Tag: security
An elixir! But with a Pinch of Salt!
This ubiquitous realm of Digital has not only weaved new waves, but has also unlocked potential problems of its own. But then again, it is the problems when addressed in the right way that brings any technology to maturity. The mobile era for enterprises is still relatively young and the right efforts at the early stages can do a lot in shaping the technology to make it the reckoning power it can be. Enterprises need the reassurance that the potential challenges mentioned below can be dealt effectively, having lesser hassles as we move on into a truly mobile landscape.
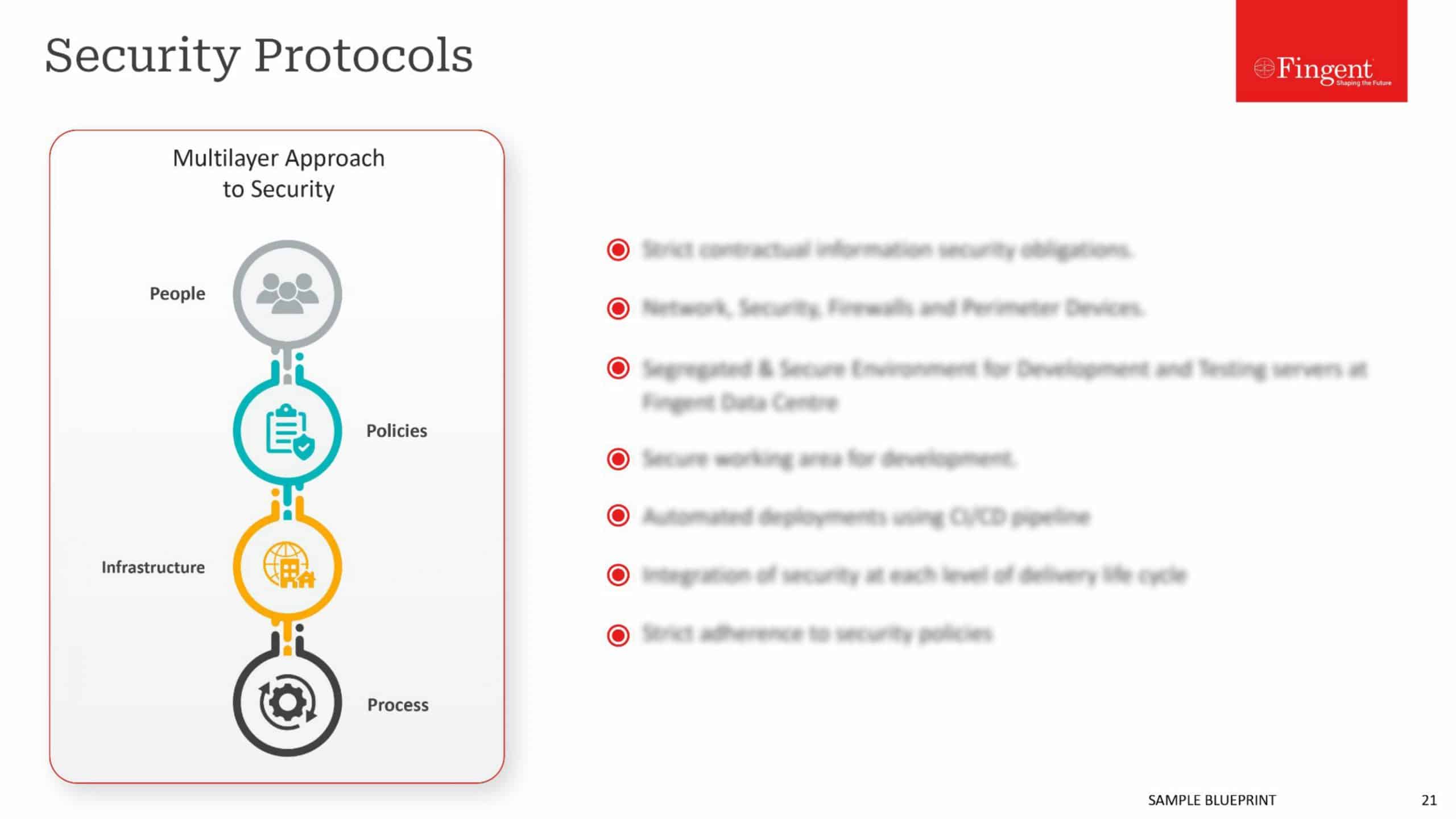
Security
The influx of mobile device has given businesses the opportunity to expand into new areas and to get equipped with tools that previously did not exist. The scale still tilts in the direction of being cautious even with these possibilities. BYOD strategies have been reluctantly welcomed by organisations due to concerns of security and the possible increase in points of vulnerability. With mobile, a new kind of vulnerability of possible theft also becomes prominent. Such threats can lead to loss of corporate data, giving unauthorized access to the corporate network. Even though the scale tilts more dominantly to the side of being mobile wary, it shouldn’t be the case going forward. There can be protocols and inbuilt security that can stop a lot of security concerns but refraining from and educating the employees about risky interactions can help the corporates have better control.
