Tag: data security
Cyberattacks are hitting the headlines with increasing frequency. Data breaches and attacks are currently inevitable parts of running an organization. Cybercriminals are adept at using phishing, malware, or insider threats to infiltrate infrastructure and steal confidential information.
Businesses that compromise their cybersecurity face more than just the loss of confidential data. Cybersecurity breaches can affect a business’s market value, jeopardize the brand reputation and compromise competitiveness. The effects of a single cyber-attack can be permanent and devastating.
How do you combat this era of over-smart cyber criminals? You need more than cyber security. What you need is cyber resilience!
Are you wondering what the best way to protect your company from within and without is? Do you want to secure your business in this volatile economic atmosphere?
If YES is your answer, please continue reading to find out why shifting from cybersecurity to cyber resilience is necessary.
Why Has It Become Necessary to Shift from Cybersecurity to Cyber Resilience
Pandemics are not the only calamities from which a business needs to build resiliency. Any unforeseen event, be it a natural calamity, a shift in the economy, or anything else, needs to be part of comprehensive disaster recovery planning.
Such unforeseen events provide many risk-based opportunities to pivot in response to risk. Chief among these is digital transformation. Here are four risk-based opportunities that make it necessary to shift from cybersecurity to cyber resilience.
1. Strategic risks: Included among many others are business continuity, reputational hazard, competition, insurance legal risks, and more. If these risks are not mitigated in time, they can affect organizational sustainability.
2. Financial risks: Financial risks have implications for regulators, tax complexities, and employee outsourcing.
3. Operational risks: Operational risks include organizational and digital functions, from employee well-being to AI and robotics. It can affect the business process and all those involved.
4. Remote work: This can easily expose an organization to cyber threats.
If an organization becomes a target of persistent cyber threats, its networks will likely be compromised. That is why businesses must be ready.
Cyber resilience allows an organization to minimize the impact of persistent threats. It lowers the probability of a successful attack and minimizes the damage if the attack is successful.
Read more: A Detailed Whitepaper On – Is Cyber Resilience Over Taking Cybersecurity for Good?
How Are They Different From Each Other?
1. Cyber security-the mighty wall
Cyber security is about reacting to a cyber-attack while cyber resilience is about anticipating a possible attack.
Cyber security is about technologies and processes designed to shield computer systems, networks, and data from cyber threats.
For example, when an empire wants to prevent security breaches, it might first build a huge, robust wall. If it feels that is not sufficient, it may construct another wall that is higher than the existing wall and perhaps add a ditch.
Can such measures completely protect an empire from a breach? Well, history has a different story to tell.
Cyber security is somewhat like that wall. It is more focused on preventing hackers from breaching ITs’ security wall. While it may prevent the majority of attacks, a hacker can still find ways to breach that mighty wall when the landscape changes. Despite all measures, an organization may be still vulnerable to a cyber-attack.
Read more: Artificial Intelligence and Machine Learning: The Cyber Security Heroes of FinTech!
2. Cyber resilience-an ever-equipped and ever-prepared tech-ninja
The goal of cyber resilience is to anticipate, withstand, and adapt. It depends on the theory of “when there is a cyber-attack,” not “if there is a cyber-attack.”
A cyber resilient business is like a ninja, able to respond and recover from a cyber-attack. Such a business can continue to operate through the attack, and eventually, get back on track and become more capable of withstanding future disruptions.
It helps organizations to foresee hackers’ activities and be informed about the possible threats they pose. This way organizations are prepared to prevent and protect, defend and respond successfully to any attacks.
