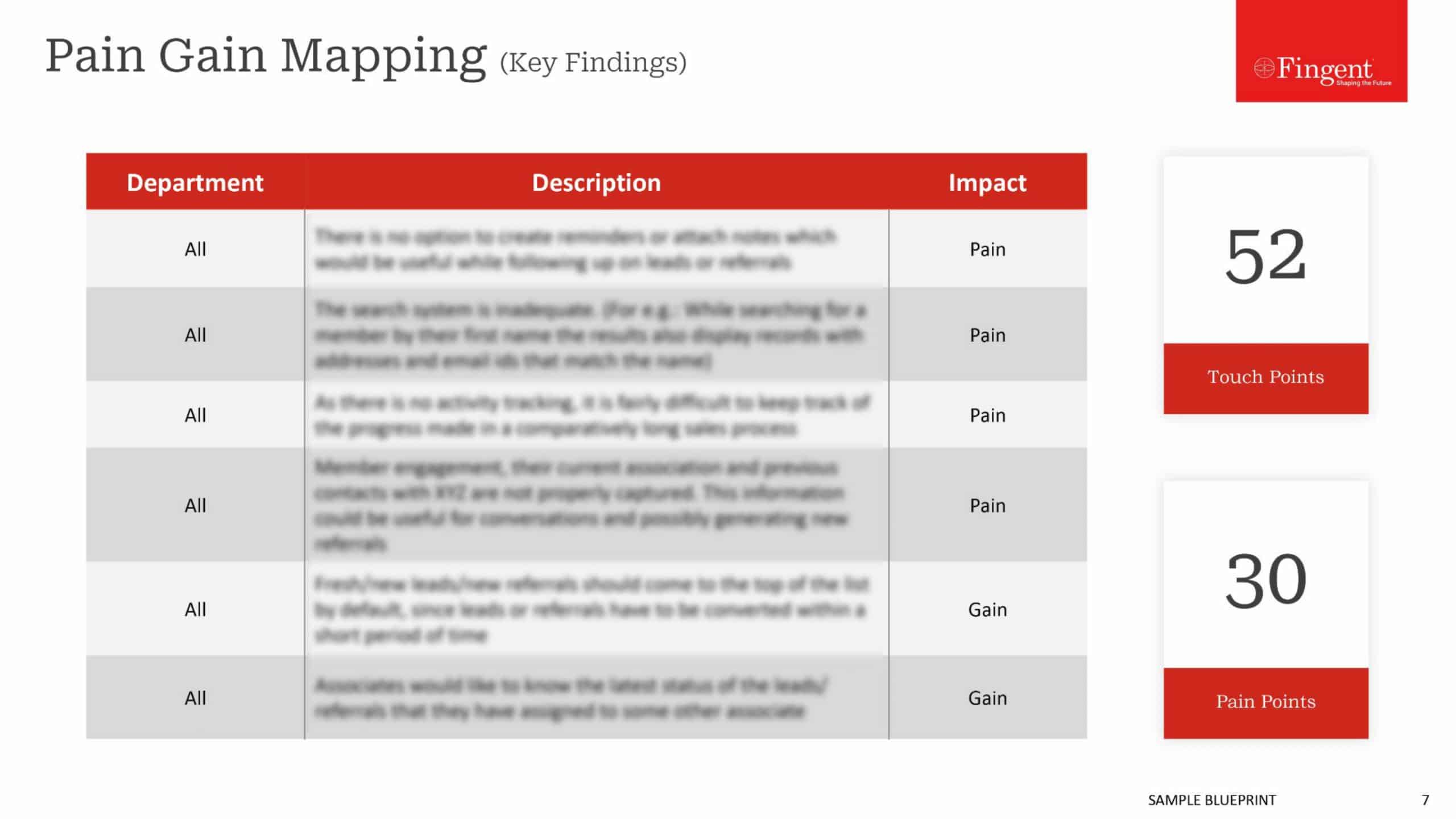
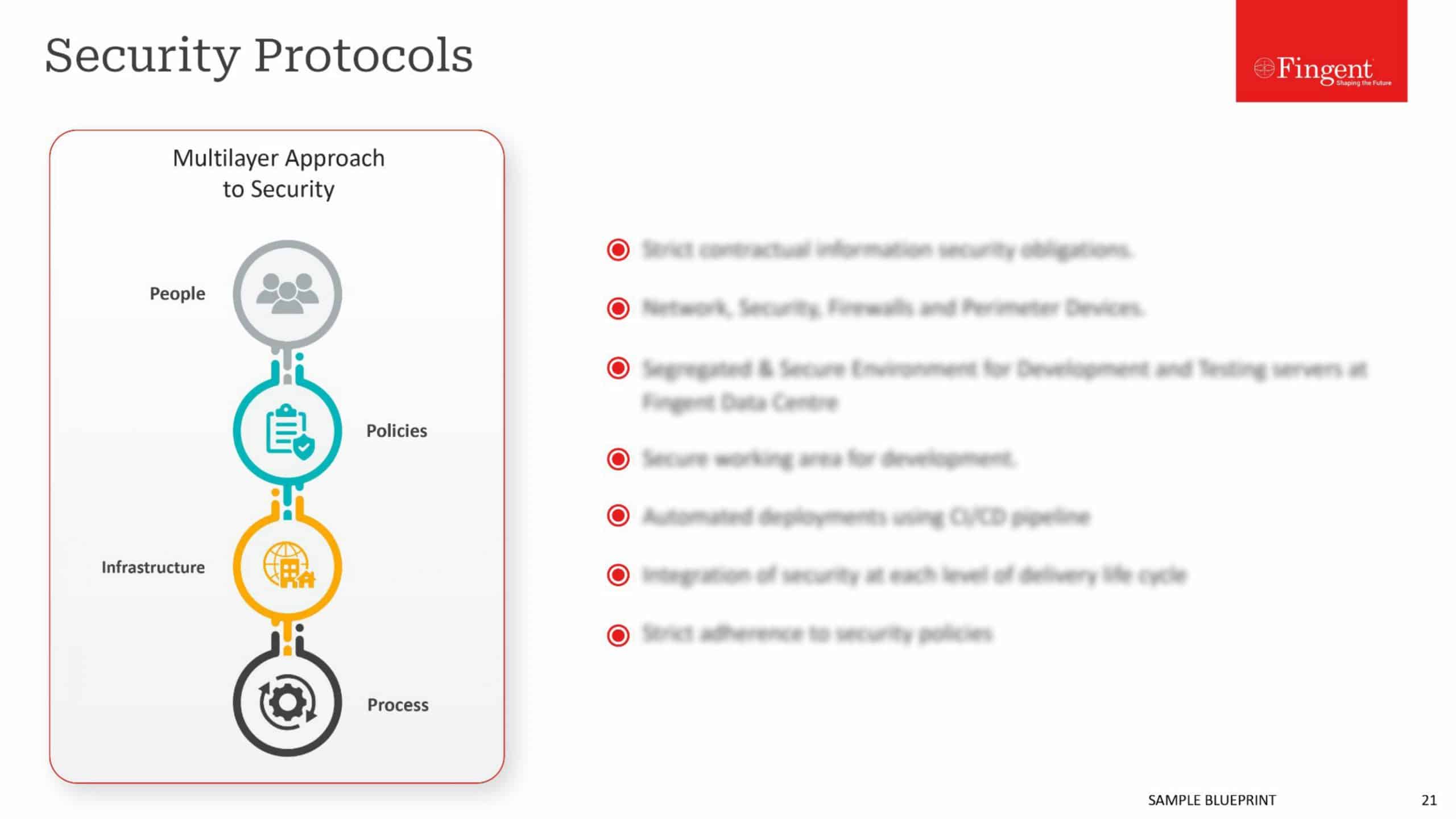
The security issues and occurrences are primarily associated with network-based security risks, availability, confidentiality threats and integrity risks. Events such as Denial of Service (DoS) attacks, malware attacks, message/media alteration attacks, spoofing and phishing attacks, man-in-the-middle attacks, and eavesdropping attacks are common in the multi-cloud environment.
Organizations are required to follow certain steps towards security to make sure that the security risks and occurrences are prevented, detected and controlled. The following security measures and steps shall be included in for achieving a secure multi-cloud environment.
- Prioritization of Visibility: The business organizations in the multi-cloud environment must ensure that they have complete visibility across all the cloud instances. Behavior-based monitoring shall be adopted for enhancing the visibility. Objectionable modifications and malevolent activities will also be highlighted with this process.
- Adherence to the Best Practices: In the case of the multi-cloud environment, there are various systems, devices, and networks that are involved. Each of these entities has a set of guiding principles and standards. The cloud security team must analyze and understand the best practices that are associated with each entity. For instance, in case of NoSQL databases present in the multi-cloud environment, it would be best to meet the compliance requirements, install advanced access control and authentication measures and promote database security for the overall security of the cloud.
- Flexible and Secure Governance: Governance is a critical element in any of the organizations. It is possible to establish trust and security across the organization only with the aid of well-governed systems. In association with the multi-cloud environment, the processes such as identity management, scheduling activities and resource allocation must be securely governed.
