Tag: Mobility
Mobile payments are of a recent origin but have caught on like wildfire. Mobile-driven commerce now exceeds US$972.25 billion, and mobile payments are expected to touch US$3 trillion by 2021. This figure will equate to about 11% of all consumer card payment volume, up from the present levels of 6%.
Here are the top trends shaping mobile payments market.
Demographics Shape Mobile Payment Growth
The bulk of the growth in mobile payments market is from the Asia-Pacific region, especially China. Chinese customers now make more payments through mobile devices than through desktops. The high level of smartphone penetration cuts across both urban and rural areas.
The mobile-first mindset is catching up in the US and the UK as well. By 2020, more consumers in these countries will make payments for goods and services over smartphones than through desktops. About 46% of all digital commerce in the US and 38% of all digital commerce in the UK would be through a mobile device by 2020, up from 20% and 12% respectively, in 2015.
It comes as no surprise that cutting across geographies, the up-and-coming generations are in the forefront of adopting new technologies, and embracing mobile wallets in big numbers.
Convenience of On-the-Go Consumption Drives Growth
The chief factor driving the growth of mobile payments market is convenience.
M-payment allows consumers to transfer money for the purchase of goods and services, pay utility bills, collect paychecks, take insurance, make loans, and do much more, all with just their smartphone or tablet. People can either retain some money in their mobile wallet or link their bank account to the mobile wallet.
Furthermore, mobile devices make it very easy for people to conduct online transactions when commuting, or in the middle of doing something else. A consumer, having seen a hoarding when commuting to the office, no longer need to wait to get in front of a computer, but can rather pick up her smartphone and purchase the product immediately. Such a high level of on-the-go consumption is facilitated by the availability of user-friendly apps, which in turn is powered by mass subscriber volumes resulting from high levels of smartphone penetration, and widespread internet connection.
The Rise of Biometrics
Even as mobile payments surge, security remains a prime concern. Considering 70% of online fraud taking place through identity theft, the stakeholders of the mobile payment industry are increasingly looking at biometrics as a means to contain fraud. Biometric authentication involves validating the transaction based on the user’s fingerprints, iris and retina scanning, facial recognition, voice, or any other unique feature. With more and more smartphones now featuring fingerprint scanners, and other biometric enabling options, biometric authentication will become a common feature in the coming years.
The Quandary of Proximity Payments
The bulk of mobile payments today is remote mobile payments. The other side of mobile payments, proximity payments, is yet tot to gain sufficient traction, despite the potential. Gartner estimates money transfer to continue dominating mobile transactions, with an estimated 67% share in 2017, and predicts an overall annual growth of 35% in mobile transaction value, between 2013 and 2017. Nevertheless, with more and more traditional cash-only services, from taxis to hairdressers and from cleaning services to bakeries now able to accept mobile payments, proximity payments is sure to catch up in the near future.
What has restrained proximity payments so far is the big security hole in NFC, the enabling technology, as exposed by Charlie Miller, a smartphone hacker, in a 2012 Black Hat security conference. The rise of Bluetooth Low Energy (BLE), an alternative and more promising technology, coupled with several providers such as AliPay offering hassle-free mobile wallets means proximity payments is on the cusp of being the next big thing in mobile internet.
The Rise of Virtual Currencies
E-money ranging from bitcoins to Facebook Credits, and from egold to merchant loyalty points are becoming more and more popular. Such virtual currencies create a lock or loyalty, as it cannot be transferred outside of the system easily. While mainstream m-payment solutions steer clear of many such payment options owing to its legal gray area, there is increasing interest in the technology that drives such cryptocurrencies.
Supporting virtual currency such as bitcoins is peer-to-peer payment infrastructure, which allows making payments to any payee in the network, without routing it through a central agency or middleman. Such transactions are more robust, and is now very popular in the dark internet, for under-the-hood and illegal transactions. Whether currencies such as bitcoins will become mainstream is to be seen, but infrastructure such as peer to peer networks is sure to be adopted by legit providers as well, displacing existing m-payment systems, owing to its inherent security advantages.
The payment industry is in the midst of a new Gold Rush. In 2010-2011, about 700 companies invested about USD $3.4 billion in innovation related to the payments sector, and many of such investments are bearing fruit now. Gartner estimates global mobile transaction volume and value to average 35% annual growth between 2012 and 2017 and forecast a market worth $721 billion, and more than 450 million users, by 2017.
