6 Proven Ways for Businesses to Combat Cloud Security Risks
Cloud security threats: How to protect your data and mitigate risks?
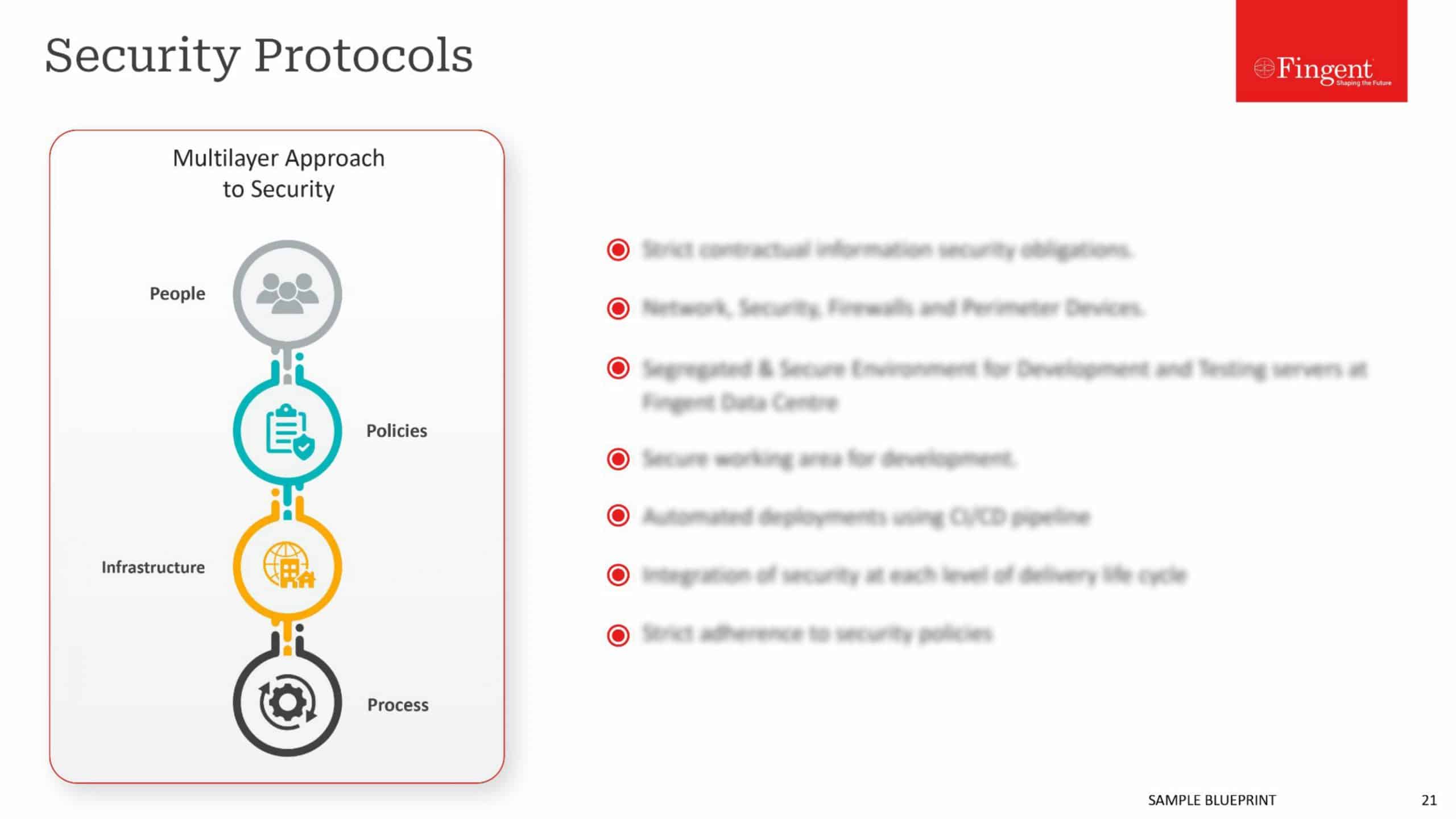
Be it Google G-Suite, Dropbox, Adobe, Salesforce, or Microsoft Office 365, almost every business uses cloud services for their critical business requirements. Despite its rapid growth, cloud computing brings the possibility of severe security threats that can drastically affect an organization. According to Cybersecurity Ventures, cybercrime damages might hit $6 trillion by 2021. 1 out of 4 will experience a data breach, and on average, businesses are investing about $7.2 million on security breaches. These figures prove how devastating security threats can be if they are left unchecked.
While cloud systems, applications, and networks are not located within your control physically, the security responsibility and risk mitigation are definitely within your control.
Some of the latest security threats to cloud data management include:
- Phishing attacks
- Ransomware attacks
- Insider threats
- Asynchronous procedure calls
- Distributed Denial of Service Attacks (DDoS)
- Uneven security gaps
Why is cloud security important?
While cloud service providers protect your data, they can’t protect your data when it leaves the cloud to interact with other systems.
Cloud security is essential to protect your data as well as the integrity of your business. According to a survey, 60% of breaches occur at patches that are available but not applied. You will need a team to continually monitor potential security threats to ensure that your cloud infrastructure is always up-to-date.
Regardless of your organization’s size, it would be best to implement strong network security services to protect your organizational and customer data.
Read more: Why It’s Time to Embrace Cloud and Mobility Trends To Recession-Proof Your Business?
Six ways to protect your data and monitor your cloud environment
1. Set-up multi-factor authentication (MFA)
Stolen credentials make it easy for hackers to access your business data and applications is to steal your credentials. The combination of complex usernames and passwords alone is not sufficient to secure your user accounts from hackers.
So, protect your cloud users with two-factor authentication or multi-factor authentication to ensure only authorized people can access your cloud apps and have access to sensitive information.
Deploying multi-factor authentication is an effective way to keep potential hackers from accessing your cloud applications. Most security experts believe that it is mandatory to implement MFA as it is also one of the cheapest security controls an organization can have.
2. Assign access controls
Not all your employees need to have access to every file, application, or data. By setting up proper authorization levels, each employee can only view or access applications or data required to complete their job.
Assigning access controls will ensure that your employees don’t edit any information accidentally that they are not authorized to access. Additionally, it will also protect you from hackers who have hacked an employee’s credentials.
3. Leverage automation to monitor, log and analyze user activities
Real-time monitoring and user activity analysis can help you identify any irregularities or abnormal moves that are not part of your regular usage patterns. For example, log in from an unknown IP or device.
Such irregularities could indicate a breach in your system, so it is essential to identify them early on to prevent hackers from hacking your system and help you resolve any security issues before they wreak havoc with your security system.
You can leverage data protection solutions to automate the process and support 24/7 monitoring and management.
Note: Every business has different needs for different levels of security services, so you may consider getting a third-party risk assessment before making significant investments. At Fingent top custom software development company, we identify and evaluate any loopholes in your current infrastructure and provide you with apt cloud infrastructure solutions using our unique approach.