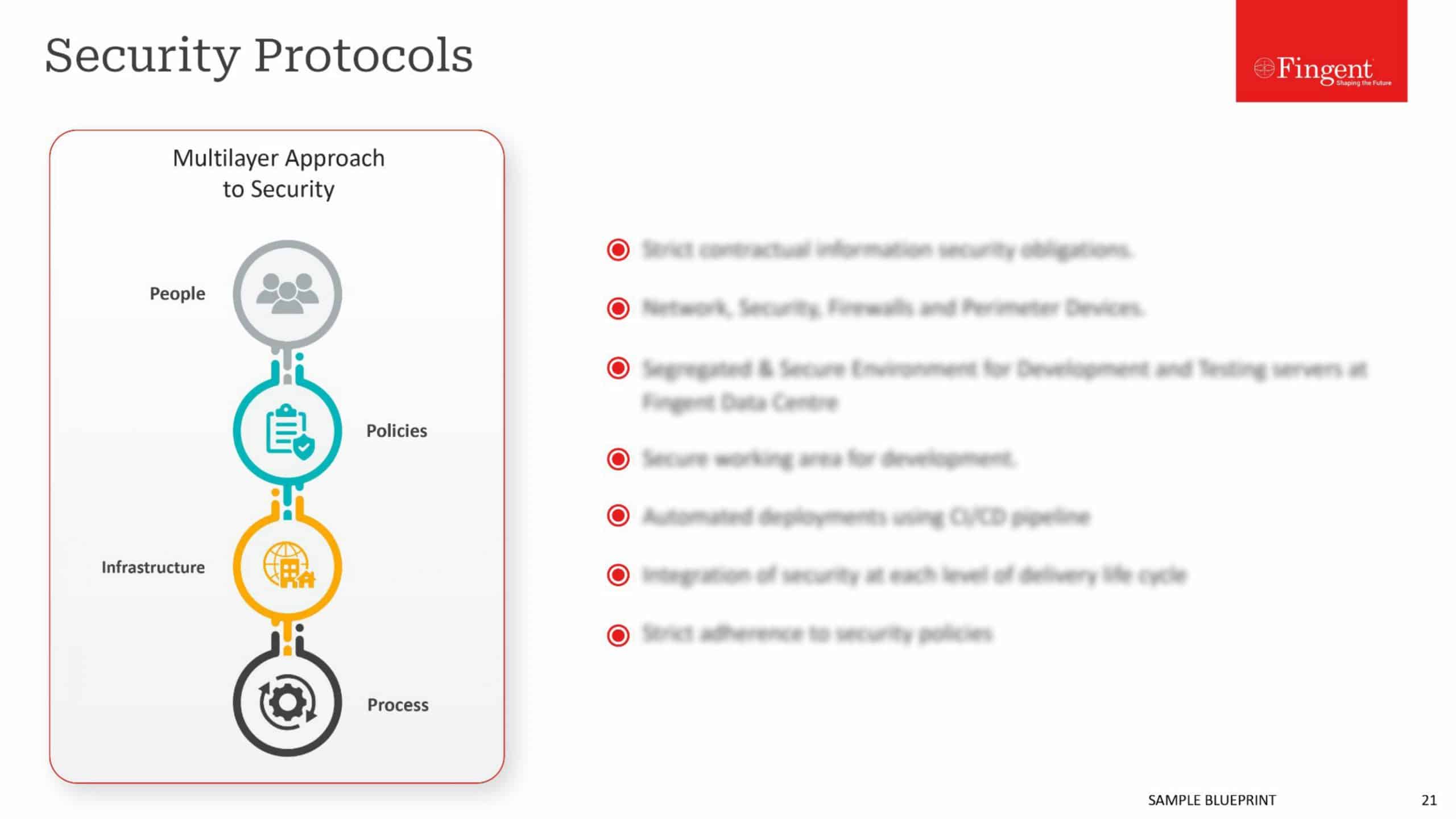
Cyber resilience is not just a security measure. It is a cultural shift – a full-time task that applies security best practices to defend an organization’s networks and systems. here are five key areas:
- Prepare: Preparation is key to success! Hence, to prevent cyber-attacks an organization requires a multi-layered approach. This includes technology, people, and processes. Cyber resilience involves having comprehensive security policies and providing training and in-work support to ensure that all involved know their role.
- Protect: In addition to basic security software, more sophisticated solutions like endpoint detection and response solution provide a greater degree of protection. Security awareness training and data protection layers offer even greater cyber resilience levels.
- Durability: Building durability into an organization is one of the end goals of cyber resilience. Adopting a single platform for data and content can make it easier to protect an organization as a breach can be identified quickly and quarantined before it affects other sections. All this while, employees can continue to access other systems and data.
- Recovery: Resilience means rising every time we fall. Cyber resilience means returning to normal no matter what. To avoid a complete halt to all business operations, an effective data backup and recovery is essential. Automated, granular backup and recovery of data to a separate network will enable businesses to quickly restore data that may have been seized or wiped.
- Adapt: According to a writer, adaptability is the simple secret of survival! And that is a key component of cyber resilience. Security solutions that leverage up-to-the-minute threat intelligence ensures that a network can adapt automatically to the latest threats. This sort of intelligence allows you to understand the current threats and make accurate predictions about likely attacks in the future.