Despite the current limitations such as lack of a universally enforceable standard, m-payment is on its way to becoming a viable alternative to physical currency. E-tailers and other businesses are certain to lose out if they do not prepare for the mobile payment space. Success depends on setting up a robust and easy infrastructure, and this is best served by partnering with an experienced and resourceful provider, who has both the experience to do a good job, and the ingenuity to leverage the latest advancement and develop cutting-edge solutions. We fit the bill in all counts. Contact us today for all your m-payment requirements.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
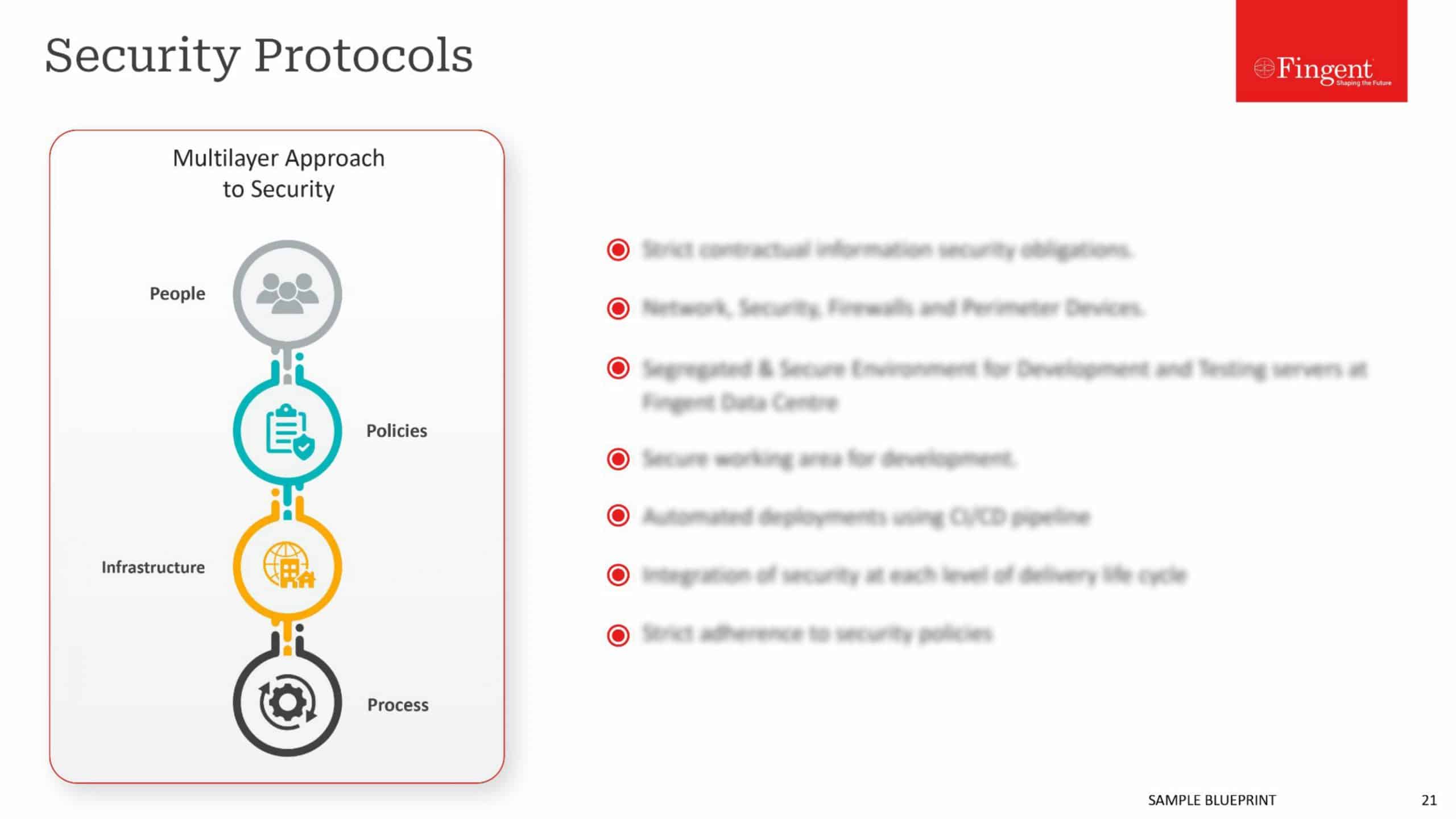
While security remains a pressing concern in the mobility space in continental Europe, UX is now emerging as a bigger investment area, in the English-speaking world of UK and US.
