Tag: cloud security
- Companies can save 20% of the total annual cost if they migrate to the cloud.
- Hyperscaler Cloud Services can enable businesses to experiment, build, innovate, and run any form of application.
- Hyperscaler adds immense value when creating custom software applications with a specified focus on the data center hardware and software needs.
Organizations of a variety of sizes are now able to reinvent how they operate and move more quickly and more agilely, thanks to the cloud. The move to the cloud has fundamentally changed how we perform our jobs, communicate, and interact. It is quickly becoming a requirement to be competitive in today’s digital environment.
Custom software applications powered by the cloud are a force to be reckoned with, and the benefits become manifold with hyperscalers like AWS, Azure, and Google. What are these hyperscalers, and how can they supercharge your business? Let’s find out.
What are Cloud Services?
In very simple terms, cloud computing is access to computer services such as servers, storage, databases, networking, software, analytics, intelligence, and more by means of the cloud (the Internet). With cloud computing, you can store and access data and programs on remote services hosted on the internet rather than the computer’s hard drive or local server. Cloud computing can be done with cloud services, which are essentially software programs that are hosted by third-party providers who make them available to users over the internet.
Studies recently revealed that, on a worldwide scale, 94% of all companies will use some kind of cloud computing service in 2023 to help them run their business operations. This is a 14% jump from 2020.
A major reason for this wide shift from on-premises servers of the companies to cloud providers is the ‘Pay as you go’ service offered by them, meaning that you only have to pay for the service that you are utilizing. However, the cloud offers more, much more!
How Does the Cloud Work and How Does it Benefit Businesses?
Just like any other IT solution, cloud services also rely on hardware and software. Users typically need just a computer, a stable internet connection, and operating systems to access cloud services.
Benefits To Businesses:
- Cost Reduction: This is a major factor that makes this technology desirable. On average, 20% of the total annual cost can be saved by companies if they migrate to the cloud.
- More Storage: Many tools are available on the cloud with the sole purpose of providing more storage capacity. Some examples include Dropbox, OneDrive, Google Drive, and iCloud Drive.
- Higher Security Barricades: Another attractive feature of cloud services is their tight security regulations. A report by Salesforce states that 94% of businesses claimed to have seen an improvement in security after adopting cloud services.
Read more: Advance your business software development with Cloud Native. Download the complete 451 Research now and strategize a successful Cloud Native adoption process.
Hyperscalers: What Are They, And How Do They Add Value To Cloud Services?
Hyperscaler got its name from the data processing method known as “hyperscale computing,” which allows software architecture to expand and scale on an enterprise level. Hyperscalers enable their clients to experiment, build, innovate, and run any form of application—from a social network to a smart city to online banking—while controlling costs and operating with agility by offering users access to a ready-made, scalable infrastructure. Some famous examples of hyperscalers are Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP). These technologies combined are reported to have an estimated 65% control over the cloud market.
Benefits Of Hyperscaler Cloud Services:
- Scalability: They can provide virtually unlimited computing resources, which enables organizations to scale their services and applications swiftly without worrying about hardware constraints.
- Global Availability: Users can easily access content with lower latency through hyperscalers, which boosts efficiency and user satisfaction.
- Security: Hyperscaler clouds provide a high level of security by frequently investing in infrastructure reliability, disaster recovery, and cybersecurity.
Value Added By The Big Three: AWS, Azure, and Google
Let’s now talk about these three hyperscalers:
AWS: Four primary elements of value—cost savings, employee productivity, operational resilience, and business agility—are measured and tracked by AWS to assist enterprises in developing an in-depth case for the cloud.
Azure: Azure is the only consistent hybrid cloud that delivers exceptional developer productivity, offers extensive, multi-layered security, including the most conformity coverage of any cloud provider, and costs less than AWS.
Google: Google’s solution provides a complete data foundation for unifying all workloads and overseeing the entire data life cycle. It can process data anywhere and is designed with and for AI, so you can obtain the most up-to-date tools for machine learning analysis, prompting, adjusting, training, and deploying unique foundation models—all while being connected to your business data.
How Can Custom Software Applications Benefit From These Hyperscalers?
Hyperscalers generally oversee the in-house technical skills of an IT team needed to customize data center hardware and software in accordance with the company’s business model and applications. This adds immense value when creating custom software applications.
AWS:
AWS offers many tools you can use to build custom SaaS applications and third-party SaaS solutions.
- Cognito: enables organizations to provide extra sign-in alternatives to their users.
- AD Connector: adds an extra degree of security.
- Quicksight: is a BI solution that you can use to provide simple insights to the people who work with you.
- Cost Explorer: displays and analyzes your costs and operations.
- Aurora Serverless: takes care of routine database chores, including provisioning, patching, backup, recovery, failure detection, and repair.
Azure:
Azure services can assist you throughout the process of custom software application planning, development, delivery, and operations.
- Github: It is a programming solution for collaboration and version control that allows you and others to work on projects from anywhere in the world.
- Azure Pipelines: Works with any language or platform and is used to simultaneously deploy services to multiple targets.
- Azure Boards: This tool lets teams organize, monitor, and talk about their work across the whole development cycle.
- Azure Monitor: This helps improve the responsiveness and availability of your services and apps.
- Visual Studio: This can be used to connect applications and services to Azure and create services that operate in the Azure cloud.
Google:
To help you create high-quality apps as quickly and dependably as possible, Google provides a wide range of resources.
- Firebase: It is used for cloud communications, performance monitoring, and authentication validation.
- Web: It offers information to assist you in enhancing your site’s organization, how it appears in Google searches, and the effectiveness of its user interface.
- The Cloud: Here, you can access services like BigQuery (for processing large, ready-only data sets), Compute Engine, and Cloud Storage.
- Tensor Flow: This tool is mostly used for machine learning and gives developers access to a variety of workflows and high-level, logical APIs to build machine learning models in a variety of languages.
Why Should You Choose Fingent?
Fingent is one of the top providers of technology solutions around the globe right now, serving customers from four different continents. To assist you with your projects, we provide top client-centered personnel who can help you with any of the three types of Cloud services – SaaS, PaaS, and IaaS.
With our team of experts, you can scale up or down as you need and manage and integrate cloud environments according to your business needs. We provide excellent pre- and post-development support by monitoring performance and making any necessary adjustments, and we are accessible at any level of development.
Give us a call, and let’s talk about how to get your business to succeed on the cloud.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
In the ever-evolving landscape of cybersecurity, application security stands as the impervious armor that shields your organization’s digital fortresses. Imagine your organization’s applications as the kingdom’s gates – if left unguarded, they become vulnerable entry points for malevolent forces. We understand that as a CIO, CTO, or IT Manager, you take your duty seriously to ensure these gates are fortified.
In order to assist you in this regard, in this blog, we will delve into the realm of application security and shed light on the importance of each layer of defense. We will also explore how a proactive approach to application security can save your organization from potential disasters.
Why Application Security is a Concern
In an era marked by rapid digital transformation, applications have become the lifeblood of businesses. They manage sensitive data, perform critical functions, and are often the first line of interaction with customers. However, these very assets can be exploited if not adequately secured.
Just as the strength of a fortress determines its ability to withstand attacks, the security of your applications dictates your organization’s resilience against cyber threats. Data breaches, unauthorized access, and system vulnerabilities have become common adversaries in today’s digital age.
Picture this: By 2023, ransomware attacks had hit an astonishing 72% of businesses worldwide, marking a significant rise over the past five years and setting a record high. This emphasizes why application security must be at the forefront of your defense strategy.
The consequences of such breaches are dire, leading to financial losses, reputational damage, and regulatory penalties. According to studies, in 2023, data breaches cost companies worldwide an average of USD 4.45 million, showing a worrying 15% increase in just three years. This statistic underscores the urgency of investing in robust application security measures. So, how can you be prepared?
The Building Blocks of Application Security
The Foundation: Architecture Choices
Every castle begins with a strong foundation, and the same principle applies to application security. The architecture choices you make at the outset are akin to building a formidable fortress. An ill-conceived architectural design can leave cracks in the walls for attackers to exploit.
