Cloud Security Best Practices | Why is cloud security important?
How can companies ensure cloud security amid cyber threats and malicious online activities?
The explosion of the cloud has changed the face of the business process as we know it. Nearly 90% of companies rely on the cloud. And yet, there has been some skepticism around cloud security. With recent breaches and technological attacks, maintaining cloud security has become the foremost concern for businesses worldwide.
Security experts at Fingent understand your concern, and so we have put together this blog about the importance of cloud security and the best practices which will ensure that you are secure on the cloud.
Why is cloud security important?
According to a report by Cisco, cloud data centers process 94% of all workloads. Despite the popularity attained by cloud technology, most of these companies are skeptical about cloud security. There is a reason for this. Statista reports the number of data breaches in the U.S alone increased to 156 million in 2020. It has also been reported that hackers attack every 39 seconds. This can be fatal to businesses in the following ways:
1. Managing remote work
Remote work lets you hire talent from across the globe. However, this arrangement entails inherent security risks. Using personal devices may expose your data to malware and phishing attacks. If a malicious virus enters through them into your cloud system, the damage done could cut your company off at its knees.
Read more: Why It’s Time to Embrace Cloud and Mobility Trends To Recession-Proof Your Business?
2. Security breaches
If your company chooses to run your application on a public or hybrid cloud, you are entrusting a third-party to take care of your data. This means you no longer have any control over data security. So it is critical to stay on top of things and ensure that your cloud computing provider is serious about this responsibility. Even when you know your provider will ensure top-tier security, it is your responsibility to verify that your data is secure as a client.
3. Comply with regulations
Data protection standards were put together to ensure the integrity and security of customer data. When you store your customer data on the cloud, it is your responsibility to keep it secure, especially if your organization belongs to a highly regulated industry like finance, insurance, banking, or legal. A data breach will destroy your reputation and brand because external parties will hold you accountable.
4. Build access levels
Unintentional leaks of data will compromise your business integrity and give your competition a leg up. Limiting data access only to those employees who need it can prevent errors that lead to data leaks.
5. Disaster recovery
Disasters such as flooding or fire can strike without warning. Unless your data is secured and protected, you could lose all your data. This may undermine customers’ confidence in your organization, delivering a death blow to your otherwise successful business.
Read more: How Secure is Your Business in a Multi-Cloud Environment
Best practices to ensure cloud security
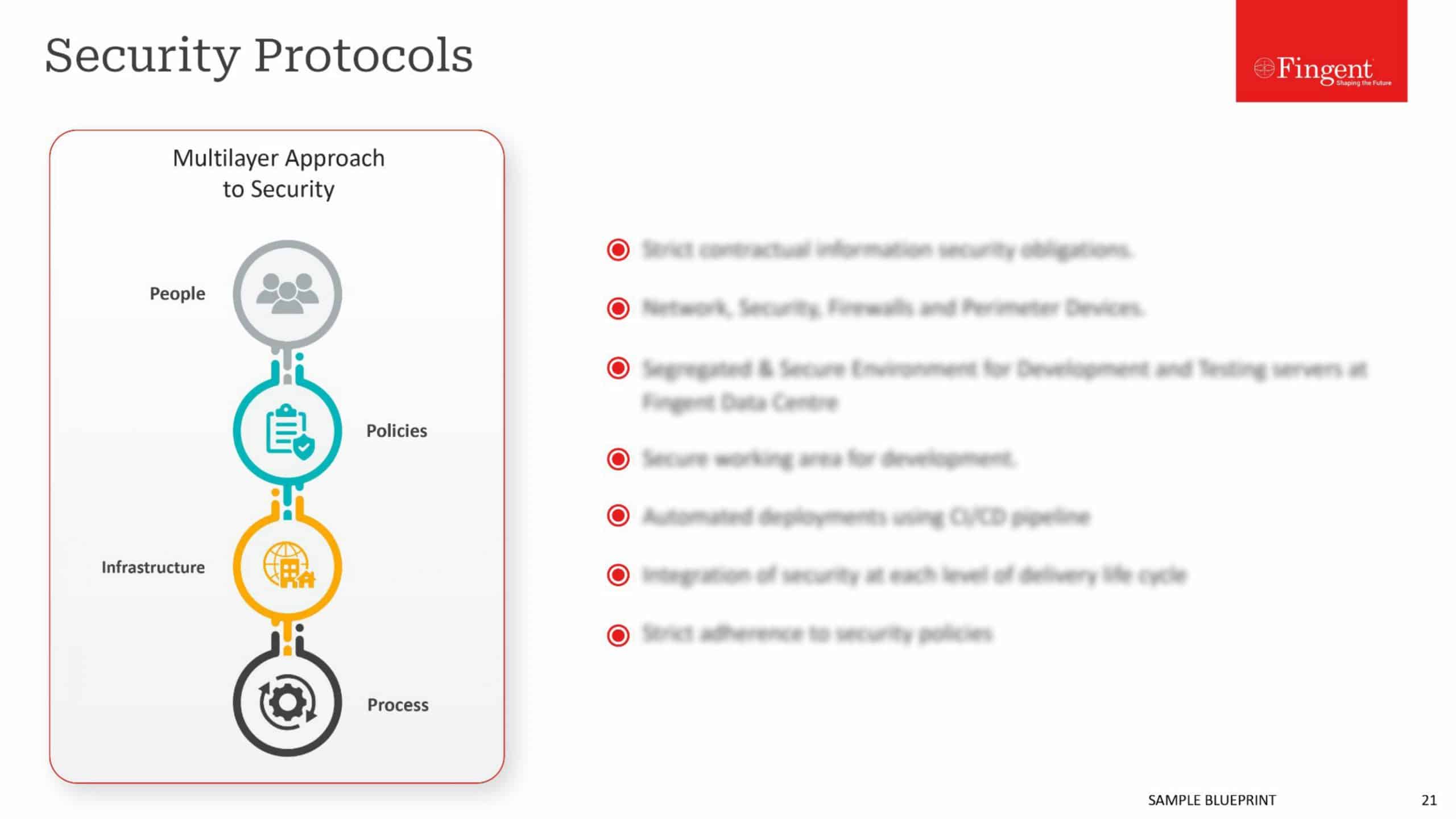
- Carefully choose a trusted provider
- Review your cloud security contracts and SLAs
- Understand your partnership of shared responsibility
- Control employee access
- Secure user endpoints
- Maintain visibility of your cloud services
- Implement a strong password security policy
- Highest levels of encryption
“Cloud computing is a challenge to security, but one that can be overcome” – Whitfield Diffie, an American cryptographer.
True to Whitfield Diffie’s words, cloud security measures can be taken to encrypt the system that will help achieve adequate cloud security.
1. Carefully choose a trusted provider
Partnering with a trusted provider is the foundation for cloud security. Choose a partner who delivers the best in-built security protocols and follows industry best practices’ highest levels. You need to ensure that you confirm their security compliance and certifications.
Learn more: Take a look at how InfinCE, an infinite cloud platform, ensures secured work-collaboration within an organization and helps enhance company efficiency & growth!
2. Review your cloud security contracts and SLAs
In an event, SLAs and contracts are the only guarantees of service and course of assistance. 62.7% of cloud providers do not specify that customer data is owned by the customer, creating a legal grey area. Read through the terms and conditions, annexes, and appendices to ensure who owns the data and what happens if you terminate the services. Also, seek clarity on visibility into any security events and responses.