Read more: Redefining Cyber Security Needs With AI!
ACT and not REACT
Data and infrastructural security are the topmost concern of every organization. Active and continuous protection is a must for tools and techniques. This is also why investing in cyber resilience can never go wrong in any condition.
Cyber resilience equips businesses with technical know-how in order to prepare for the worst and ensures it can deliver in the worst situations.
Cyber resilience involves a change of mindset. It is also about security operating within the organization and beyond. It is only by thinking of overall network resiliency that businesses can surmount existing threats, and overcome future threats.
Security experts at Fingent have their finger on the pulse of the digital world and know how to nip cyber threats in the bud and keep your business resilient from attacks. This means that you leave your cyber worries in our hands with the confidence that it will be dealt with effectively.
Call us and let’s discuss your security needs and how we can fulfill them.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
The “cloud” is a part of an evolution in IT services. IT services took the mainframe and turned it into the cloud. In the beginning, the on-premise IT department was the be-all and end-all. Over time, things have changed. There began a shift in service providers, service levels expectations, and experiences.
Businesses that leverage cloud capabilities uncover new possibilities and alternatives to fulfill the everchanging demands of their business. This is the time for businesses to think beyond cloud migration.
Most businesses see cloud adoption as the culmination of the journey. Instead, they must recognize that the cloud is a future-proofing continuum. A technology that provides flexible access to a collection of dynamic, ever-improving services.
The pandemic has hastened the cloud adoption pace so NOW is the opportunity to build on this momentum and continue transforming at this new pace. Why?
Why Do Businesses Need To Think Beyond Cloud Migration?
Soon, any app or infrastructure that is not based on the cloud will be considered a legacy. Cloud is no longer a mere technological approach for delivering applications. It will serve as a foundation for corporate innovation and a sustainable supply chain.
When organizations employ the cloud as a future operating model, they set up a technological base that will assist them today and into the future. The cloud continuum includes various forms of ownership and location. All these are dynamically enabled by next-generation connectivity like 5G.
Cloud continuum helps businesses visualize a path from on-premises to cloud migration. Businesses can apply the continuum concepts throughout their technology stack. This includes everything from infrastructure to network to apps, and beyond.
Read on to find out how cloud continuum strategy can help your business realize its full potential.
Read more: Cloud Security Best Practices | Why is cloud security important?
How Cloud Continuum Strategy Can Help Businesses Realize Their Potential
The cloud continuum is made up of several technologies. Setting clear priorities will support all elements of the business and this will help all in your organization to move together towards your business objectives.
- Achieve best possible results: The cloud continuum strategy enables companies to collect incremental feedback. Such feedback will help businesses adjust their aims to obtain the best possible results. This way they can constantly align their objectives.
- A catalyst to accelerate innovation: The cloud continuum is a readymade strategy. It helps organizations improve decision-making and capitalize on new possibilities to disrupt and distinguish through accelerated innovation. It is a new-age innovation accelerator essential for increased agility and future-ready business advantage.
- Elevate customer experience: Businesses can elevate customer experience to the next level with the cloud continuum.
- Enhanced skill and talent: The cloud continuum strategy will contribute to an efficient and effective work environment. It addresses gaps and continuously adapts to change as a continuum best practice.
- Manage scale awareness: The cloud continuum addresses the challenges an organization faces with regard to computing, performance, and latency limits.
- Improves ecosystem network effect: Improvement of network ecosystem depends on the number of ecosystem personnel and their engagement. The more value drivers you have, the better is quantity and quality of the participants.
Read more: Improve Business Planning with SAP Analytics Cloud!
Keys To Unlocking The Potential Of The Cloud Continuum
Holistic and human-centric cloud continuum strategy depends on speed and change. You need agile techniques that can capitalize on continuous enhancements. Here are four keys that will help you unlock the potential of the cloud continuum:
1. Have a clear vision of your goal
Your cloud continuum strategy must address:
Vision: Establish future goals for a resilient and sustainable business. Also, devise a strategy for technical debt reduction.
Competitive landscape: Every organization has weaknesses and vulnerabilities that a competition seeks to take advantage of. Hence, identify any gaps in the supply chain and competitive ecosystem.
Skills and talents continuum: To achieve your business goals in the future, you need to locate and retain relevant skills and expertise today. The foundation you build today will enable you to define your pathway and help you win the talent war.