Just as an architect meticulously plans the layout of a castle, your development team should consider security measures when designing your applications. A single weak link in your architectural chain can lead to disaster. Empirical data reveals that a significant 50% of vulnerabilities stem from poor architectural decisions.
Investing time and resources in designing secure architecture is a proactive approach that can significantly reduce the likelihood of security breaches down the line.
1. Building Strong Walls: Coding Practices and Code Organization
The walls of a fortress serve as the primary defense against intruders. In the world of application security, coding practices and code organization are your virtual walls. Sloppy coding practices create chinks in the armor, allowing malicious code to infiltrate your application.
What can you do?
Imagine coding as the masonry work – each brick (line of code) must be laid meticulously to ensure structural integrity. Security breaches can often result from code vulnerabilities. Ensuring your development team adheres to secure coding practices is akin to reinforcing your fortress walls.
Implementing secure coding practices, conducting regular code reviews, and enforcing coding standards can mitigate vulnerabilities. Training developers in secure coding practices is a crucial step in enhancing your application’s security posture.
2. The Gates and Drawbridges: Library Updates
Just as a castle’s gates and drawbridges are essential entry points, your applications rely on third-party libraries and components. These elements, if left unguarded, can become weak points in your security defenses.
Applications often rely on third-party libraries and components. A concerning fact is that out of about 433,000 websites analyzed, 77% of them use at least one front-end JavaScript library with a known security issue.
Think of libraries as the mechanisms controlling the gates of your fortress. Failing to update them is like leaving the drawbridge down, making it easy for attackers to breach your defenses. Regularly updating these libraries is similar to raising the drawbridge and securing your gates against unwanted visitors.
Additionally, employing automated tools to scan for vulnerabilities in third-party dependencies can help identify and address issues promptly.
3. The Watchful Guards: Application Security Program Management Solutions
Medieval fortresses had vigilant guards patrolling the battlements. Similarly, modern organizations require robust application security program management solutions to keep a watchful eye over their digital assets.
A stark reality: 66% of CIOs are ramping up their investments in cybersecurity. This surge in adoption underscores the growing recognition of the importance of a structured approach to application security.
So, think of these solutions as your digital sentinels, tirelessly scanning for threats and vulnerabilities. These systems serve as your first line of defense, ensuring that potential threats are identified and neutralized promptly.
Read more: A CTO’s Guide To Secured Software Development
How Fingent Helps Fortify Your Digital Kingdom
Without a robust application security strategy in place, your organization is vulnerable to attacks that could have far-reaching consequences.
Just as medieval kings relied on skilled architects, craftsmen, and sentinels to protect their castles, you can depend on Fingent to safeguard your digital kingdom.
At Fingent, we understand the importance of application security, and our expertise in secure architecture design, coding practices, library updates, and application security program management ensures your digital fortresses remain impenetrable. With a deep commitment to security, we offer cutting-edge solutions to protect your digital assets.
In this age of digital warfare, application security is not just an option; it’s your shield against an ever-growing army of cyber threats. Fingent can be your trusted ally in this digital battlefield.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
“Cloud computing is really a no-brainer for any start-up because it allows you to test your business plan very quickly for little money. Every start-up, or even a division within a company that has an idea for something new, should be figuring out how to use cloud computing in its plan.” – Brad Jefferson, Animoto CEO.
Cloud Application Development, originally known as the modern cloud, was first invented in the 2000s. Today, “The Cloud” denotes servers that can be accessed through the Internet and the crux software and databases that are the backbone of those servers.
The cloud has consistently grown from its genesis and is currently the backbone of many leading organizations. In this article, we will look at Cloud Applications developments, their basic framework, advantages, best practices, challenges, and benefits.
What Is Cloud Computing?
As the name suggests, cloud computing is the distribution of various software services and the ability to access them proffered by cloud service providers to users or customers over the internet. These infrastructures include tools and applications like software, servers, data storage, networking, artificial intelligence, analytics, and databases. They essentially provide faster progress, more flexibility, and drastically reduce operational costs.
Read more: Choosing the right Cloud Service Model for your business – IaaS, PaaS, SaaS.
Types Of Cloud Services
There are three main types of cloud settings that are used widely for their efficiency and are generally referred to as “models for cloud development.”
1. IaaS –
Infrastructure-as-a-Service offers access to essential network structures on the cloud, like storage space, virtual servers, links, and networks for enterprises. All of this can be done without the business needing to purchase or maintain the internet infrastructure.
IaaS is also the oldest and most basic cloud computing model. Examples of businesses that utilize IaaS include Google Compute Engine, Azure Virtual Machines, and AWS EC2.
2. PaaS –
In Platform-as-a-Service service, developers can build or create a cloud application development framework and customize the software however they desire. In the PaaS model, software developers or services rent a cloud solutions company to develop an application.
The cloud solutions company then uses the infrastructure and operating systems to create development tools that offer better computing, database, memory, and data storage. Some examples of PaaS providers are Windows Azure and AWS.
3. SaaS –
Lastly, the Software-as-a-Service model delivers cloud software that grants users access to the internet without needing to install or maintain them. It is well known for its applications that can be built or developed even on a local terminal and deployed to a cloud-based server. Slack, MailChimp, Gmail, and Salesforce are a few examples of SaaS products.
Benefits Of Cloud Computing
Cloud Computing is by far the most cost-effective path that small or large organizations can take. Saving as much money as possible and cutting costs is a vital requisite for any business, and Cloud Computing can evidently help there. Aside from this, Cloud Computing also has other benefits:
1. High Availability
High availability in a system is undoubtedly a strong benefit for an organization as it will face negligible downtime. Downtime in cloud-based services is counted in seconds instead of minutes or hours.
“The primary benefit of moving an organization’s services to the cloud is near real-time deployment capabilities in a highly available architecture.” – John Breth Founder/Managing Principal at J.B.C.
2. Faster time to market
In a cloud-based application, developers can create new instances or retire them in mere seconds, allowing them to efficiently accelerate development with quick deployments. Cloud computing also supports new innovations and provides a platform for the easy testing of new ideas and designs without hardware limitations or slow retention processes.
3. Reliability
Reliability refers to how well a service can keep up with the promises it makes while performing tasks. It also fortifies highly available databases from randomly corrupting data records or deleting reports. Cloud computing proffers regular upgrades, updates, and damage control patches and tests its applications to make sure its services are perfect as promised.
4. Data loss prevention
Data loss is a major headache for most organizations and can lead to many complications, but Cloud computing can help here as well. With cloud computing, your data backup is up-to-date and disaster recovery is exceptionally fast. Uploading data into the cloud for storage can help prevent data loss even during emergencies, such as hardware malfunction, malicious cyber attacks, or simple user errors.
5. Automation
A great vantage in the world of technology is automation. This makes machines with quick automation a highly sought-after commodity. Every Google Cloud, IBM, AWS, and Azure product has a built-in API interface that makes it programable. Developers simply need to create, configure and demolish cloud-based resources with Software Development Kits (SDKs) written in Java, Python, JavaScript, and C++.
What is Cloud Application Development?
Now that we know the amazing benefits of the Cloud, let’s get into what Cloud Application Development is.
Cloud Application Development essentially is the creating, testing, deploying, and running of software services in the cloud. They are called cloud software because these applications are built in a cloud-based environment. Cloud Application Development involves various stages of software development; each of these stages devises the application to go live and hit the market successfully.
The biggest beneficiaries of cloud applications are business owners. This technology allows businesses to simplify their operations and gradually enhances their bottom line. Cloud-based applications also provide flexibility and enable you to adapt to the latest business trends in order to keep up with competition. Hence, most businesses have started to transition from on-premise to cloud-based software development methods.
Read more: Cloud Native: The Modern Way To Develop Software
Cloud Application Development Framework
Cloud App Development Framework is the tools and technologies needed to create, control, and administer cloud applications. The tools provided by Cloud Application Development Framework include developmental tools, middleware technology, administration managing software, and various other Cloud Applications.