The increasing investment in UX syncs with the preferences of today’s highly demanding customers, who value a hassle-free engagement, without having to struggle to consume information. Even users of enterprise apps now expect a visual appeal, or UX similar to what they find with games and other consumer apps.
Traditionally, UX and security have been inversely linked, with improvements in security often getting in the way of UX. For instance, the common requirement of having to reset password once in two weeks makes the account more secure, but impede usability. Similarly, blocking file download from an unknown IP address may prevent a hacker from accessing the data, but also prevents the user from accessing his own data when he needs it, on the move.
The best security is invisible, working away in the background, keeping digital assets safe without the user even noticing the workings. While the ground reality is far from such an ideal state in most enterprises, there is now growing realization that the tendency to push in too many security features, especially in an already stressed mobility space, can drive away users, or worse, prompt them to seek out loopholes.
The solution, however, is not to throw security out with the UX bathwater, but rather deliver a seamless UX yet uncompromising on any security considerations. This requires a change of approach, best exemplified by an allegory of locks. While the existing approach resembles adding more number of locks to a door, which while keeping trespassers away also makes it more difficult for the genuine user to get it, the new approach tries to offer only a single, but an unbreakable lock. Mobility investments are flowing in this direction.
One way to reconcile security with UX is the “security by design” approach, or building in security early in the development process, rather than co-opt it as an awkward extra layer in the end, akin to manufacturing a door with a deadbolt lock built-in rather than affixing locks after installing the door.
But what exactly is the difference, one may be left wondering?
Consider an approach where users need to enter their login credentials every time and access to a specific section or resource depends on the credentials provided and another approach where there is a tight control on what each and every user can see, based on a need-to-see basis incorporated at the design stage itself. A user, rather than being prevented from peeking at data, not for their eyes, may not be served with means to access to such data in the first place. For example, the sales team may be given an app that offers all sales data, but not information that pickers in the warehouse access through their apps, and managers have another set of apps, offering a far wider range of data and information.
Another approach to reconciling the divide between security and UX is through the hardware. A case in point is Apple’s Touch ID fingerprint scanner and similar systems on Android smartphones. When hardware becomes the trusted security medium, UX can be spared from having to authenticating users. The assumption, of course, is only the right users will have access to the hardware in the first place.
Yet another approach is not to break it, but explain it. At times, there’s no workaround for a security procedure that impedes a smooth UX. In fact, focusing too much on usability may be counter-intuitive, for what is the easiest and most convenient may not be in the best interests of security. A confusing interface may best be solved with a tutorial, a FAQ page, or some help videos, rather than breaking the interface for the sake of UX and impede security in the process. There is also the issue of writing earning message in a way users understand, focusing on the implications of an unsafe action, rather than harping on technical jargon.
Security is all-important, but only if there are users available in the first place. A poor UX in today’s highly demanding and competitive age would simply drive away users, making rigid security protocols self-defeating and redundant. Developers are widening up to this all-important logjam and investing big in UX, but such focus should be with the understanding that UX and security aren’t necessarily at odds, and the duo even benefits each other.
Your best bet in developing state of the art mobility software that offers the best of both worlds is partnering with us. Our experienced and versatile team of developers understand both UX issues and security considerations and help you roll out software and apps that fit the bill perfectly.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
By the late 1980’s the prominent sound of “ding, ding, zip” of the typewriters that reverbed through the office halls gave way for a softer, mimicked, mechanical feel of the typewriters. The computer keyboards with time evolved, making it the familiar yet a distinct avatar of the faithful typewriters of the past. What changed was more than just the mechanical clinker in the office halls; they gave rise to a new status quo on how work was performed and what could be achieved by ideally leveraging the computers.
A Digital Revolution
A little bit of reflection on the successful business of our times like Facebook, WhatsApp, Zynga, Twitter, Square, Netflix, points to the fact that, these companies were either born digital or made efforts to alter their business to becoming digital. The companies that innovated, the ones that laid the old to rest, followed a process of creative destruction. What businesses have to remember is that, most of the times the employees and the customers have got a faster affinity to adapt to changing technology. This adoption would only be followed by an expectation that the business that they interact with, also follows suit. For B2B players it becomes important that they use Mobile, Big Data, IoT, 5G, and augmented reality for revolutionising the customer experience, optimising operational and industrial processes, innovating rapidly, bringing faster cash cycles, driving employee productivity and for improved service enhancements.