2. Establish cloud practices
Be agile and adaptive: Make sure you combine technology adoption with strict discipline. This will allow you to modify your non-technology areas as computational advances. Doing so will help you steer ahead of your competition.
Incorporate mobility into the creation of new processes. This will allow for more flexibility in the future.
3. Deliver extraordinary experiences
Recognize that experience is at the heart of your business: Customer experience and employee experience can be a gamechanger for your business. Hence, ensure to make your investments available and accessible to both your employees and customers.
4. Stick to your cloud continuum strategy
Stay on your business journey by sticking to your strategy: You may face several challenges in helping various departments in your organization to understand and stick to your cloud continuum strategy. However, do not give up on your strategy. Educate and encourage everyone in your organization to comprehend and comply with the strategy.
Do you still feel unsure? Here are some use cases that will help you see how some major organizations were reinvented on the cloud continuum.
Read more: Cloud Migration Strategy: 7 Steps to Accomplish a Flawless Transition
How Organizations Are Being Reinvented On The Cloud Continuum
3M
During the pandemic, 3M plants struggled to gather, transfer, and use the data from their production systems. The organization then pushed the data from the plant’s on-premises SQL Server to Azure SQL Edge. This enabled a faster and more streamlined process. By the end of 2020, 3M was able to double its production of N95 masks.
Sephora
Sephora uses AI and AR to provide extraordinary experiences to all its customers.
Starbucks
Starbucks is well-positioned in the cloud continuum. It continues to innovate and grow despite socio-economic upheavals. It was able to stay ahead of its competition because it collects feedback and adapts its goals continuously.
It also ensures to provide a personalized experience for 100 million weekly customers by creating AI-driven recommendations.
Are You Ready For The Cloud Continuum?
The past year has been a witness to how fast an organization can pivot in the face of a crisis. Now is the golden opportunity to unlock your business potential with the cloud continuum. You too can stay ahead of your pack by becoming a continuum competitor. Partner with Fingent top custom software development company and see for yourself how your business will be transformed to be faster, more agile, and more successful. Let’s get talking!
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
How Can Your Business Benefit from Fog Computing?
How much data do we create every day? The World Economic Forum reports that the entire digital world is expected to reach 44 zettabytes by 2020. So, each day, we witness the colossal growth of data and this pace is only increasing with the growth of IoT. The agility and flexibility of big data applications are the foundation of the Internet of Things (IoT). The escalation of IoT has resulted in an increased volume of digitally generated data and managing that data has become a major challenge. This has led to the emergence of fog computing – an answer to the new challenges of computing technologies.
Read more: Gearing up for IoT in 2020
Defogging The Term Fog Computing
Let us start by defining it.
What is fog computing?
Fog computing is a decentralized computing infrastructure in which computing resources such as data, computers, storage, and applications are located between the data source and the cloud. This term refers to a new breed of applications and services related to data management and analysis.
According to Mung Chiang, Dean of the Purdue University, “fog provides the missing link for what data needs to be pushed to the cloud, and what can be analyzed locally, at the edge.” In simple terms, fog computing is a distributed network fabric that stretches from the outer edges of data creation to the point of storage.
Are fog computing and edge computing the same?
Edge computing is a subset or a component of fog computing. For example, if fog computing is compared to a basket of various fruits, edge computing would be one fruit from a single variety.
Edge computing refers to data being analyzed locally, at the point of creation. Fog computing encapsulates edge processing as well as the network connections required to bring that data from the edge (point of creation) to its endpoint.
Evidently, fog computing and edge computing are complementary.
Difference between fog computing and cloud computing
Just as the literal fog is a cloud closer to the ground, fog computing is stationed as a layer to reduce the latency in hybrid cloud scenarios. Cloud computing forms a comprehensive platform that helps businesses with the power to process important data and generate insights. Fog computing is like the express highway that supplies computing power to IoT devices which are not capable of doing it on their own.
Read more: Hybrid Cloud Infrastructure: How It Benefits Your Business
How Does Fog Computing Work?
Fog computing uses the concept of ‘fog nodes.’ These fog nodes are located closer to the data source and have higher processing and storage capabilities. Fog nodes can process the data far quicker than sending the request to the cloud for centralized processing.
The cloud is getting cluttered due to the enormous number of devices connecting to the internet. Since cloud computing is not viable in some cases, it has become necessary to use fog computing for IoT devices. It can handle the enormous data generated by these devices.