Some of the more popular Cloud Application Development Frameworks are:
1. Java
Java frameworks, such as J2EE, Hibernate, and Spring are generally used by beginners because these frameworks make the whole development of strong cloud computing applications process very easy.
2. Azure
Azure is a famous platform that provides excellent security to cloud computing applications. Developers using this framework can easily integrate applications, systems, and data.
3. Google Cloud
The Google Cloud Architecture Framework is most famous for its best practices of secure, efficient, resilient, high-performing, and cost-effective applications.
Advantages Of Cloud Application Development
There are many advantages of Cloud Application Development but listed below are 5 of the most important and prominent ones:
1. Scalability
Scalability in terms of Cloud Computing refers to the ability of the application to increase or decrease IT resources when demands change. It is one of the greatest features of the cloud as it allows users to scale many machines and processing power simultaneously, making it a highly flexible service.
2. Cost Effectiveness
Business owners should be very mindful of their expenses and making smart decisions in order to curb extravagant expenses should be second nature to them. Cloud Application Development is extremely cost-effective as it follows a pay-as-you-go technique. Here the costs of using the cloud application are reflected directly in the needs of the customer, making the initial transition to a cloud service less complicated and pocket-friendly.
3. Security
The Cloud is widely famous for its airtight security and the secret lies in its method of data encryption and transfer of data over networks and storage databases. A report by RapidScale claimed that 94% of businesses noticed a big jump in security after switching to Cloud Computing Applications, and 91% stated that the Cloud makes it easier to abide by government compliance requirements.
4. Flexibility
Cloud Application Development proffers organizations with extreme flexibility and overall agility. Its top-notch flexibility and improved freedom make a significant impression on the overall efficiency of an organization. A survey conducted by InformationWeek said that “65% majority of respondents stated that the ability to quickly meet business demands was the most important reason a business should transition to a cloud-based environment.”
5. Accessibility
Due to its previously discussed scalability and flexibility, Cloud Application Development is highly accessible. The Cloud grants users the ability to quickly and easily use and store information anywhere on the internet. An internet cloud infrastructure is reportedly known for increasing an organization’s overall productivity and efficiency simply by making its data easily accessible.
Best Practices For Cloud Application Development
The better a Cloud Application Development process is, the more resilient and reliable its application is most likely to be:
- Understanding Business Needs And Requirements:
It is very important to first analyze your business needs and requirements before making any drastic investments. Understand the premise of your technological needs and check your organization’s budget before making the transition to cloud-based application development.
- Leveraging The Right Cloud Services And Tools:
Leverage your option in Cloud Services and look for the most beneficial and trustworthy service. Each service has its own data and supports a specific business goal. Ensure that these goals align with your own business goals.
- Building For Scalability And Flexibility:
Remember to keep maximum scalability and flexibility in mind when developing your Cloud Application. We have already seen how important these two factors are when it comes to the overall success of a business.
- Emphasizing Security:
Security of the highest quality is the most important factor when developing a cloud application. Secure your business data and emphasize to your partner the importance of data protection. Look for solutions that will respect your need for top-notch security and will provide it perfectly.
- Implementing Automation And Monitoring Tools:
Artificial Intelligence and many more emerging technologies are on the brink of changing the course of the world completely. Ensure to reap the benefits of these technologies as much as you can while developing a cloud application. These technologies can acutely benefit with automation and monitoring of cloud-based applications.
Challenges In Cloud Application Development
Just like any internet application, even cloud applications have their fair share of challenges during development. Listed below are a few of those challenges:
1. Security and Compliance
Security and Compliance of information is the biggest challenge in cloud application development because of its complicated nature and various operating conditions. These security issues can be rectified by employing encryption, security hardware, and security applications. Users should never cut corners when it comes to security practices when developing a new Cloud Application.
2. Integration With Legacy Systems
Since enterprise solutions have new applications that replace the legacy side of older applications and since these legacy systems were built without an API approach, it results in the older applications not being able to process newer, more modern technology applications such as IoT apps, Saas apps, and other similar applications.
3. Resource Management
The scale of modern data centers, the diversity of resource types, and their independent features, and in addition to this, the wide range of objectivities differ from one cloud ecosystem to another. All of these factors, put together, create a wedge in resource management.
4. Choosing The Right Cloud Service Provider
Finding a cloud service provider that is good at communicating and interpreting your business needs is rare but integral. It does not matter how long you take to find this perfect partner, patiently scrutinize all your options and look for a capable service provider.
Best Practices For Cloud Application Development
The better a Cloud Application Development process is, the more resilient and reliable its application is most likely to be:
1. Understanding Business Needs And Requirements
It is very important to first analyze your business needs and requirements before making any drastic investments. Understand the premise of your technological needs and check your organization’s budget before making the transition to cloud-based application development.
2. Leveraging The Right Cloud Services And Tools
Leverage your option in Cloud Services and look for the most beneficial and trustworthy service. Each service has its own data and supports a specific business goal. Ensure that these goals align with your own business goals.
3. Building For Scalability And Flexibility
Remember to keep maximum scalability and flexibility in mind when developing your Cloud Application. We have already seen how important these two factors are when it comes to the overall success of a business.
4. Emphasizing Security
The highest quality security is the most important factor when developing a cloud application. Secure your business data and emphasize the importance of data protection to your partner. Look for solutions that will respect your need for top-notch security and will provide it perfectly.
5. Implementing Automation And Monitoring Tools
Artificial Intelligence and many more emerging technologies are on the brink of changing the course of the world completely. Ensure to reap the benefits of these technologies as much as you can while developing a cloud application. These technologies can acutely benefit with automation and monitoring of cloud-based applications.
Use cases – Cloud Application Development
1. Enterprise Applications
Major examples of Enterprise Applications are Enterprise Dynamics 365, WordPress, and BambooHR, among many others.
2. Mobile Applications
Amazon, Shopify etc, are examples of mobile cloud computing and when we use our phones or tablets to track our account balance or make a purchase on e-commerce platforms, we interact with these applications.
3. IoT Applications
IoT device systems, including Google Nest or Alexa, are examples of IoT applications running on a cloud base. They collect data on the house’s energy usage, analyze the gathered data and make suitable suggestions to the homeowner on how to manage energy consumption.
4. E-commerce Application
Elastic Beanstalk from Amazon Web Services is used for its online storefront, web apps, and API structure. With this application, online vendors need not know anything about network maintenance to launch and control customized applications quickly.
How Can Fingent Help?
Fingent top custom software development company is a world-renowned service provider with stable markets and satisfied customers on four continents. Our experts utilize the latest and fast-emerging advanced technology to make your project development process easy and flawless. Their experience in cloud-based technology will aid your business in exploiting all aspects of the cloud. We have our own unique approach to developing a cloud application and have countless customers with happy reviews to back them up. Give us a call, and let us get talking.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
Technology trust is a good thing. Traditional approaches focused on establishing a strong perimeter to keep the bad guys out are no longer enough. In today’s digital world, Zero Trust Security is an approach that is essential for every business that has an online presence. Zero trust is a holistic and strategic approach to security that verifies every person and device that is granted access and confirms who and what they say they are. This blog explains why there is an increasing need for app security and 7 reasons why businesses need the Zero Trust Security paradigm.
Is There an Increased Need for App Security?
Cloud environments host business-critical applications and data, making them vulnerable to attack by hackers who would like to steal, destroy, or hold hostage sensitive data for personal gain. Though the security strategy is not perfect, Zero Trust reduces the attack surface and limits the impact and severity of the attack.
Functionalities in an application increase its vulnerability to an attack and the frequency of the attacks also increases. Identifying vulnerabilities and security threats early on can save a lot of time and money for businesses. App security lowers the number of vulnerabilities, increases efficiency, and improves the speed of detection and time-to-fix.
Watch now: How InfinCE – an infinite cloud platform, is empowering industries with secured next-gen cloud technology!