Read more: Cloud Service Models Saas, IaaS, Paas – Choose the Right One for Your Business
4. Provide anti-phishing training to your employees
Small Business Trends reports that 1 in every 99 emails is a phishing attack, which amounts to 4.8 emails per employee in a five-day workweek.
Hackers can easily steal employees’ login credentials to gain access to secure information via phishing. In this kind of social engineering attack, the attacker sends fraudulent emails, texts, or websites to trick the victim into sharing access to sensitive information. Providing ongoing training to your employees to recognize a phishing attempt is the best way to prevent employees from falling prey to such scams.
5. Create a comprehensive off-boarding process for departing employees
Ensure that your departing employees no longer have access to your cloud storage, data, systems, customer data, and intellectual properties.
As every employee is likely to have access to different cloud applications and platforms, you need to set up a process that will ensure all the access rights for departing employees are revoked. If you can’t manage this internally, you may consider outsourcing this task to a credible vendor.
Learn more: Take a look at how InfinCE, an infinite cloud platform, ensures secured work-collaboration within an organization, and helps enhance company efficiency & growth!
6. Cloud-to-cloud backup solutions
There is no doubt that there are legitimate risks associated with any cloud application or platform. However, the odds of you losing data due to your cloud provider’s error is low compared to human error.
Say, an employee deletes your data accidentally, and a hacker obtains the account password and corrupts the information, or an employee clears her inbox and folders. In such cases, cloud providers can do nothing much past a specific period. Most cloud providers store deleted data only for a short time.
You can check with your cloud provider about the time frame and whether they charge any fees to restore the data. If your company must abide by strict regulations or be concerned about being liable for corrupted data, you can consider cloud-to-cloud back-up solutions.
Read more: Cloud Migration Strategy: 7 Steps to Accomplish a Flawless Transition
What Next?
There’s no denying that cloud computing is one of the most cost-effective options to maintain a high level of security for your sensitive data. At Fingent, our experts can help design a comprehensive cloud computing strategy that will help achieve your business objectives and provide you with ongoing management to keep your data protected. Contact us now and get started.
Stay up to date on what's new

Recommended Posts

05 Nov 2023 B2B
Cloud 101 – Getting a Good Return on Your Business Cloud Investment!
In the digital age, cloud investment is your business's propulsion, offering flexibility, scalability, and a competitive edge. However, many companies don't fully reap the cloud's benefits. The cloud's potential remains……

15 Oct 2023 B2B
Hyperscaler Cloud Services: The Next Step In Business Cloud Investment!
Companies can save 20% of the total annual cost if they migrate to the cloud. Hyperscaler Cloud Services can enable businesses to experiment, build, innovate, and run any form of……

10 Oct 2023 B2B
Guarding Your Digital Fortresses: The Imperative of Application Security
In the ever-evolving landscape of cybersecurity, application security stands as the impervious armor that shields your organization's digital fortresses. Imagine your organization's applications as the kingdom's gates – if left……

30 May 2023 B2B
Cloud Application Development: Empowering Your Business In The Digital Era!
“Cloud computing is really a no-brainer for any start-up because it allows you to test your business plan very quickly for little money. Every start-up, or even a division within……
Featured Blogs
Stay up to date on
what's new