When implemented, fog-empowered devices locally analyze time-critical data that includes alarm status, device status, fault warnings, and so on. This minimizes latency and prevents major damage. Fog computing can effectively reduce the amount of bandwidth required, which in turn speeds up the communication with the cloud and various sensors.
Fog computing example:
If a user with a hand-held device wants to review the latest CCTV footage from a locally positioned IoT security camera, he would need to request the stream from the cloud since the camera does not have storage. This could take a bit of time, which can be eliminated with fog computing, where a local fog node can be accessed for video streaming which is far quicker.
Step-by-step Fog Computing Process:
- Signals are wired from IoT devices to an automation controller which executes a control system program to automate those devices.
- A control system program wires data through a protocol gateway.
- Data is converted into a protocol such as HTTP so that it can be understood easily by internet-based services.
- A fog node collects the data for further analysis.
- It filters the data and saves it for later use.
Read More: Fog Computing: The Catalyst For Efficient Data Processing
Key Takeaways for Your Business
- Increased business agility: It is evident that fog computing is cost-effective because it makes the production of revenue-generating products and services more efficient. It accelerates rollout cycles, broadens revenue bases, and reduces costs.
This revenue stream creates value for IoT fostering highly functioning internal business services. Fog computing also provides a common framework for seamless collaboration and communication helping OT and IT teams to work together to bring cloud capabilities closer.
- Privacy control: Fog computing facilitates better control of privacy because you can process and analyze sensitive data locally instead of sending it to a centralized cloud for analysis. It also enables the IT team to track, monitor, and control any device that collects or stores data.
- Data security: Since fog computing allows you to connect multiple devices to a network, it helps identify threats such as potential hacks, or malware. Additionally, such identified threats can be curbed at the device level without risking the entire network.
The Future is Fog Computing
Fog computing has several advantages over cloud computing. Fog computing can boost usability and accessibility in various computing environments. Soon, cloud computing for IoT may fade away but fog computing will take over. IoT is seeing an impressive growth rate and so it needs a special infrastructure base that can handle all its requirements. Fog computing is the key to accomplish this critical work. Reach out to Fingent, the leading custom software development company, and embark on a transformative journey for your business today.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
Facial Recognition Technology – What’s In Store For The Future
When Facebook started automatically tagging faces in uploaded images, nobody realized that this facial recognition technology would hike up to tracking people down while walking on the streets. In the past several years, this disruptive technology has gained immense popularity, that it is now used everywhere, from airports to shopping centers, to law enforcement. With its growing predominance in national safety and security, the face recognition market is estimated to reach USD 11.30 Billion by 2026.
“Facial recognition has been around for a long time—like the 1960s. Perhaps the father of facial recognition, Woodrow Wilson Bledsoe, an American mathematician and computer scientist who classified photos of faces all by hand, (RAND tablet), even he might have been alarmed at how facial recognition technology is supercharged today by advances in computing power, 5G speeds and AI paired with machine learning.”
– Tamara McCleary, CEO of Thulium, and a unique advisor to leading global technology companies such as SAP, Dell, Oracle, IBM.
Moreover, the advancements in artificial intelligence and machine learning are bringing about an active expansion to this technology. It won’t be long when the automation of facial recognition technology will fundamentally change the way we do many things. However, many minds still doubt on the path this revolution is leading to.
Let’s dig deeper into the advancements of the facial recognition technology, what it holds for the future and whether it’s completely safe to rely on such a disruptive technology that fiddles with personal identities.
Facial Recognition Technology In-Depth
So what is facial recognition technology and how exactly does it work?
Facial recognition is a biometric technology that utilizes unique facial features to recognize individuals. Today’s plethora of innumerable photos and videos make the dataset for this technology to work. Through artificial intelligence and machine learning capabilities, software mathematically maps distinguishable facial features, to compare patterns in newly available images with visual data stored in the database. Such a recognition process allows the simple unlocking of phones to security checks at airports.
In a way, artificial intelligence plays a vital role in the complete identity recognition process. A branch of artificial intelligence known as computer vision works through measuring nodal points on a face to make a face-print. This faceprint is a unique code that is applicable only to a particular person. This enables identification.