Data Access
It is highly imperative that an employee working from the field is not limited to the data that he has. With concerns over security, mobile should not be an inferior option to the connected devices in the offices. Having limits on the way mobile can perform, defeats the purpose for which it stands for, rendering the capital spend for mobile strategy irrelevant. With a good mobile application development policy, data can be provided in real time with the IT having a secure control over it.
Enterprise Mobile Applications
Statistics tells us that employee productivity can increase by more than 30% with an enterprise mobile app. But the problem is, most organisations fail to tap into this productivity due to short-sightedness in the development of the app. The multitude of devices and the OS makes it difficult to build native apps for these diverse scenarios, this along with the lack of skilled developers and testing makes it a headache even with the right more profound. Hence it becomes imperative for organisations to take expert help for giving efficient, swift and functional mobile apps.
Supporting Mobile Workforce
Managing a remote workforce should also have a streamlined process through which IT can support them. The workforce irrespective of their location should be able to connect seamlessly in times of need to take required help from IT. This makes a strong network a default requirement make the enterprise mobility a success. The creation of a working environment in which employees can do what they do traditionally in an office space is the final litmus of a truly mobile workforce. They should not feel limited by the network, the device, the application or the security.
The Mobile strategy is here to stay, it becomes imperative for an organization to develop full-fledged, well-rounded apps that can deliver a consistent experience to the user. Granted using mobile has a few concerns, but these would get rectified along the way. There is no shying away from a mobile strategy especially with the exponential adoption of mobile devices all around, it only becomes a natural evolution of the workplace to rest within the hands of the employees in times to come.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
While security remains a pressing concern in the mobility space in continental Europe, UX is now emerging as a bigger investment area, in the English-speaking world of UK and US.
The increasing investment in UX syncs with the preferences of today’s highly demanding customers, who value a hassle-free engagement, without having to struggle to consume information. Even users of enterprise apps now expect a visual appeal, or UX similar to what they find with games and other consumer apps.
Traditionally, UX and security have been inversely linked, with improvements in security often getting in the way of UX. For instance, the common requirement of having to reset password once in two weeks makes the account more secure, but impede usability. Similarly, blocking file download from an unknown IP address may prevent a hacker from accessing the data, but also prevents the user from accessing his own data when he needs it, on the move.
The best security is invisible, working away in the background, keeping digital assets safe without the user even noticing the workings. While the ground reality is far from such an ideal state in most enterprises, there is now growing realization that the tendency to push in too many security features, especially in an already stressed mobility space, can drive away users, or worse, prompt them to seek out loopholes.
The solution, however, is not to throw security out with the UX bathwater, but rather deliver a seamless UX yet uncompromising on any security considerations. This requires a change of approach, best exemplified by an allegory of locks. While the existing approach resembles adding more number of locks to a door, which while keeping trespassers away also makes it more difficult for the genuine user to get it, the new approach tries to offer only a single, but an unbreakable lock. Mobility investments are flowing in this direction.
One way to reconcile security with UX is the “security by design” approach, or building in security early in the development process, rather than co-opt it as an awkward extra layer in the end, akin to manufacturing a door with a deadbolt lock built-in rather than affixing locks after installing the door.
But what exactly is the difference, one may be left wondering?
Consider an approach where users need to enter their login credentials every time and access to a specific section or resource depends on the credentials provided and another approach where there is a tight control on what each and every user can see, based on a need-to-see basis incorporated at the design stage itself. A user, rather than being prevented from peeking at data, not for their eyes, may not be served with means to access to such data in the first place. For example, the sales team may be given an app that offers all sales data, but not information that pickers in the warehouse access through their apps, and managers have another set of apps, offering a far wider range of data and information.