7 Reasons Why Businesses Need Zero Trust Security
Zero Trust limits the scope of damage if credentials are compromised, or if the firewall is breached. This paradigm secures remote work better than conventional methods. It improves productivity and organizational agility. Here are additional reasons to consider:
1. Increased Cyberattacks
When organizations rely on a single sign-on (SS)) verification method, ensuring people are who they say are may become difficult and risky. To avoid this security gap, SSO should be balanced with other technologies like Multi-factor Authentication (MFA).
In the last few years, MFA has become easier and smarter. While SSO and MFA together create a tight web of security around an organization, they fail to provide a smooth end-user experience.
That is where Zero Trust Security comes in. Zero Trust is based on the assumption that “nothing” and “nobody” are to be trusted. Using AI and ML in Zero Trust models, organizations can start to learn the normal behavior of their employees. These enable organizations to detect any deviation from their regular pattern and block an employee’s access until he is being verified.
2. Cybersecurity Workforce Outpace Supply
The success of Zero Trust depends on continual monitoring and analytics. When you use automation to evaluate access requests you can judge those requests based on the key identifiers and then automatically grant access. The IT department need not be involved in approving each access request, but look into it only when the automated system flags requests as suspicious.
How can this be of significant benefit? According to Cybersecurity Workforce Study, 2021, 60% of the participants reported that the shortage of cybersecurity staffing is placing their organization at risk. Despite the influx of 70,000 professionals into the cybersecurity workforce, global demand for cybersecurity professionals continues to outpace supply. So, if you can safely automate, you can reduce human resources, and your existing team can devote their time to innovation and improvement.
3. Heightened Security Measure Require More Security Teams
The Zero Trust optimizes your existing security team because it uses a centralized monitoring system. With it, your team can easily generate reliable data and gain insights. As a result, you can maintain a more secure environment even with reduced security staff.
4. Cloud Environment Require Shared Cybersecurity Responsibility
Businesses are moving their critical applications and workloads to the public or hybrid cloud. Given that, cybersecurity leaders must reconsider the security measures they have in place. The cloud environment requires a shared responsibility model. In the Zero Trust model, certain security aspects are provided by the cloud vendor, and others are cared for by the enterprise.
Read more: Why Is Cloud Security Important What Are The Best Practices to Ensure Cloud Security

5. Network Is No Longer a Secured Enterprise Network
Work From Home has necessitated intense use of the cloud. This means the internet network is no more secure. The conventional security measures and visibility solutions are no longer practical or robust enough. Zero Trust rests on the foundation of the “always-verify” principle. It offers complete visibility both in data centers and the cloud.
6. Everyone Need Not Have Elevated Security Privileges
In this digital-first age, users who access an enterprises’ applications and infrastructure are not just employees or customers. Vendors who are servicing a system, suppliers, or partners could also be accessing privileged data.
None of these non-employees need such access. What more, not all employees need access to every application, infrastructure, or business data. A well-executed Zero Trust strategy enables businesses to precisely control access based on key dimensions of trust.
7. Work From Home Increases Security Risks
In the post-pandemic era, Work From Home (WFH) has become the new normal. Location-based security technologies like the company’s headquarters are no longer relevant. Unsecured wi-fi networks and devices increase security risks. Assuming that their employee’s WFH setups and environments are not as secure as the office, businesses must depend on the overreaching system like a Zero Trust framework.
Work devices are traditionally managed, patched, and kept up-to-date with security tools and policies, not so with BYOD (Bring Your Own Devices). Some employees may forget basic cyber hygiene skills. The Zero Trust Security can control the potential for a security breach as it enforces access controls at every point within the network.
Watch now: Shifting to a remote work environment? Learn why InfinCE makes the best remote work companion!
Adopt Zero Trust Security
Zero Trust Security paradigm ensures each request undergoes evaluation based on micro-segmentation of user types, location, and other identifying parameters. Only after such intense scrutiny does it determine when to trust, what to grant access to, and how long that access should be enabled.
Zero Trust Security returns immediate gains through risk reduction and security control. But there is more. It improves visibility, increases productivity, makes better use of your IT resources, and facilities compliance. In a nutshell, Zero Trust Security helps your organization build strength and resilience.
Decision-makers and security leaders of an enterprise should consider leveraging robust layers of defense through the Zero Trust model. Zero Trust Security tightens controls over access to information through network perimeters and the implementation of strict authentication measures.
Security experts at Fingent are working with the Zero Trust model and have honed their skills in providing bulletproof security for our clients’ systems and networks. Give us a call and see how we can help you.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
The cloud approach is gaining immense popularity amongst businesses due to its scalability, enhanced productivity, and cost-effectiveness. According to Cisco, in 2021, over 94% of workload and computing processes will be hosted on the cloud. While many firms are already implementing and thriving with the Cloud, a few still remain to deploy this technology. This blog is a simple guide to help you understand every aspect of the Cloud, and how your business can drive success with Cloud Application Development!
What’s Ahead?
- Knowing the Cloud!
- What is a ‘Cloud-based Application’?
- Benefits of a Cloud App
- Types of Cloud Application
- Key Features to Consider When Developing a Cloud Application
- Some Examples Of Cloud Application
- Developing a Cloud Application
- A Look at the Tools to Build Cloud-based Apps
- Challenges of Cloud-based Application Development
- A Few Common FAQs
- Conclusion
Knowing the Cloud!
In simple terms, the cloud refers to software or service that is accessed over the internet. The cloud uses data centers to store data, which enables easy access of files and applications from anywhere and from any device.
For businesses, leveraging cloud technology can immensely reduce IT costs and overhead, eliminating frequent updates and maintenance of servers. Cloud computing can also simplify international operations for companies by allowing seamless access and control of files and data from anywhere. Google Drive, Dropbox, Apple iCloud, and Microsoft OneDrive are some widely used cloud services today.
Read more: Why It’s Time to Embrace Cloud and Mobility Trends To Recession-Proof Your Business?
What is a ‘Cloud-based Application’?
In the last decade, cloud computing has experienced a tremendous investment. By the end of 2023, the global cloud market is estimated to reach over $ 623 billion.
Typically, a cloud-based app is an Internet-run program having its components stored online with some or all of its processes carried out in the cloud. These on-demand services allow you to access computer networks, storage, or resources using the internet.
Cloud-based solutions help businesses augment capacity, scalability, and functionality while at the same time reduce maintenance and cost for computer infrastructure or in-house teams.
Common solutions provided by cloud-based applications may include;
- File storage and sharing
- Order entry,
- Inventory management
- Word processing
- Customer relationship management (CRM)
- Data collection
- Financial accounting features
Benefits of a Cloud App
The cloud is creating a huge impact on businesses. According to Gartner, over 60% of companies will majorly rely on the cloud for their operations by 2022. Of course, this means that the cloud has some huge benefits to offer for businesses. Here are a few to highlight.
1. Improved data sharing and security
The data stored in the cloud is easily and instantly available to authorized users. Since the cloud offers easy availability of data, security and privacy are often a concern. That is why the advancements in cloud technology have majorly focused on providing enhanced data security. Many cloud providers now guarantee improved data security, making the cloud the best source for secure storage. Also in case of disaster recovery is inevitable, the cloud provides a streamlined solution to restore and back up data.
2. Improved collaboration
Cloud-based apps and software enable organizations to make collaboration an easy and effective process. These applications provide easy data sharing and editing options allowing employees to work effectively on projects remotely and in real-time. Role-based access control enables better monitoring of tasks, and improves team management, especially when operating remotely. Improved collaborations can help enterprises to reduce time-to-market and enhance customer service. InfinCE is a prime example of how enterprises can use a cloud-based app to improve team collaboration. The app provides centralized management, enhanced visibility, and easy communication that drives operational efficiency and productivity.
3. Cost-effective
The cloud space can be scaled up or down depending on your business needs. Cloud service providers allow you to pay per usage of the cloud infrastructure allowing you to only pay for the services you need. Most cloud providers offer seamless concierge support and regular maintenance, which in turn immensely helps reduce the stress and cost of maintenance. Moreover, there is no need to invest separately on devices to store data, as the cloud ensures safe and secured data storage. Put simply, cloud-based apps help enterprises reduce the upfront cost of the IT infrastructure and hence are a cost-effective solution.