“I believe AI in Facial Recognition could add great value to society but we have to be careful to use clean data and we have to educate the public for the need for good, clean, accurate data to be sure we do not accidentally disenfranchise certain groups even more in the future. We must assure the data does not include unconscious bias or even deliberate bias programmed into the code. It is also important to note that we have a major lack of data for many disenfranchised groups including the community of persons with disabilities.”
– Debra Ruh, CEO, Ruh Global IMPACT, Global Disability, and Aging Inclusion Strategist.
Once this faceprint is made, the technology runs through an identity database to match this face with a name and other required details. Thus, the probability of error is near to rare; maybe an eight out of 1000 scans could mistakenly identify the person. This is what makes this technology an excellent prospect for performing crucial functions.
Read more: How Fingent helped develop a unique mixed reality application for a leading university to identify people using facial recognition
Innovative Uses Of Facial Recognition Technology
As facial recognition technology evolves with time, few industries and countries apply the technology in innovative ways.
China is rising to be the leader in facial recognition technology. Although part of the technology remains a perspective, its innovative use is what amazes the audience. A few other countries following the trend are Japan and the United Arab Emirates. The US doesn’t stand back either. Look at these impressive ways of face recognition technology implementation.
- Face recognition is on its go, replacing cash and credit cards. At fast-food units like KFC, customers can just smile into a self-serve screen to automate the identification and withdrawal of cash from banks. Some banks are also allowing customers to use face recognition instead of bank cards.
- The automobile brand Subaru has integrated facial recognition cameras to its Forester brand of SUVs. This is intended to detect when a driver is tired or about to sleep to take necessary actions to prevent accidents. This indeed is a tremendous innovation towards road safety.
- The 2020 Tokyo Olympics, is reported to make use of facial recognition to boost their security systems. Instead of relying on ID cards that have a high probability of being fake, the authorization is now implementing the FR technology to allow media, competitors or other such people to enter the premises.
- Dubai Airport also makes use of the FR technology to strengthen their security. A virtual aquarium fitted with 80 facial recognition cameras examines every passerby to easily recognize criminals or offenders. Also, police cars are on their go-to implement FR cameras to identify criminals and wanted vehicles quickly.
- Facial recognition technology is no doubt making a great impact on national security systems, promising a safe and crime-free future. The US government is also making use of biometric exits and AI cameras to track people crossing their international boundaries without proper documents.
The Growing Concern
Though face recognition technology offers innovative and impressive use cases in security and surveillance, there are numerous challenges that it faces. Privacy being a major concern, not everybody is happy with the storage of sensitive and personal data. A potential downside of this technology is the data and privacy breaches. The databases containing facial scans and identities are being used by multiple parties such as banks, police forces, and other defense firms and are hence prone to misuse.
Considering the face recognition tech as a threat to their citizens’ privacy, many cities including San Francisco, Massachusetts, Cambridge, and others are planning to put a complete ban on real-time face recognition surveillance.
“Concerns around AI’s practical applications like facial recognition have begun crystallizing over the last few years and will continue unabated. Current AI-based face recognition systems possess a grave threat to individual privacy, which if unregulated may end up jeopardizing sensitive user data to the wrong hands in times to come.”
– Varghese Samuel, CEO & MD Fingent.
Moreover, how much can this technology eliminate crime is still being discussed. The accuracy of the system in detecting people who cover their faces from cameras or disguise themselves is yet a topic of dispute. However, to everyone’s relief, the technology is showing constant improvement in this matter. According to the U.S. National Institute of Standards and Technology (NIST), facial recognition systems got 20 times better at finding a match in a database over a period that covered 2014 to 2018.
“Artificial intelligence has made great strides, but still has a long way to go. It is powerful to use on a daily basis, when the stakes are low (for example, in tagging photos or recommending advertisements), but not yet trustworthy enough to stand fully on its own in high-stakes applications, such as driverless cars, medical diagnosis, and face recognition, where errors can deeply affect people’s lives.
– Gary Marcus, Founder and CEO, Robust.AI Professor Emeritus, New York University, Author of book: REBOOTING AI
The Untold Future
It is pretty much tough to predict where the facial recognition technology would be in the coming years, but the increase in AI advancements is sure to widespread this technology around the globe. Major industries have already capacitated the FR capabilities to replace the traditional process of paying bills, opening bank accounts, checking controls at airports, and such. A few of these industries include healthcare, retail, marketing, and social media platforms.