Another approach to reconciling the divide between security and UX is through the hardware. A case in point is Apple’s Touch ID fingerprint scanner and similar systems on Android smartphones. When hardware becomes the trusted security medium, UX can be spared from having to authenticating users. The assumption, of course, is only the right users will have access to the hardware in the first place.
Yet another approach is not to break it, but explain it. At times, there’s no workaround for a security procedure that impedes a smooth UX. In fact, focusing too much on usability may be counter-intuitive, for what is the easiest and most convenient may not be in the best interests of security. A confusing interface may best be solved with a tutorial, a FAQ page, or some help videos, rather than breaking the interface for the sake of UX and impede security in the process. There is also the issue of writing earning message in a way users understand, focusing on the implications of an unsafe action, rather than harping on technical jargon.
Security is all-important, but only if there are users available in the first place. A poor UX in today’s highly demanding and competitive age would simply drive away users, making rigid security protocols self-defeating and redundant. Developers are widening up to this all-important logjam and investing big in UX, but such focus should be with the understanding that UX and security aren’t necessarily at odds, and the duo even benefits each other.
Your best bet in developing state of the art mobility software that offers the best of both worlds is partnering with us. Our experienced and versatile team of developers understand both UX issues and security considerations and help you roll out software and apps that fit the bill perfectly.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
When Angela Bennet in “The Net”, wakes up from her sleep at the hospital, after being unconscious for three days, she realizes that all records of her life have been deleted. She has been checked out of her hotel, her credits cards have all become invalid and her car is also not there in the parking lot anymore….
Remember the panic attack she gets?
This 1995, Sandra Bullock starrer was one of the first few films to depict the possibility of being electronically erased completely. It also shows how people get forced to grapple with the consequences of identity theft. Since then, many similar movies and advertisements have come out, that dramatize and add fuel to our fear of identity theft. According to a report by Javelin Strategy and Research, in 2011, around 28 million Americans were found to be the victims of identity theft.
That said, are you one of those people who stays alert and ahead of such crimes? Or are you the kind who lives in fear of such crimes, but have not done anything about it?
If you belong to the latter, then it’s high time you took necessary steps to protect your digital life. Here’s a start:
- Be sure to install security systems with automatic updates – Security systems need to be kept updated with time, because as technology grows, so do the ways to hack and break in. Updates in security systems are meant to fix bugs and enable new features for more protection. Hence, it is important that you get these updates on time. Most systems can be set to update itself automatically, so you can get them in a few minutes.
- Use strong passwords – A password is one of the most effective ways of protecting your data. Having a strong password goes a long way into keeping your data safe and secure. Although, you should avoid having the same password for more than one account, file or folder. It’s always good to have strong words or even phrases as passwords. Ideally, a considerably long word, say about 9 characters in length, with a combination of letters and numbers or uppercase and lowercase characters would do. Or else a phrase with the same combination too. Even though, remembering passwords is difficult, you have got to use these.
- Use data encryption – Encryption basically means converting data into an unrecognizable form or an “encrypted” form. It is commonly used for protecting sensitive or personal information on the internet. You can encrypt your data using encryption utilities available in the market. You need to also try as much as possible to use encrypted sites as well, especially for banking or payment related necessities. An encrypted site will have the symbol of a lock on its status bar. Also, using shared or public networks should be done with caution. Accessing personal information over a public network is not advised.
- Use the cloud – The all-pervasive cloud is one of the best ways to keep your data safe and secure. External hard drives, just like your laptop or smartphone, are always vulnerable to theft and even other kinds of damages. Having your data backed up in your cloud, and secured with a strong password, will ensure that you don’t lose any important information. Whatever happens to your physical devices, you always have a backup of everything in the cloud. Plus, you can easily access it from anywhere and from any device.
- Use the web anonymously – As much as possible, use proxy servers while searching the internet, so that your identity and location remains anonymous. For example, the incognito window on the Google Chrome browser helps to be safe to some extent. TOR is another free software that directs internet traffic through a large worldwide network of more than 2000 links, which makes your browsing difficult to find or trace. There are also other search engines and browsers that allow using the internet confidentially and do not provide any information, such as your computer ID or location, even when asked for.
Apart from all this, you need to be extra careful about your personal belongings like your wallet, where you carry your credit cards and your smartphones, where you could store information related to your social security number or bank accounts and the like. Sometimes, being a little vigilant may be all it takes to protect your digital life.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
If you are like me, you would have fantasized: ‘IoT would bring my reign, treat me like a Prince and put me in a world of sheer convenience’. Oh wait, does the monarchical system feel a bit too old or overstated? Ok, let’s fast forward to the ‘Democracy’, where you at least thought, the IoT will let you be like Richie Rich, “the poor little rich boy” with a ‘Dollar’matian dog, who had nearly everything automated around him.