Types of Cloud Application
To proceed with cloud application development, you will have to decide what type of app you would want to create. One way to classify the categories is about the differences in the app architecture.
SaaS – Software as a Service
SaaS serves both cloud apps as well as individuals. These apps run on third-party hardware and not on the user’s device. Also, the software is hosted remotely. A big advantage of SaaS is that you don’t have to spend on additional hardware or buy licenses for every software update.
IaaS – Infrastructure as a Service
This type of product often requires middleware and app support from the clients. The customer may have to create a custom programming bridge between the application and its operating system. However, with IaaS, one can develop a customized product without building the basic components from scratch.
PaaS – Platform as a Service
This cloud-based app development requires the application code from the customer. PaaS providers allow their customers to use their hardware and basic development software. As this software is updated constantly, developers can use only its latest version. PaaS is flexible and lets the users scale the product as per their needs. Cost efficiency and flexibility are some of the major benefits of PaaS.
Read more: Cloud Migration Strategy: 7 Steps to Accomplish a Flawless Transition
Key Features to Consider When Developing a Cloud Application
The Cloud is a powerful technology, which if leveraged the right way can do wonders for your company. That is why it is imperative to be clear and sure of what benefits you need exactly to derive out of the cloud application development. Here are a few things to consider when fixing the features of your cloud application.
One of the most eminent features of the cloud is that it provides ample space for flexibility and scalability. With the cloud, one can empower safe storage of data that can be expanded as per convenience.
Most users prefer the cloud because of its storage facilities. However, its security is always a concern. When investing in cloud application development, one must highly prioritize app and data security by ensuring a code-based architecture for improved security.
Although the cloud delivers unlimited benefits, cloud hosting comes with a cost. Thus, data size optimization and condensed user requests should be the top priorities while developing a cloud platform.
To ensure you attain maximum benefits from these and the many other features of the cloud, it is imperative that you partner with developers who are highly aware and experienced with the diverse cloud platforms so that you attain software that perfectly suits your business needs. Moreover, following an agile method of development would allow you to collaborate better with your developers, programmers, designers, data architects, and QA managers for improved development efficiency. At Fingent, we ensure client participation at every stage of app development.
Some Examples of Cloud Application
Most of the apps we use today, utilize the cloud in one way or another. Cloud application development has given birth to some amazing tools and services that make operating businesses a little less stressful. Here are a few to point out!
- InfinCE: Provides streamlined and simplified IT Infrastructure, centralized management, enhanced work collaboration, access to unlimited productivity tools, all under a single platform.
- Dropbox or Google Drive: This allows you to store your files on the cloud easily and help others access them from anywhere.
- Figma: This powerful cloud-based design app is gaining popularity due to its collaborative nature.
- Miro: This provides a virtual board that enables you to work with other users in creative and fun ways.
The possibility to collaborate with users from all over the world, even in real-time is one of the biggest advantages of cloud apps.
Read more: InfinCE – Untangling Technology for Businesses
Developing a Cloud Application
Cloud application development involves different stages, each of which matters to enable your app to hit the market. Most cloud application development teams use DevOps practices and tools such as Kubernetes to ensure an effective and successful project.
At Fingent, we analyze your business needs and custom-build apps that solve your business complexities. We can help you seamlessly transit to the cloud and efficiently deploy its benefits to achieve greater business growth and value.
A Look at the Tools to Build Cloud-based Apps
A wrong tech approach can slow down your business development, so the technological stack is of utmost importance when developing cloud-based apps. You can choose a cloud service vendor from market leaders such as;
- Amazon Web Services(AWS) – In 2019, it obtained a 32% market share and became the leading provider. AWS includes over 140 flexible and integrative services. This allows you to build almost any custom app.
- Google Cloud Platform – As a PaaS, it offers you cloud computing, API services, advanced analytics, storage, NoSQL database service, and even virtual machines. It is flexible, affordable and a great platform for start-ups.
- Microsoft Azure- Its solutions are designed for enterprises looking for scaling or having many web products. Its services may include ML modules, mobile back-end, database services, and virtual machines.
Cloud-based app structure
- Another aspect to consider when cloud application development is the data architecture. A cloud app operates as a collection of interconnected services or APIs. So, to get maximum benefits of cloud services, you will have to connect them and at the same time understand the kind of components you have while ensuring that those services are integrated.
- Next, you must consider data organization. Remember, the app architecture must instruct the cloud services about how to decouple the data. This will help you store the app components either on a public or private cloud. As a result, your business will become flexible and enable you to make your web performance better.
- You must develop a communication logic between the data and services of your app. The app components should communicate instantly. If the logic is not well-designed, the customer experience could be poor due to slow loading speed. So, optimize the communication and apply either single-channel streaming or system message grouping.
- Scaling is something you must think of in advance. Create a margin of safety for your operational channels and consider future traffic extensions. Make sure to build an operational model to help back-end components and storage server customers especially in extreme situations.
- The last issue to think about is the security algorithm. Banking, retail, or healthcare have their dedicated standards so make sure your tools meet their expectations. Make sure to check the security algorithms for any vulnerabilities of your cloud-based solutions and the encryption is strong. Also, implement a cloud identity and access management (IAM) approach, to ensure your product is secure and cost-effective.
Read more: 7 Reasons For Enterprises To Implement Multi-Cloud Strategy In 2020
Challenges of Cloud-based Application Development
When you decide to opt for a cloud-based software solution you should figure whether your company can be a cloud provider (SaaS, IaaS, or PaaS) or build an app based on third-party cloud solutions.
If you decide to be the cloud provider, you will have to think of issues such as the data processing logic, hardware, and service security as you will have to host your service and provide the users with a cloud network. If you decide to develop your app on a third-party cloud, you will have to consider the integration and so you will have to choose your provider carefully.
Here are a few challenges that you may come across during cloud application development.
- Reliability: Your cloud software design includes critical operations that need to work if you want your customers to benefit from the solution. Avoid using a cloud framework that cannot maintain important processes. You can consider backup data and operations with a private cloud.
- Scalability: You must ensure to provide a scalable solution with the service you have chosen. If a product can’t be scaled or it falls over due to sudden traffic surges or you are unable to deliver services to a large audience regularly, you are bound to lose potential profits to your business.
- Performance: More data centers mean the better your app will perform. Global providers place their servers in such a way that users can experience the same page loading speed from any location. If the number of servers is less or the custom UI needs more than three seconds to load, the app customer experience is likely to be poor. More loading time means less conversion. The app loading speed is defined by a Content Distribution Network(CDN) which is a part of the cloud app infrastructure.
- Interoperability: The cloud environment should be able to run your app on different devices and integrate other cloud services into your infrastructure. However, as all cloud systems do not communicate with each other, you may not have a chance to mix components from different services.
- Security: Security especially client-side along with storage protection will remain challenging for developers. Security is the biggest challenge when it comes to adopting cloud computing. Cloud apps may include API integrations. These apps also must be easily accessible for users. To raise the security level of your cloud-based app, you will have to leverage strong data encryption, SSL, and reverse proxy.
A Few Common FAQs
1. What are cloud-based technologies?
These technologies are applications, services, or resources that are made available to users on-demand via the internet from cloud computing providers’ servers.
2. How do cloud applications work?
To process logic, a cloud-based app relies on remote servers. This is accessed through a web browser using the internet.
3. What are the different types of cloud computing?
There are three types of cloud computing; public cloud, private cloud, and hybrid cloud.
4. What are the different types of cloud services?
Cloud services are of four types – serverless, infrastructure as a service (IaaS), platform as a service (PaaS), and software as a service (SaaS).
5. What is the difference between a web application and a cloud application?
A web-based application requires some or all the software to be downloaded from the web every time it is run. On the other hand, a cloud-based application function within the cloud and is similar to a web-based application as well as a native desktop application.