In a nutshell, face recognition technology is expected to predominate the globe in the near future. The increasing usage of mobile devices and demand for robust fraud detection and prevention is predicted to majorly drive the implementation of this technology. As per the predictions made by Markets and Markets, a prominent research firm, the global facial recognition market size is expected to grow from USD 3.2 billion in 2019 to USD 7.0 billion by 2024, at a Compound Annual Growth Rate (CAGR) of 16.6% during 2019–2024.
“The more people grow accustomed to using facial recognition products and services that enhance efficiency and that can, at the moment, seem altogether too fun or mundane to be harmful — whether it’s tagging photos, unlocking a phone, or projecting how your face might look in the future — the more facial recognition technology becomes normalized.”
– Jarno M. Koponen, Head of AI & Personalization at Yle News Lab. His work has been covered by The New York Times, New Scientist, Oxford Reuters Institute, Mashable, TechCrunch.
Face recognition technology is revolutionizing the world more than you think. It’s time to figure out how this technology could bring added value to your firm. Contact our custom software development experts today!
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
6 Chatbot Security Practices You Need To Implement
According to a survey by Oracle, regarding the benefits of using chatbots for their consumer-facing products, which included responses from 800 decision-makers, including chief marketing officers, chief strategy officers, senior marketers, and senior sales executives from France, the Netherlands, South Africa, and the UK, it was found out that “80 percent of companies wanted to have some type of chatbots implemented by 2020!
It is also forecasted that 90% of bank-related interactions will be automated by 2022. Moreover, 80% of businesses will have chatbot automation implemented by 2020. Also, 47% of consumers would buy items from a chatbot when 28% of top-performing companies are already using AI for marketing! With chatbots turning into the trend, it is vital to implement chatbot security measures.
A Back Door Open To Hackers
Chatbots are nowadays mostly used in industries such as retail, banking, financial services, and travel that handles very crucial data such as credit/debit cards, SSN, bank accounts, and other Sensitive PII (Personally identifiable information).
The aggregation of such data is crucial for the chatbot to perform. Thus, it is required that chatbots are not vulnerable to be exploited by any hackers.
A recently released report from MIT Technology Review and Genesys showed that 90% of companies are already using AI strategies to increase revenue. The research also found that on average, between 25% and 50% of all customer queries can be solved through automated techniques. This has made it easier than before to handle complex tasks.
Related Reading: Read on to know more about the top AI trends of 2019.
The HTTPS Protocol For Security Of Chatbots
HTTPS protocol is the basic and default setting required for a good security system. The data that is being transferred over the HTTP via encrypted connections are secured by Transport Layer Security (TLS) or Secure Sockets Layer (SSL).
Related Reading: Check out how Fingent helped create an enhanced and engaging learning experience through chatbots.
Types of Security Issues
Security Issues fall into two main categories:
-
Threats
Threats are usually defined as different methods by which a system can be negotiated or compromised. Threats can include incidents such as Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privileges, and many other threats.
-
Vulnerabilities
Vulnerabilities are defined as methods that a system is compromised and cannot be identified and solved correctly and on time. A system becomes open to attack when it has poor coding, lax security, or because of human errors. The most effective way to solve the issues of a possible vulnerability is to implement SDL (Security Development Lifecycle) activities into the development and deployment methods.
As per the study by the Ponemon Institute, In 2017, the average total cost of a successful cyber-attack was over $5 million, or $301 per employee!
Here are 6 chatbot security issues that you need to consider right away:
1. Encryption
Data while transit can also be misused. There exist different protocols that provide encryption, while addressing these problems of misuse and tampering.
According to article 32 (a) of the General Data Protection Regulation (GDPR), “it is specifically required that companies take measures to de-identify and encrypt personal data. So, chatbots have access only to encrypted channels and communicate through those”.
For instance, Facebook Messenger introduced the new feature called “Secret Conversations” that enabled end-to-end encryption based on Signal Protocol.
2. Authentication and Authorization
Authentication is performed when the user needs to verify their identity. This is often used for bank chatbots.
Generated authentication tokens verify data that are requested through a chatbot. On completing the verification of the user’s identity, the Application produces a secure authentication token, along with the request.
Another step of security measures is an authentication timeout. The token generated is used for only a certain amount of time, after which the application has to process a new one.
Two-way verification is another process where the user is asked to authorize their email address or to receive a code via SMS. This is a crucial process which is necessary to verify that the user of that account is the real user that is using the chatbot.