No wonder, because with IoT, – “Everything that can be automated will be automated”- said Robert Cannon, Internet law and Policy Expert.
Internet of Things– the new buzz is certainly the next big thing you are going to witness, whether you are its fan or critic! In a nutshell, Internet of things, also called Internet of Everything (IoT) is a network into which the everyday things in our life (like phones, car, laptop, tea machine, alarms and anything with an ‘on & off’ switch to internet) are connected for machine to machine communication within themselves to accomplish tasks. After an era of connecting places and people, the Internet of Future is all geared up to connect every object/thing in our day to day life. It took a decade to deploy the first billion internet-connected sensors, a billion more sensors were deployed in the year 2013 alone, and now we are on our way to a trillion connected devices, very soon we’ll see everything connected to this network.
As it has been at every point of this development, with a lot of conveniences and possibilities come the open chances to insecurity, vulnerability, and privacy breach. And with IoT, these aren’t the regular “my remote knows my email password” type of issues, but are going to be more severe vulnerabilities. Trust me, you ain’t seen nothing if you thought Viruses, Trojans, rogue security software or phishing attacks were serious security issues, because your total security in future- whether you use or don’t use computers/internet, is under the nose tip of: THE INTERNET OF THINGS!!!
While making life convenient and comfortable, the availability, use and exchange of private data during the courses of providing various IoT services/applications will also generate severe security/ privacy issues. More and more private information will be fed into machines and when these machines go online, there stands a possibility for hackers too to access these. “We have created a whole new playground for attackers to dream up things to do — whether it is nuisance, whether it is theft or whether it is violence”, says Jeff Greene, senior policy counsel at Symantec, and co-chair of the NSTAC task force.
…There you see Richie’s fancy Mansion slowly fading and evolving into Mario’s dreaded Sky Island 18 hole challenge…
Let’s see how the IoT will challenge its adopters,
Top security challenges that IoT would encounter:
- Too many points of breach: In IoT, every device and sensors would represent a potential risk. How confident can companies be about their huge number of devices connected in IoT, their ability to preserve the confidentiality and integrity of Data? Researchers at Eurecom technology institute, France, downloaded 32000 firmware images from potential IoT device manufacturers and found 38 new vulnerabilities in more than 693 images that were extended to over 123 products. These vulnerabilities included poor encryption or loopholes to unauthorized access and affected nearly 140K devices in the Internet.
- Unlawful Surveillance: The various objects connected to the IoT via internet connecting modules in it, like toys, cars, keys or home appliances can be potential threat of illegal surveillances. For instance, Federal Trade Commission (FTC) had to file a complaint against the wireless camera production company, TRENDnet Inc. in 2013, as the videos recorded by nearly 700 of their cameras were hacked and put up with insecure internet links. This was due to the lack of proper security guidelines for the wireless cameras. Similar issues can happen in IoT where a lot of personal things used every day can compromise your privacy or security to criminals who can access even more information through your compromised/less secure things in the network. Economist reports that 60% of the surveyed business leaders think that security and privacy issues will hamper uptake of IoT by customers.
- The integrity and reliability of data collected: IoT will bring data from all sort of sensors connected in its network to corporate systems. Organizations can’t be sure whether all these data are secure, compromised or interfered with.
- All sort of personal data up there in the network and you expect privacy? With all sort of data collected from our daily lives, IoT will help us make smarter decisions and bring smarter solutions. But, what if the data collected by different devices get compromised at any point? Criminals will be able to actively intrude in private lives of people. A similar breach happened recently with a Japanese automated toilet, where Trustwave Holdings Inc’s consultant, Daniel Crowley hacked it, and was able to play music or make it flush randomly.
Nevertheless, the impact of such smart connected devices is expected to be in trillions annually, which lured the eyes of many, who argued that proper regulations and policies can very well apply brakes to such malpractices with IoT. Enterprise IT managers, policy makers, and other smart guarding brains have shielded us from challenges arising with every innovative technology, with the help of even better technology and policies to lessen such risks. If consumers, developers and providers clearly understand the security issues associated with the different modules, providing best IoT solutions with security and privacy factors kept intact wouldn’t be an unattainable goal, though it will be tricky.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new