- Encryption of the Data at Rest: It is often witnessed that the business organizations enforce and implement the encryption of the information that is in-transit. However, the encryption of the information at rest is often not paid due attention. Such loopholes in security provide the attackers with an opportunity to get hold of the information at rest and misuse the same. It is, therefore, extremely necessary to encrypt the information at rest using advanced encryption algorithms.
- Advanced Shared Responsibility Model: Sharing of resources is one of the prime features of cloud computing, which gets enhanced in the multi-cloud environment. There are overlapping responsibilities and ideas that are often observed which may lead to the occurrences of loopholes in the security. Every entity that is present in a multi-cloud environment must make sure that complete justice is done to the shared responsibility model of the cloud. The allocation of roles and responsibilities shall be done in such a manner that there are complete transparency and ease of execution that is involved.
- Network-based Security Controls: Most of the security issues that occur in the multi-cloud environment have networks as the prime agents of the threats. It adds to the requirement of implementing automated and advanced network security tools and controls to ensure that such risks are avoided and controlled. Some of these tools include network monitoring tools, intrusion detection systems, intrusion prevention systems, anti-malware tools, and anti-denial tools.
Cloud strategy and planning has provided the organizations with the ability to enhance the performance, speed, and quality of their respective business operations and activities. With the occurrence of the security risks and threats, there is a poor impact on the business continuity and customer engagement. It is, therefore, required to include the basic and advanced steps to security to deal with the security issues and problems. These steps shall combine administrative, physical, logical and technical controls.