3. Self-destructing Messages
When Sensitive PII (Personally identifiable information) is being transferred, the message with this data is deleted after a definite period of time.
Personally identifiable information (PII) is any data which can be used to identify a particular person. It includes records such as a person’s medical, educational, financial and employment information. Examples of data elements that can identify and locate an individual include their name, fingerprints or other biometric (including genetic) data, email address, telephone number or even their social security number.
This kind of security measure is crucial when working with banking and other financial chatbots.
4. Personal Scan
When working with personal data, it is necessary to take security precautions and measures.
Apple was the first company that added finger authentication to their iPhones. This technology is now being used widely to verify an individual’s identity. This is performed when initiating a transaction or when you want to access your bank account using a chatbot that a personal scan is required.
5. Data Storage
Chatbots are effective because they retrieve and store information from users.
For instance, if you have a chatbot that performs online payments, this can mean that your clients are providing their financial information to a chatbot.
The best solution in this situation is to store such information in a secure state for a required amount of time and to discard these data later on.
Some other concerns are the following:
- Biometric authentication: Iris scans and fingerprint scans are popular and robust.
- User ID: User IDs involve processing secure login credentials.
- Authentication Timeouts: A ‘ticking clock’ for correct authentication input. This prevents giving hackers an opportunity to guess more passwords.
- Other strategies could include 2FA, behavior analytics, and kudos to the ever-evolving AI trends.
6. Tackling Human Causes
The one and only other factor or cause that cannot be altered is the human factor. With commercial applications in specific, that chatbot security and end-user technique have to be resolved. This will ensure the chatbots from being vulnerable to threats.
Related Reading: Find how artificial intelligence can drive business value.
To know more about secure bot building, get in touch with our software development experts today!
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new



Talk To Our Experts
What seemed to be a far-fetched idea or an unclear, undefined entity, a few years ago, is what is ruling the world of business today. Enterprise mobility.
People are all for the concept of “bringing their own devices” at their workplaces these days. More than 60% of workers have access to their company data or work through their smartphones and tablets. Interestingly, only about a third of business enterprises have any kind of BYOD (Bring-Your-Own-Device) management strategy in place.
“People are bringing their own devices, but in many cases, they and their companies are not taking care of those devices and the applications on them appropriately.”, says Richard Absalom, consumer impact technology analyst at Ovum.
It is very important to have a proper Enterprise Mobility Management strategy for every organization, especially since most of them are spending a pretty significant amount on mobility.
Here is what you can do to better manage enterprise mobility.
Involving Everyone
Any BYOD policy has to be developed with inputs from all over the organization. Driven by the CIO, BYOD management efforts should involve everyone from developers to users to the IT team. Even the human resource and legal departments have to be included. As it means an entire culture change in the organization, it necessitates the need for everyone to be on the same page, about what can and cannot be accessed over personal devices.
Smartphone Technologies

An Exit or Loss Policy
While devising BYOD policies, something that people generally tend to miss out, is an exit strategy. When an employee in any department of an organization leaves, he will be carrying a lot of information concerning his department on his smartphone, with him. This is a huge loss for the organization.
“When an employee leaves, say in sales, and they take all of the contacts on their personal phone, that is a big corporate asset that goes missing.”- Absalom
Hence, you need to develop appropriate theft, loss as well as exit policies. Along with technical issues you need to raise the security stakes. You need to find a balance with all these features and risks, so as to protect your employees’ personal information as well as your business reputation.
Insecure WiFi

User Credentials
Credentials for users, such as usernames and passwords, need to be created securely with utmost care. Credentials which may be sufficient for certain kinds of applications may not be suitable for other kinds of applications that need more security. Short number strings for example,while may be appropriate authentication for a user on game leaderboards and scoreboards, they won’t be enough for a social networking application.
All of these practices call for crisp and clear policy guidelines. Their compliance needs to be made mandatory as well. You need to make sure that all your employees are well aware of the rules regarding joining, leaving or altering their role or participation in a BYOD initiative. Signatures on policy agreements need to be made compulsory. Absalom also said that it would be good to have all employees agree to legally upholding their policies and to getting their devices locked on events of it being stolen, lost or compromised in any way.
Hence, if well managed, enterprise mobility can be the best thing that ever happened to your business. Keep the above pointers in mind, embrace mobility and manage it efficiently.
Stay up to date on what's new

Featured Blogs
Stay up to date on
what's new