3. Understand your partnership of shared responsibility
When you tie-up with a cloud service provider, you enter into a partnership of shared responsibility for security implementation. Understanding the shared responsibility involves discovering which security tasks you will handle and which your provider will handle. It is important to ensure transparency and clarity in your partnership of shared responsibility.
4. Control employee access
Implementing strict control of user access through policies will help you manage employees who attempt to access your Cloud services. Cloud security best practice starts from a place of zero trust. Afford user access to data and systems only to those who require it. To avoid confusion and complexity, create well-defined groups with assigned roles. This will allow you to add users directly to the group rather than customizing access for each employee.
5. Secure user endpoints
Since most of your users access your cloud services through web browsers, it is crucial to introduce advanced client-side security to keep it protected from exploits. Implementing endpoint security solutions that include firewalls, antivirus, intrusion detection tools, and more will help to protect your end-user devices.
6. Maintain visibility of your cloud services
Remember, you cannot secure something that you cannot see. Using multiple cloud services across various providers and geographies can create blind spots in your cloud environment. Make sure you implement a cloud security solution that provides visibility of your entire ecosystem. You can then implement granular security policies to mitigate a wide range of security risks.
7. Implement a strong password security policy
Strong password security may sound basic, but it is an important element in preventing unauthorized access. Have a strong and strict password policy. To defend against most brute force attacks, enforce a rule that users update their password every three months. You may also implement multi-factor authentication. This would require a user to add two or more pieces of evidence to authenticate his/her identity allowing you to trust your users while ensuring that they are authorized users.
8. Highest levels of encryption
Your data may get exposed to increased risk while sending it back and forth between your network and the cloud service. You must consider using your own encryption solutions for data, both in transit and at rest. Encryption keys will help you maintain complete control over your data.
Read more: 6 Proven Ways for Businesses to Combat Cloud Security Risks
Don’t wait till it’s too late!
You never know when a stealthy hacker could attack your business and make you go under. All organizations, independent of their size, can benefit from these best practices and improve their cloud usage security.
At Fingent, our custom software development experts go above and beyond to ensure that your business is hacker-proof and secure. If you need to discuss cloud security options, do not put it on the back burner! It could creep up on you and set your whole business afire, ruining your competitive edge and spelling doom for the future. Call our experts and discuss your options today.
Stay up to date on what's new

Recommended Posts

05 Nov 2023 B2B
Cloud 101 – Getting a Good Return on Your Business Cloud Investment!
In the digital age, cloud investment is your business's propulsion, offering flexibility, scalability, and a competitive edge. However, many companies don't fully reap the cloud's benefits. The cloud's potential remains……

15 Oct 2023 B2B
Hyperscaler Cloud Services: The Next Step In Business Cloud Investment!
Companies can save 20% of the total annual cost if they migrate to the cloud. Hyperscaler Cloud Services can enable businesses to experiment, build, innovate, and run any form of……

10 Oct 2023 B2B
Guarding Your Digital Fortresses: The Imperative of Application Security
In the ever-evolving landscape of cybersecurity, application security stands as the impervious armor that shields your organization's digital fortresses. Imagine your organization's applications as the kingdom's gates – if left……

30 May 2023 B2B
Cloud Application Development: Empowering Your Business In The Digital Era!
“Cloud computing is really a no-brainer for any start-up because it allows you to test your business plan very quickly for little money. Every start-up, or even a division within……
Featured Blogs
Stay up to date on
what's new