Statistics shows that there would be 6.1 billion smartphone users worldwide, 56% of all web traffic is through mobile and the global mobile data traffic is expected to reach 6.2 Exabytes/ month! That’s a lot of numbers indicating the importance of a Mobile strategy.
Digital Business Transformation through Mobility
Mobility is not just about going wireless. It focuses on the business process and the work models that effectively utilise mobile. Internally it is about the business models and processes that can enable marketing, HR and operations to utilise the benefits of going mobile like improved and faster decision making, increased productivity of the employees, faster resolution of internal issues, brand perception enhancements, reduced sales cycle time and increased revenues. But there are concerns of network security, compatibility and security of the devices, corporate and customer data security, regulatory requirements that always make the C-Suite executives think twice before they tread on these unsure waters.
Transforming a business through mobility has to have a well-rounded view of the entire business and a thorough recognition of the priorities of going mobile. It can be as simple as supporting more mobile handheld devices, extending internal systems for mobile access, offering incremental BYOD, providing more mobile support to the customer, implementing corporate mobility policies and so on. With Mobility, work becomes something that people do and not a place they go to, it has the capability to bring transformations with regards to:
Increased Revenue Potential
Mobility is pervasive and the ever trusted smartphone has led the march, becoming the go-to device, people use for work, pleasure or to kill boredom. Living in the comfort of your pockets, the mobile becomes the first medium of choice for one to interact with the outside world. This gives business a chance to connect to the customers at any point of time. Similarly, mobile apps that can help the customer consume products and services would invariably help to increase revenues. Employee empowerment and customer engagement are the two critical interactions for a business to make. Having a solid mobile strategy would help them both to be connected on the move, thus effectively enabling contracts and deals closures on real-time.
Flexibility
The first signs of going digital would be improved employee freedom. An employee would no longer be restricted to the cubicles, instead he/she will get a chance to work on ‘wherever whenever’ style. Through cloud-based applications, the staff would be able to access resources and attend to important work, no matter where they are. Such apps are now even built with offline connectivity that can help the field workers to sync things later into the cloud while effectively helping them perform their work. Reach out is one such app that has been developed with the offline connectivity, for managing work orders and jobs in inspection and audits. This goes a long way into providing flexibility, responsiveness and faster turnaround times, which in the end translate to excellent customer satisfaction. This sets up a win-win for both the customer and the business as it enhances the way you work and the way the business serves the customers need.
Collaboration
Another major contributor to employee productivity is the way mobility enables workplace collaboration, regardless of the physical proximity of individuals and teams. When effective collaboration is required among individuals and teams spread across multiple locations, mobile truly makes the effort more streamlined and natural. Cloud-based enterprise collaboration software can help teams to break down barriers of location and time, bringing the best of talents to work in unison.
Communication
With the flexible and collaborative nature of work, there comes a need of precise and timely communication that can draw the line between being successful or crashing out. It becomes highly essential that the mobile workforce is appraised with relevant metrics that help them to take the right decision and also to update crucial project updates. Aware mobility helps to accelerate performance by having this view of important metrics right on your trusted iOS or Android device. This can help to get on time information that helps you take that important decision when required.
Operational Efficiency and Productivity
Businesses would have to change the way they have conducted themselves over the years. They would need to get re-organised, to accommodate the task oriented usage style of mobile users and deliver them efficiently, without having any security concerns. Real time statistics of location and direction have already helped logistics and field service, to come up with strategic ways in which these could be leveraged. This leveraging should ideally result from a re-envisioned business process. Mobilisation of Salesforce interactions, supply chain management and innovative charging models can be devised by having mobile at the hub of the transformation, for a truly digital organization.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
A few years back began the hype around going completely mobile in your field service, and improving productivity. Was it all worth the hype?
Now, we have a number of field service companies that have survived and succeeded to say “yes” to that question and tell the story of how game changing it is.
So far we have learned about the different advantages of going mobile, about the importance of capturing data from the site effectively, and also how we can use mobile technologies to achieve this purpose. Now, how can you put this captured data to effective use?