Conclusion
From cost reduction and scaling opportunities to higher accessibility of the final product. Cloud application development offers a host of benefits to businesses. However, cloud application development has its own set of complexities if not carried out the right way. A custom software development partner plus a trusted cloud service provider like Fingent can help you seamlessly transit to the cloud with 24/7 concierge support and consultation. Get in touch with us today to discuss your project!
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
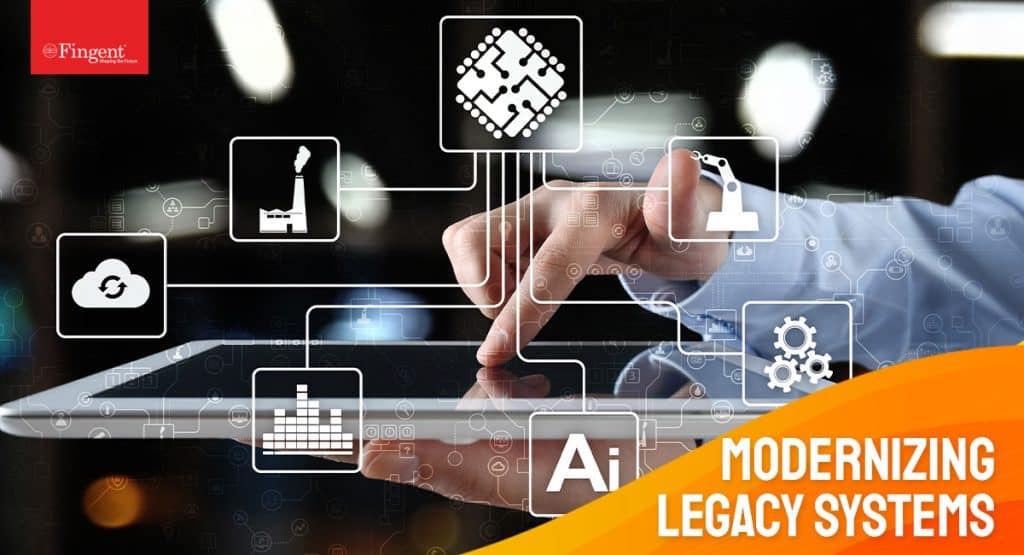
How does legacy cloud migration ensure business continuity in FinTech? Explore in this article.
Did everyone have Business Continuity Plans in place and protocols to follow during the pandemic? Yes, definitely. Did anyone expect a disaster of magnitude like this? Not in their wildest dreams or gloomiest forecasts! The pandemic forced hundreds of millions of employees to shelter in place, essentially moving all operations online. Not all organizations were equipped with the needed technological tools, and most businesses were caught off-guard. FinTech companies were not immune to the aftermath.
For example, pre-COVID-19, it is true that a few FinTech organizations began migrating to Cloud. But, conversely, there were many who hesitated to embrace the cloud migration strategy because of legitimate concerns over critical factors such as rising costs, managing complex business data and workloads, re-training existing IT staff, and more.
The pandemic was a wake-up call that helped businesses identify legacy cloud migration as a relevant and vital choice. Though most companies have realized that modernizing old, outdated business applications can boost productivity and increase efficiency; some are still hesitant about their cloud migration strategy.
Read more: 11 Practices Followed by Leaders to Build Resilience and Ensure Rapid Business Recovery
This blog explains why FinTech organizations must consider legacy cloud migration seriously and what are some specific benefits of cloud migration strategy.
What is legacy cloud migration?
Legacy cloud migration involves moving on-premise applications, outdated software, or programs that a company has relied upon for years. These applications may include everything from sales or CRM applications to industry-specific applications. Some FinTech organizations may be reluctant to migrate to cloud just because legacy cloud migration is a daunting project. However, maintaining a status quo can be detrimental to your business growth.
Read more: Why modernize your legacy systems? What’s the best approach to legacy systems modernization?
Legacy cloud migration is the only light at the end of the tunnel
The pandemic has triggered a significant reexamination of FinTech businesses and their IT priorities. Gartner predicts that “by 2022 cloud shift across key enterprises IT markets will increase to 28%.” This era of economic uncertainty caused by the pandemic affected all businesses, especially, FinTech organizations. A report from Yellowbrick showed that 84.3% say cloud computing is more important than workplace disruption.
Thankfully, cloud migration strategy was available when it was most needed – a phase when maintaining business continuity has become a priority. Consider the most important reasons for legacy cloud migration.
Why FinTech Companies Should Embrace Legacy Cloud Migration
1. People matter more than premises
As the pandemic hit the world with one wave after another with no time to catch a breath, there was a dire need for remote self-service technology. The massive role played by people working from home is a clear indication that people matter more than premises. A year ago, cloud migration strategy was considered discretionary. Today, work from home has made cloud migration mandatory.
Read more: Why It’s Time to Embrace Cloud and Mobility Trends To Recession-Proof Your Business?
Hence, now is the time for FinTech organizations to plan for their business continuity to remain adept for future upheavals, disruptions, or even disasters. When your organization migrates to cloud, you ensure your teams’ effectiveness while working remotely.
2. Prepare for the next
Though the pandemic is wreaking havoc, it will recede in due time. However, what remains is a possibility of a similar recurrence of disruption in the future. Hence, FinTech organizations must prepare for future disruption by recognizing that the calamity to come may not be another pandemic but its functional equivalent. Legacy cloud migration will equip you to face any future disruptions and remain resilient.
3. Facilitate real-time payments
Banks are well aware of the advantages of real-time payments. The race is on for upgrades and integrations that allow organizations to leverage real-time payments. A survey of over 500 executives indicated that 71.9% are ‘extremely interested’ in such payment capabilities. Above all, cloud brings in scalability and agility to real-time payments. Cloud migration strategy can improve the speed and consistency of transactions. Besides, it can enable fast and frictionless transactions.
Legacy cloud migration allows banks to adopt digital payments. Banks can address many of their traditional payment pain points, such as spikes in demand.
Collaborating between payment players and cloud service providers can help your organization provide a more secure digital experience for your customers. This is of paramount importance in a world where contactless interaction is the key. According to a McKinsey survey, banks that adopt digital transformation were able to increase customer satisfaction by 15-20%, reduce cost by 20-40%, and boost conversion rates and growth by 20%.
While consumer expectations and payment preferences continue to evolve rapidly, cloud migration strategy will help FinTech industries to stay relevant and continue to grow.
Read more: Safeguarding IT Infrastructure From Cyber Attacks – Best Practices
4. Scalability and flexibility for an uncertain future
FinTech firms need an infrastructure that can grow with them and protect their business from future disruptions. Migrating to a cloud platform equips FinTech firms to adapt to branch closures while extending banking services to as many people as possible. Legacy cloud migration provides the agility to scale with speed while saving on on-premise infrastructure that is comparatively expensive to maintain and upgrade. Moreover, it can provide your organization the needed accessibility, flexibility, and scalability during economic downturns.
5. Manage risks and compliance
Efficiency, automation, and cloud-based delivery will be critical for compliance operations. It is vital to use next-generation technology and emerging digital approaches to optimize risk modeling. Since legacy cloud migration is agile, flexible, and low cost, it can solve many challenges in operational risk and financial crime compliance activities. Additionally, solutions deployed in the cloud can assist with operational challenges.
6. Data management
Acquiring large quantities of accurate data is a top priority for all FinTech firms. Their success depends on all the information they must collect, from onboarding to analyzing their spending habits. Cloud migration strategy enables your firm to gather and store data securely while allowing your designated employees to access it from anywhere when required.
Read more: Cloud Migration Strategy: 7 Steps to Accomplish a Flawless Transition
The FinTech industry is at a crossroads now. How it responds to the current crisis will determine its future. The key to the survival of FinTech companies will be the rapid digitization of their business and the adoption of cloud migration strategy. Migrating to the cloud is as important as the historic move from typewriter to computer. Cloud migration has become a global force for business growth. It can reduce overhead costs and help your team focus on increasing productivity and performance.