The use of security solutions that are available in the market will allow the organizations to achieve and maintain security in the multi-cloud environment. These solutions will provide an integrated security mechanism and will eliminate the need to deploy security measures for each of the cloud model and elements. Security concepts and requirements, such as information security, network security, and database security are now provided in a single package by the leading software solution providers while entrusting them for your digital transformations.
Stay up to date on what's new

Recommended Posts

05 Nov 2023 B2B
Cloud 101 – Getting a Good Return on Your Business Cloud Investment!
In the digital age, cloud investment is your business's propulsion, offering flexibility, scalability, and a competitive edge. However, many companies don't fully reap the cloud's benefits. The cloud's potential remains……

15 Oct 2023 B2B
Hyperscaler Cloud Services: The Next Step In Business Cloud Investment!
Companies can save 20% of the total annual cost if they migrate to the cloud. Hyperscaler Cloud Services can enable businesses to experiment, build, innovate, and run any form of……

10 Oct 2023 B2B
Guarding Your Digital Fortresses: The Imperative of Application Security
In the ever-evolving landscape of cybersecurity, application security stands as the impervious armor that shields your organization's digital fortresses. Imagine your organization's applications as the kingdom's gates – if left……

30 May 2023 B2B
Cloud Application Development: Empowering Your Business In The Digital Era!
“Cloud computing is really a no-brainer for any start-up because it allows you to test your business plan very quickly for little money. Every start-up, or even a division within……
Featured Blogs
Stay up to date on
what's new