Once you’ve equipped your field service staff with all the latest mobile technologies, you have a systematic flow of different kinds of data coming in from your customer sites. Here are some ways in which you can use such data:
To monitor technician performance

For compliance
Technicians use their mobile apps to record job details like the kind of job, the time procedure followed, the time taken etc. This allows the managers to see whether their technicians promptly comply with legal regulations and standards, along with the company safety and performance standards.
To achieve customer satisfaction

To plan for the future
With the help of different analytics tools, the data captured on-site can be utilized to gain useful insights about your company as well as your employees. You can generate different kinds of reports, easy-to-interpret charts and graphs etc. on various areas of your business, so as to analyze the current scenario and plan for the future. It thus, not only helps in benchmarking your workforce but also helps to make the best decisions for future needs.
With the help of such data captured on-site, organizations can provide more of proactive service delivery, which leads to happier customers and hence improvement in the bottom line. In fact, the next generation in field service is actually expected to be more proactive and less reactive. Read our coming blog posts to know more.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
Healthcare professionals, without a doubt, need some of the most sophisticated and specialized technologies for their trade. Considering the importance of even minutes or seconds in such a profession, getting quick access to patient records, disease or condition related information and the like, can help a great deal in saving valuable time. Be it mobile devices and applications, or regular devices like the stethoscope and pressure testing cuffs, it should have features that address the unique needs of healthcare professionals.
Here are some features that can be included in a healthcare application or device, that can make work for healthcare professionals much easier:
Security Features

– full disc encryption
– a certified smart card reader
– a trusted platform module
These help in protecting both the organization’s as well as the patient’s data, while at the same time providing anytime, anywhere access to important information.
Efficiency-Enhancing Features
A number of hardware features like, audio capture capabilities, with noise cancellation to support leading edge voice-recognition software, can be very useful for healthcare professionals in taking notes even when their hands are full. A built-in barcode reader can help in quick, effective and positive patient-to-patient medication information matching. These features allow health practitioners to be more effective in terms of treatment and care. To a large extent these features also allow health professionals to be more proactive in their approach towards patients as well. Often, patients’ questions and issues can be addressed even before they arise, thanks to such smart features.
Here, efficiencies are achieved in terms of day-to-day activities as well as on an overall basis. Together, they contribute towards more optimized work flows, more savings in time and money, and thus, more personal and focused attention to patients.
External Hardware

Dust and water resistance properties (as per IP 54 ) for their devices can also prove to be useful for the doctors. Antimicrobial coating on the device protects the device from obvious infections as the doctor treats different patients. They will also have to be cleaned with several sanitizing solutions for the best of all users.
Above all these, healthcare professionals need constant and seamless communication among their colleagues as well as among various departments. They need systems that encompass various locations, from in-patient units to out-patient units to operation theaters to labs. They also need different means of communication in their tools, like video calls, emails, text and multimedia messages and the like.
Healthcare devices and tools used by professionals can become one of the main contributors of effective care in organizations if they have the right features. Hardware and software features are both important factors affecting the efficiency of a device or application. Once the right set of features are incorporated, they have to be constantly evaluated and validated, to ensure that only the best development practices and standards are adhered to, so as to maintain a fundamental level of quality and safety, and also to keep the system updated.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
Field service businesses are trying to capitalize on the advantages offered by today’s technologies. Mobile technology, being the most significant among them, has taken the industry by storm, offering increased productivity gains, streamlines work processes, improved field agent communications, increased first-time fix rate, shortened billing cycles, reduced overhead of paper-based field service management and so on. The infographic puts together some recent trends, impacts and state of mobile technology in Field Service Businesses.
Interested in learning more on enabling your field team with mobile technologies? We’d love to know your business requirements and help accordingly, contact our specialist team now.
Share this Infographic On Your Site
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
There were times when common banking activities like withdrawal of money or deposit of money meant time-consuming visits to the bank and waiting in line for hours. As inconvenient and troublesome as that was, it also meant less risk of being cheated and less chances of theft of personal information. Today, we have banking at our fingertips, with mobile banking applications. What we used to do in probably three to four hours earlier, can be done now with a few simple clicks or taps in a matter of seconds and that too from anywhere in the world if you have a smart device and the internet. But how secure are these mobile banking apps and online transactions? Could someone be stealing all the information you send out through such apps?