Cloud migration strategy will become inevitable as the FinTech industry builds a more accessible financial world. By partnering with a cloud migration services provider like Fingent, you will be able to quickly and seamlessly migrate to the cloud without disrupting your business. We also help you build FinTech applications and platforms leveraging the latest technology in the market. So, give us a call, and let’s get talking.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
How can companies ensure cloud security amid cyber threats and malicious online activities?
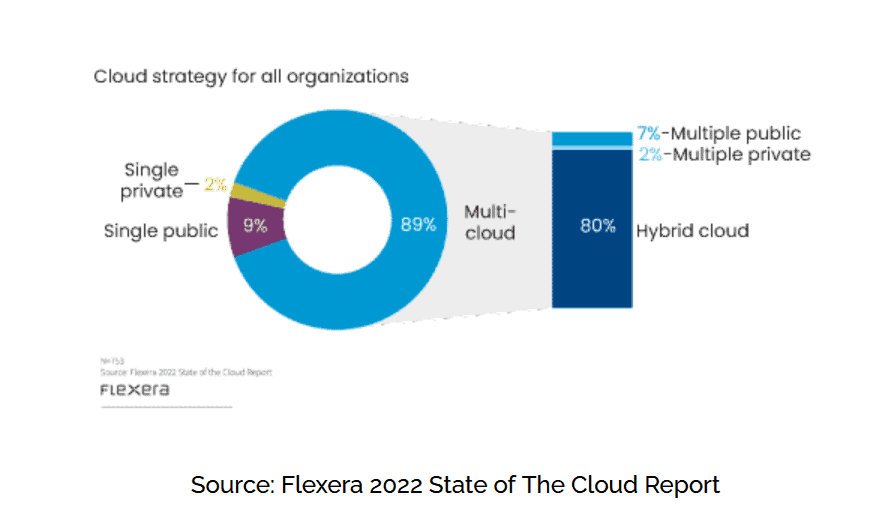
The explosion of the cloud has changed the face of the business process as we know it. Nearly 90% of companies rely on the cloud. And yet, there has been some skepticism around cloud security. With recent breaches and technological attacks, maintaining cloud security has become the foremost concern for businesses worldwide.
Security experts at Fingent understand your concern, and so we have put together this blog about the importance of cloud security and the best practices which will ensure that you are secure on the cloud.
Why is cloud security important?
According to a report by Cisco, cloud data centers process 94% of all workloads. Despite the popularity attained by cloud technology, most of these companies are skeptical about cloud security. There is a reason for this. Statista reports the number of data breaches in the U.S alone increased to 156 million in 2020. It has also been reported that hackers attack every 39 seconds. This can be fatal to businesses in the following ways:
1. Managing remote work
Remote work lets you hire talent from across the globe. However, this arrangement entails inherent security risks. Using personal devices may expose your data to malware and phishing attacks. If a malicious virus enters through them into your cloud system, the damage done could cut your company off at its knees.
Read more: Why It’s Time to Embrace Cloud and Mobility Trends To Recession-Proof Your Business?
2. Security breaches
If your company chooses to run your application on a public or hybrid cloud, you are entrusting a third-party to take care of your data. This means you no longer have any control over data security. So it is critical to stay on top of things and ensure that your cloud computing provider is serious about this responsibility. Even when you know your provider will ensure top-tier security, it is your responsibility to verify that your data is secure as a client.
3. Comply with regulations
Data protection standards were put together to ensure the integrity and security of customer data. When you store your customer data on the cloud, it is your responsibility to keep it secure, especially if your organization belongs to a highly regulated industry like finance, insurance, banking, or legal. A data breach will destroy your reputation and brand because external parties will hold you accountable.
4. Build access levels
Unintentional leaks of data will compromise your business integrity and give your competition a leg up. Limiting data access only to those employees who need it can prevent errors that lead to data leaks.
5. Disaster recovery
Disasters such as flooding or fire can strike without warning. Unless your data is secured and protected, you could lose all your data. This may undermine customers’ confidence in your organization, delivering a death blow to your otherwise successful business.
Read more: How Secure is Your Business in a Multi-Cloud Environment
Best practices to ensure cloud security
- Carefully choose a trusted provider
- Review your cloud security contracts and SLAs
- Understand your partnership of shared responsibility
- Control employee access
- Secure user endpoints
- Maintain visibility of your cloud services
- Implement a strong password security policy
- Highest levels of encryption
“Cloud computing is a challenge to security, but one that can be overcome” – Whitfield Diffie, an American cryptographer.
True to Whitfield Diffie’s words, cloud security measures can be taken to encrypt the system that will help achieve adequate cloud security.
1. Carefully choose a trusted provider
Partnering with a trusted provider is the foundation for cloud security. Choose a partner who delivers the best in-built security protocols and follows industry best practices’ highest levels. You need to ensure that you confirm their security compliance and certifications.
Learn more: Take a look at how InfinCE, an infinite cloud platform, ensures secured work-collaboration within an organization and helps enhance company efficiency & growth!
2. Review your cloud security contracts and SLAs
In an event, SLAs and contracts are the only guarantees of service and course of assistance. 62.7% of cloud providers do not specify that customer data is owned by the customer, creating a legal grey area. Read through the terms and conditions, annexes, and appendices to ensure who owns the data and what happens if you terminate the services. Also, seek clarity on visibility into any security events and responses.
3. Understand your partnership of shared responsibility
When you tie-up with a cloud service provider, you enter into a partnership of shared responsibility for security implementation. Understanding the shared responsibility involves discovering which security tasks you will handle and which your provider will handle. It is important to ensure transparency and clarity in your partnership of shared responsibility.
4. Control employee access
Implementing strict control of user access through policies will help you manage employees who attempt to access your Cloud services. Cloud security best practice starts from a place of zero trust. Afford user access to data and systems only to those who require it. To avoid confusion and complexity, create well-defined groups with assigned roles. This will allow you to add users directly to the group rather than customizing access for each employee.
5. Secure user endpoints
Since most of your users access your cloud services through web browsers, it is crucial to introduce advanced client-side security to keep it protected from exploits. Implementing endpoint security solutions that include firewalls, antivirus, intrusion detection tools, and more will help to protect your end-user devices.
6. Maintain visibility of your cloud services
Remember, you cannot secure something that you cannot see. Using multiple cloud services across various providers and geographies can create blind spots in your cloud environment. Make sure you implement a cloud security solution that provides visibility of your entire ecosystem. You can then implement granular security policies to mitigate a wide range of security risks.
7. Implement a strong password security policy
Strong password security may sound basic, but it is an important element in preventing unauthorized access. Have a strong and strict password policy. To defend against most brute force attacks, enforce a rule that users update their password every three months. You may also implement multi-factor authentication. This would require a user to add two or more pieces of evidence to authenticate his/her identity allowing you to trust your users while ensuring that they are authorized users.
8. Highest levels of encryption
Your data may get exposed to increased risk while sending it back and forth between your network and the cloud service. You must consider using your own encryption solutions for data, both in transit and at rest. Encryption keys will help you maintain complete control over your data.
Read more: 6 Proven Ways for Businesses to Combat Cloud Security Risks
Don’t wait till it’s too late!
You never know when a stealthy hacker could attack your business and make you go under. All organizations, independent of their size, can benefit from these best practices and improve their cloud usage security.
At Fingent, our custom software development experts go above and beyond to ensure that your business is hacker-proof and secure. If you need to discuss cloud security options, do not put it on the back burner! It could creep up on you and set your whole business afire, ruining your competitive edge and spelling doom for the future. Call our experts and discuss your options today.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
Cloud security threats: How to protect your data and mitigate risks?
Be it Google G-Suite, Dropbox, Adobe, Salesforce, or Microsoft Office 365, almost every business uses cloud services for their critical business requirements. Despite its rapid growth, cloud computing brings the possibility of severe security threats that can drastically affect an organization. According to Cybersecurity Ventures, cybercrime damages might hit $6 trillion by 2021. 1 out of 4 will experience a data breach, and on average, businesses are investing about $7.2 million on security breaches. These figures prove how devastating security threats can be if they are left unchecked.
While cloud systems, applications, and networks are not located within your control physically, the security responsibility and risk mitigation are definitely within your control.