The truth is that there are various risks of being victims to such cyber attacks, but thankfully mobile banking apps these days are made with several layers of protection and it would take considerable effort for a thief to break in through all of that. Nevertheless, there are some things that you should do too, to make sure that your information is safe and protected while using mobile banking apps. Here’s what you should do for a safe banking experience online:
- Avoid following links and thus phishing – Phishing refers to the practice of acquiring personal and important information such as passwords, usernames and the like by pretending to be a trustworthy person or entity. It basically involves tricking someone into providing sensitive information and then using that information for malicious practices. It is in a way similar to actual ‘fishing’ as both of them involve bait to lure the victim into the trap. The bait in phishing could be a simple text message with an internet link or an email, or even a website, which could even look like your bank’s website (spoofing). You should never follow links on such emails and messages. According to the Federal Trade Commission, these are the most common ways that scammers use to steal private information from you. Legitimate companies and banks never ask for credit or debit card numbers, passwords or social security numbers and the like through emails and texts, so if you see a message somewhat like this:
“We suspect an unauthorized transaction on your account. To ensure that your account is not compromised, please click the link below and confirm your identity.”
DO NOT click on the link. - Download only the official banking app from a reputed site or store – Most leading banks offer their official applications on most smartphone app stores. For a fact, such apps are a lot more safe and secure than other apps and are definitely better than sending SMSs and emails. Banks actually go a long way to ensure that any information entered and sent across through their apps is encrypted. Hence make sure you download only the official app and only from leading well-known app marketplaces, like that of Google’s and Apple’s. Your bank will probably have information about their official app on their website, which you can use to verify the credibility of the app you are about to download.
- Avoid banking through public networks – Public WiFi networks are often not that secure. Even simple banking activities like checking your balance can make your private information vulnerable over the network. Most places that offer such WiFi or hotspot networks often advise their users not to share private information through it. It is always better to switch to your phone’s network in case you have to use your banking app while in a public network, as fraudsters and thieves could also be using the same network and may be waiting to steal your information. Some phones allow automatic switching to WiFi once they are in range of an open one. Hence, make sure you are not on a public network before using online banking apps or sharing any private, sensitive data.
- Avoid having personal data on your phone – For the same reason that your phone is the most convenient tool that you can easily carry around everywhere, it also proves to be sort of a risk sometimes. Your phone can have all kinds of information, like your calendar appointments, your passwords and your contacts. Such information can be read by other apps and other devices if not properly monitored and can be used against you. It also means you should be careful about where you leave your phone. Try avoiding maintaining private information on your phone as much as possible. If at all you have to, make sure you have several layers of protection for your phone. This will at least give you some time to lock your phone in case it gets stolen or lost.
- Make sure you have an updated anti-virus system – Keeping your system up to date with the latest software along with the latest security patches can actually help a great deal in keeping away malicious software and people. It is also good to download an appropriate, trusted antivirus program for your phone as well. That adds as an extra layer of protection to the phone as well.
Keeping all these points in mind, you can very well use mobile banking apps safely. All you need to do is be a little careful and alert. In spite of all this, if you happen to lose your phone, you have the Federal Laws to the rescue. According to CNN, you can recover your losses with a limit of $50 if you report the loss within two days of its discovery. Several banks apparently already have policies in place, that waive the liability completely. Even then, prevention is better than cure, so it’s always better to avoid theft and follow these simple steps while using mobile banking apps.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
Samsung, the South Korean Electronics titan, is reportedly planning to follow the footsteps of Apple. According to Forbes, the company is likely to launch a new smartphone leasing program for its Galaxy range of smartphones in the U.S market. Through this system, Samsung intends to allow its consumers avail a new mobile device, like the Galaxy S6 or the Galaxy S6 Edge on a monthly installment basis. This program is similar to the one launched by Apple less than two weeks ago.
Forbes said, “ Samsung may be launching this leasing program in the next several months, although that timeline may accelerate.”
Apple had announced its iPhone Upgrade Program in September at an event where it also launched the iPhone 6s, 6s Plus, the iPad Pro and an updated version of the Apple TV. As per the program, Apple phone users will be given the privilege of buying iPhones directly from the Apple Store, rather than through carriers. It allows users to get new iPhones every year through Apple Care, with a two-year contract starting at a very affordable rate of $32 a month. Which means, they get to upgrade each year to the latest version if they desire to do so.
Apple’s Upgrade program came at a time when U.S customers were using the lengthy subsidized plans of big wireless carriers for smartphone hardware and a result were locked in two-year contracts. Now, most customers are left with no option but to buy their own hardware, now that the wireless carriers have withdrawn. Such lack of subsidies had led to a decline in sales of high-end phones like Apple’s iPhone and Samsung’s Galaxy series. This was probably what made Apple introduce its own program to enable a larger share of its customers purchase its highly priced hardware easily. So basically, through its program, Apple makes it possible for its customers to upgrade their iPhones on a regular basis, much easily than with the traditional carrier plans and also offer better value than other similar U.S leasing programs like that of AT&T and Verizon.
Now, in the same way, even Samsung plans to make its devices easily accessible to its customers. I would say it’s a smart move as it can attract new customers who are probably looking to get a relief from two-year contracts. Even though Samsung has announced its plan to be released in the next few months, it could arrive sooner than that because the company is working hard to bring its program to the market as soon as possible. However, for the time being, Samsung hasn’t revealed its pricing strategy for the program. Hence, we will have to wait in anticipation to see what Samsung has in store.
So, now that there are two smartphone companies out to provide smartphones on lease, and since customers can hardly wait to avail them, leasing seems to be the new “in” thing. What makes it so popular? How does it benefit users and what are the disadvantages that can inhibit its adoption?
Pros and Cons of Smartphone leasing
The most important factor for the popularity of smartphone leasing is definitely the fact that there is no upfront fees required. Even though you don’t own the smartphone, you can use it for a set period of time, then give it up and upgrade to a new device. The monthly payments are also quite reasonable which makes it affordable for everyone. Also, you get frequent and sure shot upgrades, almost every year, with the option of purchasing the phone at the end of the period. Of course, it all depends on the lease plan which varies with each carrier. When you own a smartphone, you only have the option of upgrading your phone every two years. With all these benefits, more people are moving towards leasing rather than owning smartphones and spending a lot of money on them. When there is an option to rent or lease technology, people would most certainly choose to go for companies that can provide such benefits.
Although, the fact that you don’t own the device is a major con, as you need to return the phone in good condition at the end of the lease period even it is for an upgrade. The customer will be held liable for all damages which is not the case when you actually purchase a smartphone. Moreover, you can only terminate the lease agreement upon paying the balance amount of the lease and the phone.
Nevertheless, leasing is definitely becoming a much preferred and popular means to use a smartphone. Especially since the leaders in the industry are set to make it easy and affordable.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
With great power comes great responsibility. We’ve all heard of that haven’t we. Well, here is a little modified version of that – “With great benefits come great risks”. Yes, it’s true. Especially in the case of mobile payments. While we are all basking in the glory of the “great benefits” accruing from the digitization of world of payments, the flip side of things is often overlooked. How many of us know the risks associated with mobile payment portals?
Let’s just say it’s complicated. One thing to keep in mind though, is that, irrespective of what industry it is, new developments in technology mean new vulnerabilities and risks and the only way to move forward is to be well aware of them and find ways to deal with them. I’m going to take you through some risks associated with mobile payments here. Before that, let’s take a look at how mobile payments work.
How does it work
Mobile phones contain a Near Field Communications (NFC) chip inside, which stores the bank information or debit/credit card information securely. NFC is a short-range wireless technology used for communication between various digital devices. When a consumer makes a purchase, the NFC chip transmits the relevant information through wireless technology, as the consumer enters the range of a retail register. It is similar to the Radio Frequency Identification Technology (RFID) used in contactless credit cards and transit cards.
Risks involved
First of all, the GSM or CDMA standards used by the service payment providers may be the primary cause of risks or vulnerabilities. Many service providers often use messaging protocols along with their data transmission systems for the sake of convenience or ease. But they fail to provide the required level of security encryption, which makes it easy for frauds to break in and steal important information, like for example payment authentication information.
Another issue with mobile payments is shoulder surfing and device theft which involve spying on the users of cash-dispensing machines or any other electronic devices and obtaining their Personal Identification Number (PIN) or passwords and the like. Sometimes such spying can take place even through malware like malicious programs, viruses, and other such invasive software. This risk can be avoided through an appropriate antivirus software or by using trusted sources for downloading applications.