Some of the latest security threats to cloud data management include:
- Phishing attacks
- Ransomware attacks
- Insider threats
- Asynchronous procedure calls
- Distributed Denial of Service Attacks (DDoS)
- Uneven security gaps
Why is cloud security important?
While cloud service providers protect your data, they can’t protect your data when it leaves the cloud to interact with other systems.
Cloud security is essential to protect your data as well as the integrity of your business. According to a survey, 60% of breaches occur at patches that are available but not applied. You will need a team to continually monitor potential security threats to ensure that your cloud infrastructure is always up-to-date.
Regardless of your organization’s size, it would be best to implement strong network security services to protect your organizational and customer data.
Read more: Why It’s Time to Embrace Cloud and Mobility Trends To Recession-Proof Your Business?
Six ways to protect your data and monitor your cloud environment
1. Set-up multi-factor authentication (MFA)
Stolen credentials make it easy for hackers to access your business data and applications is to steal your credentials. The combination of complex usernames and passwords alone is not sufficient to secure your user accounts from hackers.
So, protect your cloud users with two-factor authentication or multi-factor authentication to ensure only authorized people can access your cloud apps and have access to sensitive information.
Deploying multi-factor authentication is an effective way to keep potential hackers from accessing your cloud applications. Most security experts believe that it is mandatory to implement MFA as it is also one of the cheapest security controls an organization can have.
2. Assign access controls
Not all your employees need to have access to every file, application, or data. By setting up proper authorization levels, each employee can only view or access applications or data required to complete their job.
Assigning access controls will ensure that your employees don’t edit any information accidentally that they are not authorized to access. Additionally, it will also protect you from hackers who have hacked an employee’s credentials.
3. Leverage automation to monitor, log and analyze user activities
Real-time monitoring and user activity analysis can help you identify any irregularities or abnormal moves that are not part of your regular usage patterns. For example, log in from an unknown IP or device.
Such irregularities could indicate a breach in your system, so it is essential to identify them early on to prevent hackers from hacking your system and help you resolve any security issues before they wreak havoc with your security system.
You can leverage data protection solutions to automate the process and support 24/7 monitoring and management.
Note: Every business has different needs for different levels of security services, so you may consider getting a third-party risk assessment before making significant investments. At Fingent top custom software development company, we identify and evaluate any loopholes in your current infrastructure and provide you with apt cloud infrastructure solutions using our unique approach.
Read more: Cloud Service Models Saas, IaaS, Paas – Choose the Right One for Your Business
4. Provide anti-phishing training to your employees
Small Business Trends reports that 1 in every 99 emails is a phishing attack, which amounts to 4.8 emails per employee in a five-day workweek.
Hackers can easily steal employees’ login credentials to gain access to secure information via phishing. In this kind of social engineering attack, the attacker sends fraudulent emails, texts, or websites to trick the victim into sharing access to sensitive information. Providing ongoing training to your employees to recognize a phishing attempt is the best way to prevent employees from falling prey to such scams.
5. Create a comprehensive off-boarding process for departing employees
Ensure that your departing employees no longer have access to your cloud storage, data, systems, customer data, and intellectual properties.
As every employee is likely to have access to different cloud applications and platforms, you need to set up a process that will ensure all the access rights for departing employees are revoked. If you can’t manage this internally, you may consider outsourcing this task to a credible vendor.
Learn more: Take a look at how InfinCE, an infinite cloud platform, ensures secured work-collaboration within an organization, and helps enhance company efficiency & growth!
6. Cloud-to-cloud backup solutions
There is no doubt that there are legitimate risks associated with any cloud application or platform. However, the odds of you losing data due to your cloud provider’s error is low compared to human error.
Say, an employee deletes your data accidentally, and a hacker obtains the account password and corrupts the information, or an employee clears her inbox and folders. In such cases, cloud providers can do nothing much past a specific period. Most cloud providers store deleted data only for a short time.
You can check with your cloud provider about the time frame and whether they charge any fees to restore the data. If your company must abide by strict regulations or be concerned about being liable for corrupted data, you can consider cloud-to-cloud back-up solutions.
Read more: Cloud Migration Strategy: 7 Steps to Accomplish a Flawless Transition
What Next?
There’s no denying that cloud computing is one of the most cost-effective options to maintain a high level of security for your sensitive data. At Fingent, our experts can help design a comprehensive cloud computing strategy that will help achieve your business objectives and provide you with ongoing management to keep your data protected. Contact us now and get started.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
Cloud computing refers to the method of computing in which an interconnected network of remote servers is utilized for the execution of the operations such as storage, management, and processing of information. The business units in the current era are making use of multiple cloud computing services and techniques in an integrated architecture. There are various deployment and delivery models of the cloud which are amalgamated as one unit for the execution of business processes and activities. However, with the expansion of such practices, there are some security issues that have been observed.
The security issues and occurrences are primarily associated with network-based security risks, availability, confidentiality threats and integrity risks. Events such as Denial of Service (DoS) attacks, malware attacks, message/media alteration attacks, spoofing and phishing attacks, man-in-the-middle attacks, and eavesdropping attacks are common in the multi-cloud environment.
Organizations are required to follow certain steps towards security to make sure that the security risks and occurrences are prevented, detected and controlled. The following security measures and steps shall be included in for achieving a secure multi-cloud environment.
- Prioritization of Visibility: The business organizations in the multi-cloud environment must ensure that they have complete visibility across all the cloud instances. Behavior-based monitoring shall be adopted for enhancing the visibility. Objectionable modifications and malevolent activities will also be highlighted with this process.
- Adherence to the Best Practices: In the case of the multi-cloud environment, there are various systems, devices, and networks that are involved. Each of these entities has a set of guiding principles and standards. The cloud security team must analyze and understand the best practices that are associated with each entity. For instance, in case of NoSQL databases present in the multi-cloud environment, it would be best to meet the compliance requirements, install advanced access control and authentication measures and promote database security for the overall security of the cloud.
- Flexible and Secure Governance: Governance is a critical element in any of the organizations. It is possible to establish trust and security across the organization only with the aid of well-governed systems. In association with the multi-cloud environment, the processes such as identity management, scheduling activities and resource allocation must be securely governed.
- Encryption of the Data at Rest: It is often witnessed that the business organizations enforce and implement the encryption of the information that is in-transit. However, the encryption of the information at rest is often not paid due attention. Such loopholes in security provide the attackers with an opportunity to get hold of the information at rest and misuse the same. It is, therefore, extremely necessary to encrypt the information at rest using advanced encryption algorithms.
- Advanced Shared Responsibility Model: Sharing of resources is one of the prime features of cloud computing, which gets enhanced in the multi-cloud environment. There are overlapping responsibilities and ideas that are often observed which may lead to the occurrences of loopholes in the security. Every entity that is present in a multi-cloud environment must make sure that complete justice is done to the shared responsibility model of the cloud. The allocation of roles and responsibilities shall be done in such a manner that there are complete transparency and ease of execution that is involved.
- Network-based Security Controls: Most of the security issues that occur in the multi-cloud environment have networks as the prime agents of the threats. It adds to the requirement of implementing automated and advanced network security tools and controls to ensure that such risks are avoided and controlled. Some of these tools include network monitoring tools, intrusion detection systems, intrusion prevention systems, anti-malware tools, and anti-denial tools.
Cloud strategy and planning has provided the organizations with the ability to enhance the performance, speed, and quality of their respective business operations and activities. With the occurrence of the security risks and threats, there is a poor impact on the business continuity and customer engagement. It is, therefore, required to include the basic and advanced steps to security to deal with the security issues and problems. These steps shall combine administrative, physical, logical and technical controls.
The use of security solutions that are available in the market will allow the organizations to achieve and maintain security in the multi-cloud environment. These solutions will provide an integrated security mechanism and will eliminate the need to deploy security measures for each of the cloud model and elements. Security concepts and requirements, such as information security, network security, and database security are now provided in a single package by the leading software solution providers while entrusting them for your digital transformations.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new