The Point of Sale (POS) terminal device used by NFC technology in mobile payments is another risk. These terminals may get hacked and can be used within probably a distance of 20 centimeters from your device. This increases the chances for other malware to be uploaded onto your device, which in turn leads to fraudulent NFC transactions in the same name. Such risks can be minimized by having a bilateral system authentication before making a mobile payment. It also helps to keep away from false payment requests. As a matter of fact, the source of the payment request needs to be checked properly for its genuineness, as it is a clear indicator of a risk.
Then there are regular risks associated with payments as well, like the chances of someone else’s expenditure being charged to your account or the same purchase being charged twice to your account and the like. Such risks arise irrespective of whether you swipe a card to make a purchase or whether you make contactless payments.
Mobile payment basically brings with it a lot of risks along with benefits and conveniences. A major concern of the people regarding mobile payments is having to disclose a lot of personal information in order to make purchases easier. Such information, once fed into a mobile wallet stand the chance of being used by other applications in your mobile device as well, if not properly protected. Most of the time, people ignore the permissions page while downloading an app and grant permissions to Apps straightaway without reading them. Sometimes, it doesn’t even make sense for apps to request permission to access certain information that is clearly not necessary for it to function. But we tend to overlook this in the urge to install applications that we find interesting, without even knowing how our private data can get compromised through such apps. It would help to read through these once before installing apps so as to minimize the risks of your personal details being shared.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
As the reign of mobile applications and mobile devices continue, we, as part of this revolutionary trend, have to keep ourselves updated about everything latest in the mobile world, don’t we? Of course we do. We also have to be aware of everything we need to in this regard. I’m talking about mobile applications and their making. Continuing my endeavour to make you guys acquainted about the many processes and resources that go into making a mobile application, here I’m going to give you some more information on mobile application testing.
In one of my previous articles, A winning mobile testing strategy: The Way to Go, I had explained the various steps involved in the process of testing and the article, and Mobile Application Testing: Challenges and the Solution had the major challenges faced by testers.
Now, for those of you who read through the testing process, in case you are wondering “what other kinds of testing are there?”….
Here is a list of the most commonly used kinds of mobile application testing. Do keep in mind that all of these tests are conducted to perfect different aspects of an application. Hence, ideally a combination of some of these would probably be the best way to go.
- Functionality testing – This is actually the most basic kind of testing for any application, as it ensures that the basic functions of the app work as intended. As is the case with any user interface based application, mobile applications work on the basis of several human interactions as well. All of these functions need to be tested for their accuracy. Considering the challenges faced by testers, like the wide range of mobile devices for example, functionality testing is usually a time-consuming and intensive process if it is done manually. However, there are various automation tools available in the market for functional testing as well.
- Usability testing – This is conducted in order to ensure that the mobile app is easy to use and provides a good user experience to the customers. It basically tests the app from three angles:
Satisfactory user experience – The user acceptability level or comfort level of the application and also others affected by its use.
Effectiveness – The level of benefits achieved through the app in comparison to the level of resources expended for it.
Efficiency – The accuracy of the application in terms of its ability to achieve specific goals in specific environments. - Performance testing – This covers testing of performance of the application from the client side, server side as well as network. The client side will focus more on things like, responsiveness of the application, user interface elements etc. It also involves testing with different types of data connections, WIFI, levels of battery consumption etc. There are again a number of tools available to carry out testing in these areas.
- Compatibility testing – This is conducted to see whether the application works as intended in different devices, Operating systems and their different versions, browsers and screen sizes.
- Security testing – This is carried out to test whether the application is capable of storing and protecting information.
- Memory testing – This is important to ensure that the application maintains optimum memory usage throughout its life. Mobile devices usually tend to have very limited memory and the operating systems also have a tendency to stop applications that use too much memory, which might lead to problems with user experience.
- Regression testing – This is done in order to bring to light any bugs or errors that may exist in already built modules of a project after making changes such as improvements, enhancements or configuration changes and the like.
There are also other kinds of testing, like services testing, user interfaces testing, operational testing etc. which are also done in some cases depending on the kind of mobile application. Apart from that, the most commonly used tests are listed above. As a general rule, functional testing is often conducted first followed by performance testing and the rest. Like i said before, not all of these tests might always be conducted in order. It all depends on the application. The basic point is that testing is a huge and significant part of mobile application development, and at no cost can this be avoided.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new